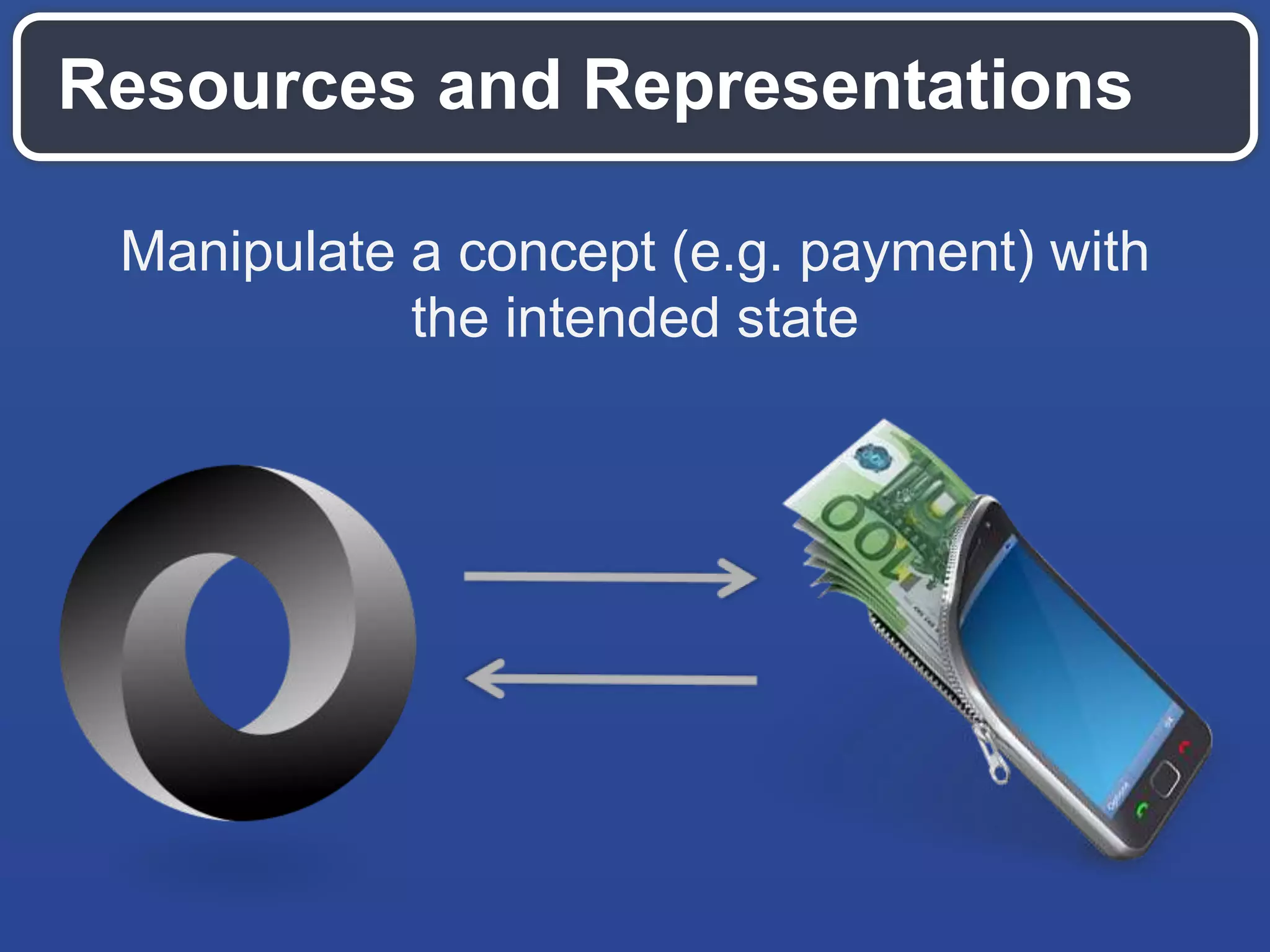
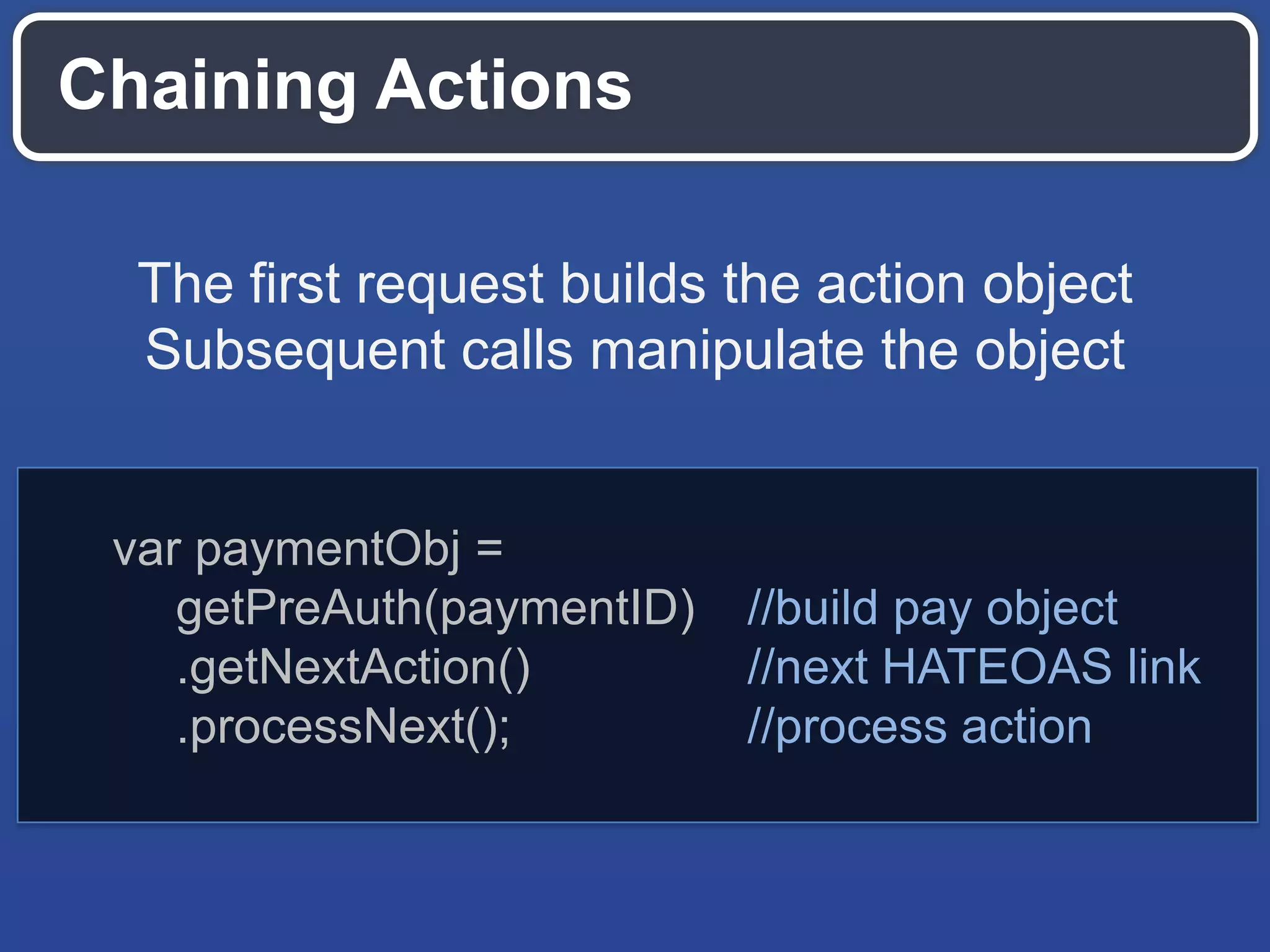
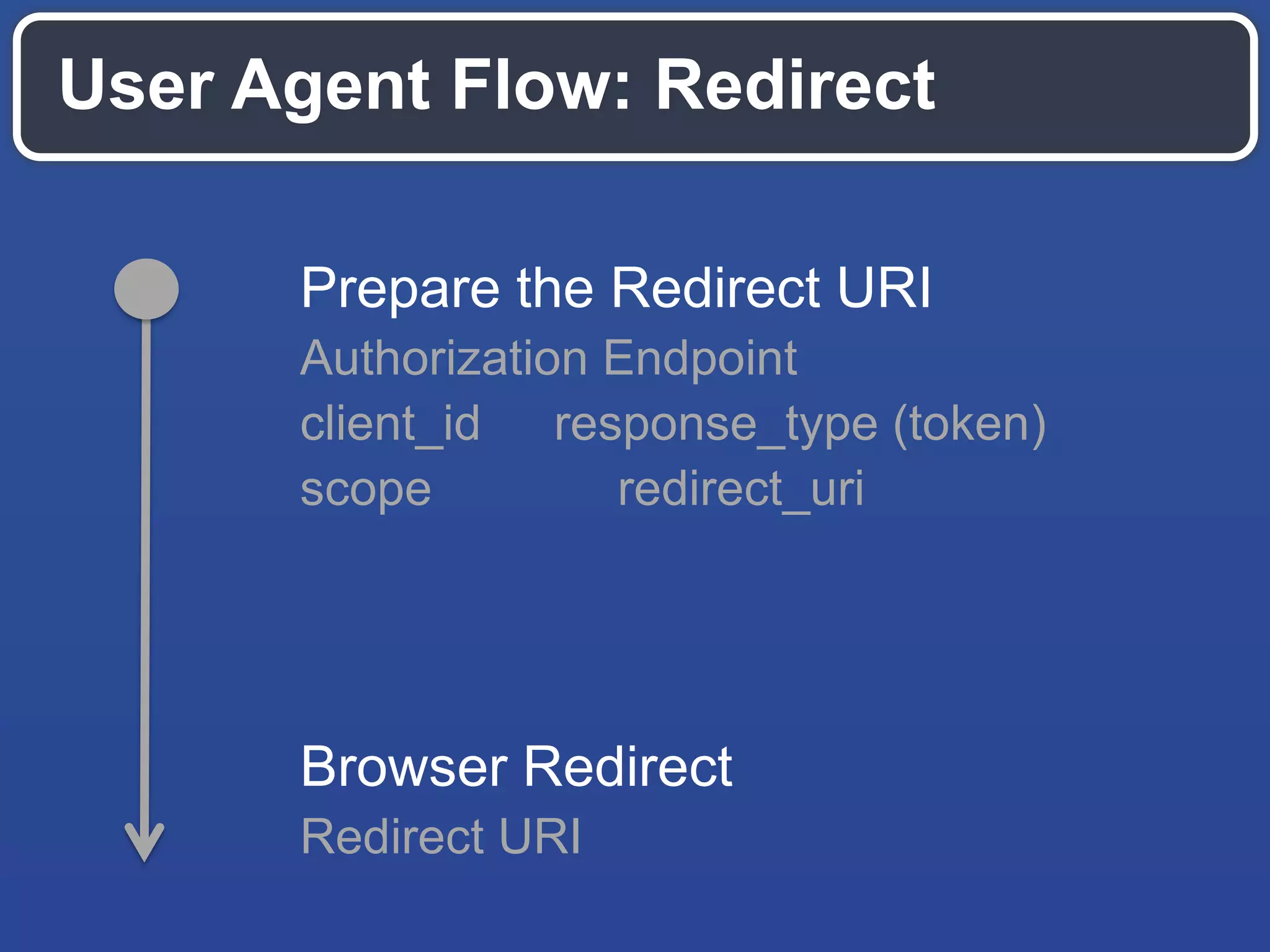
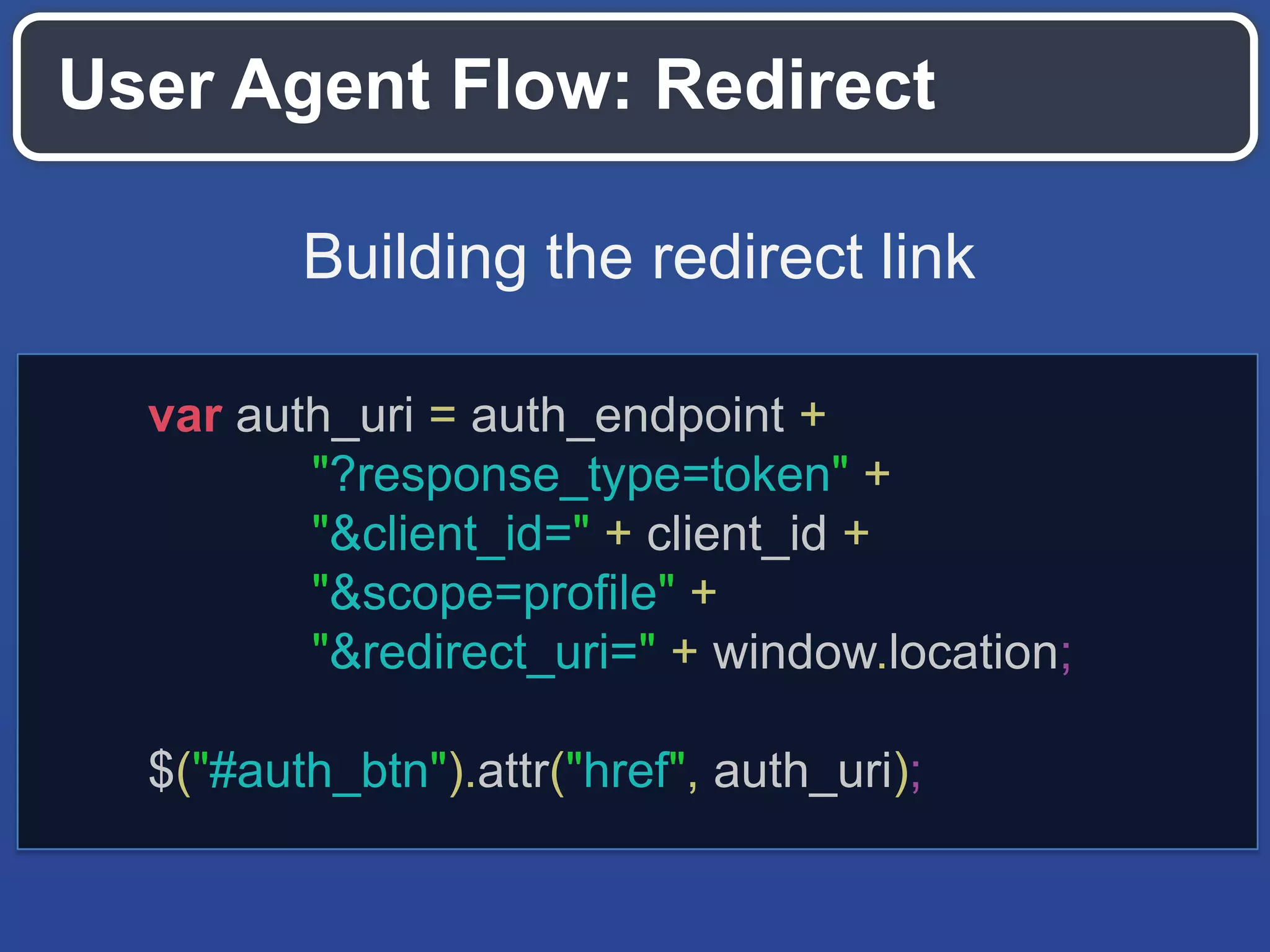
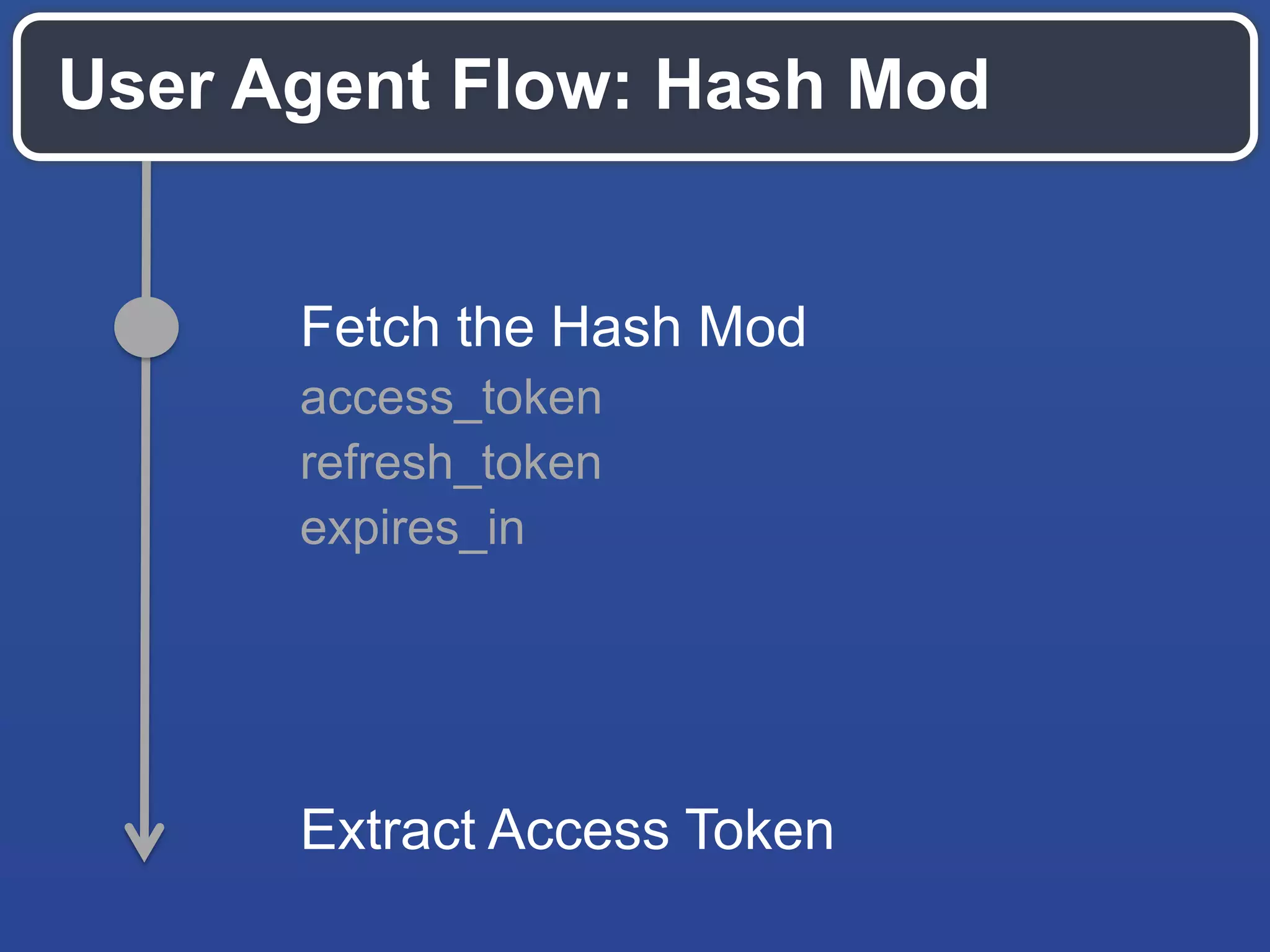
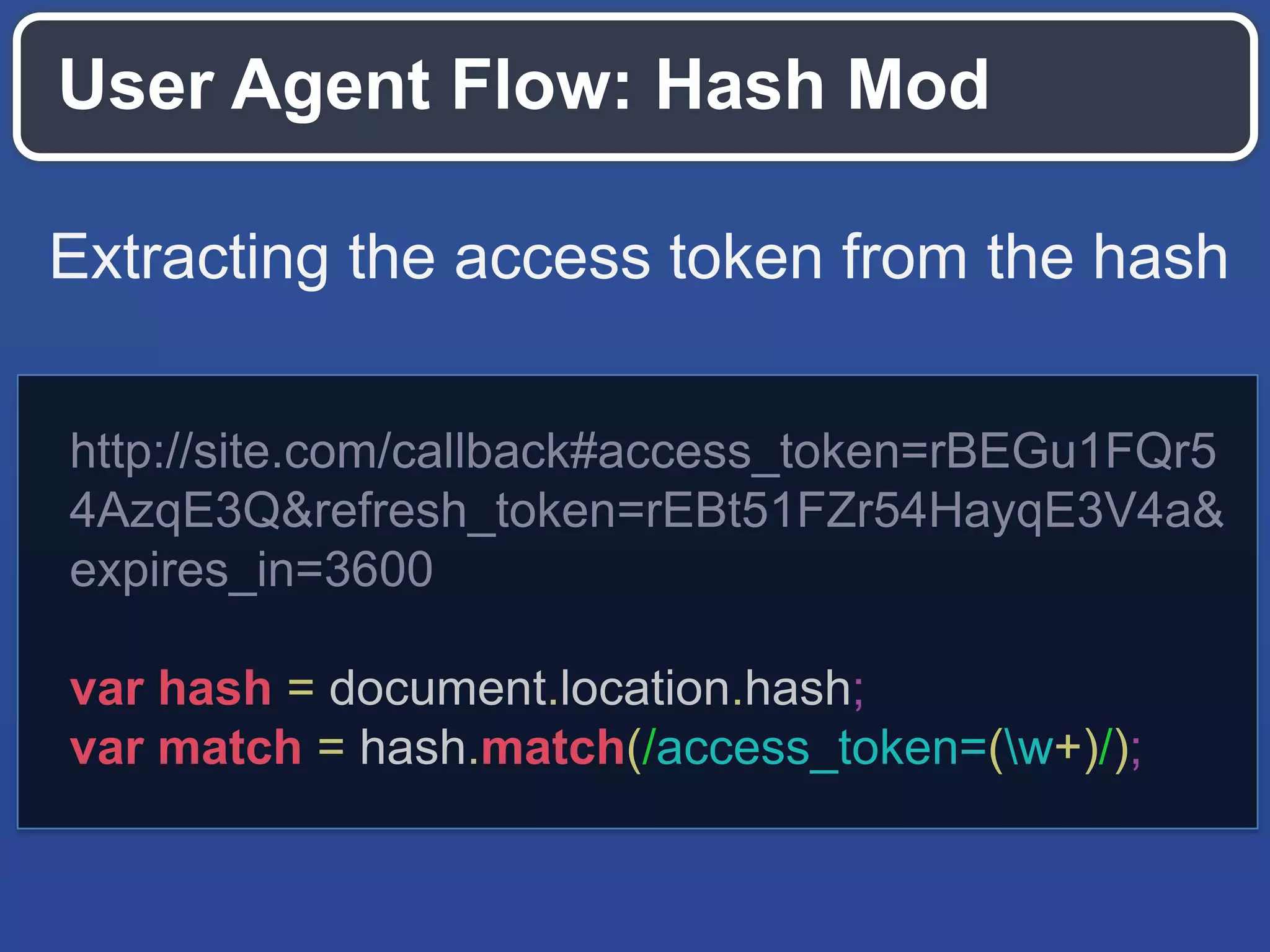
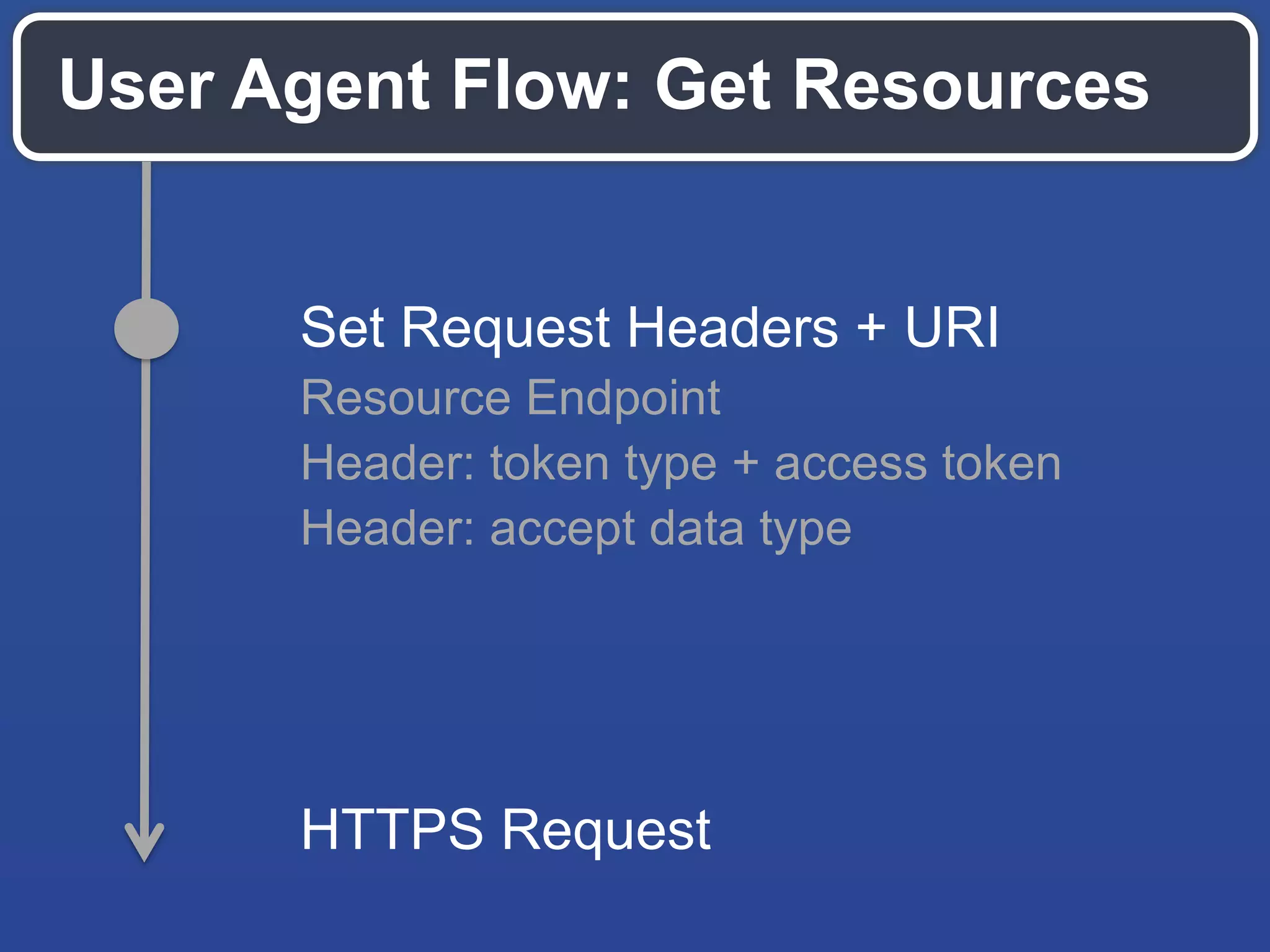
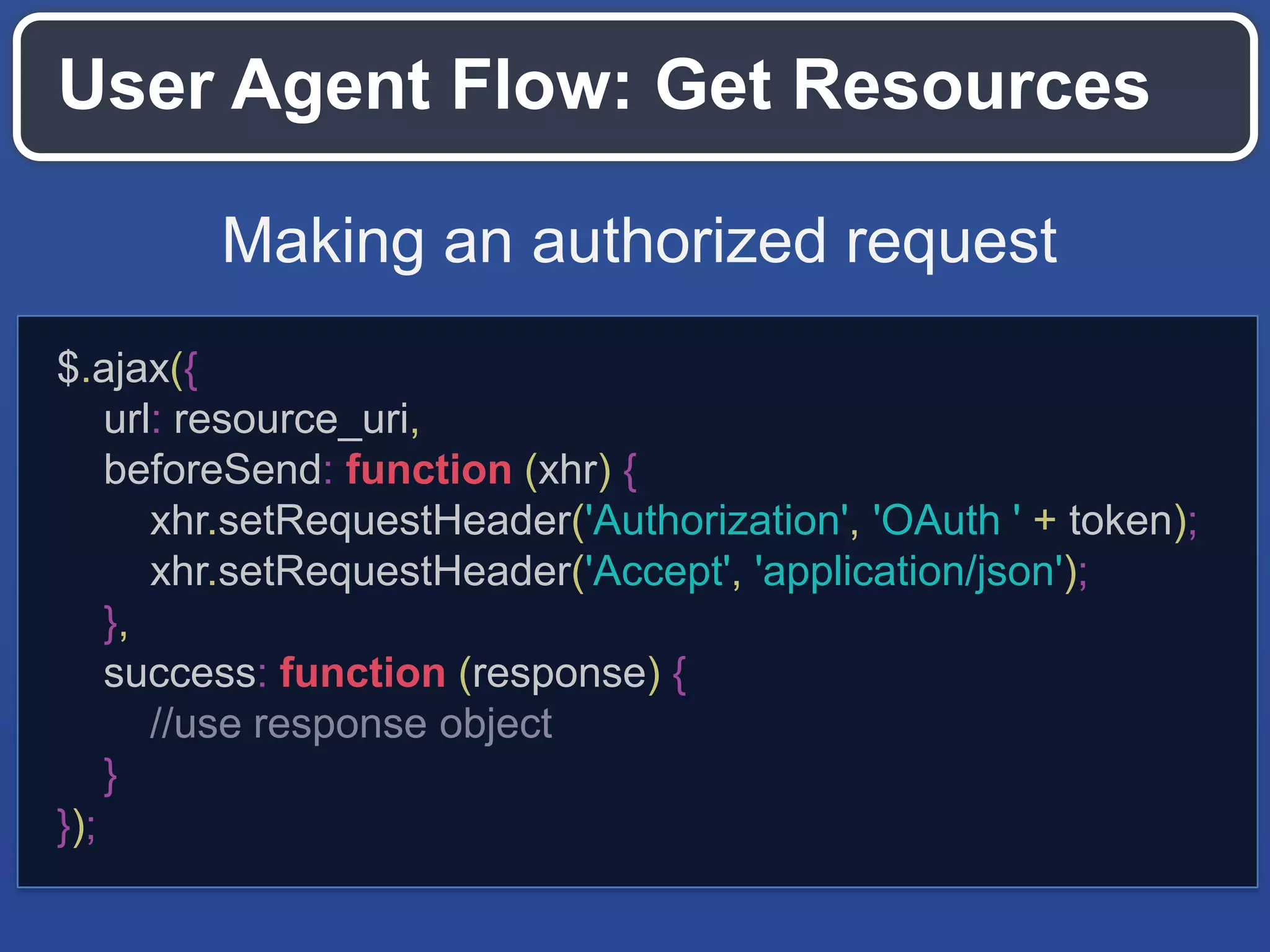
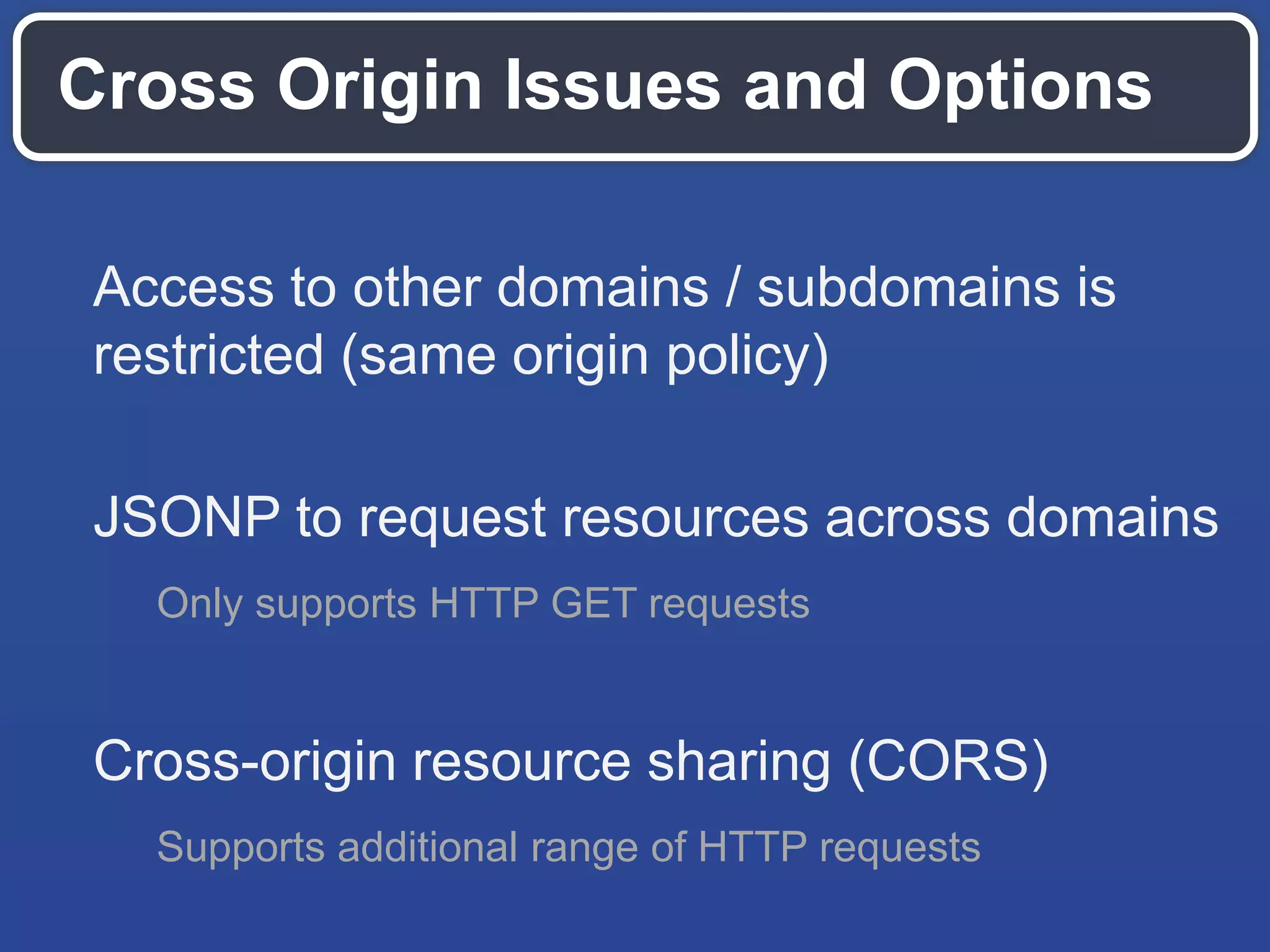
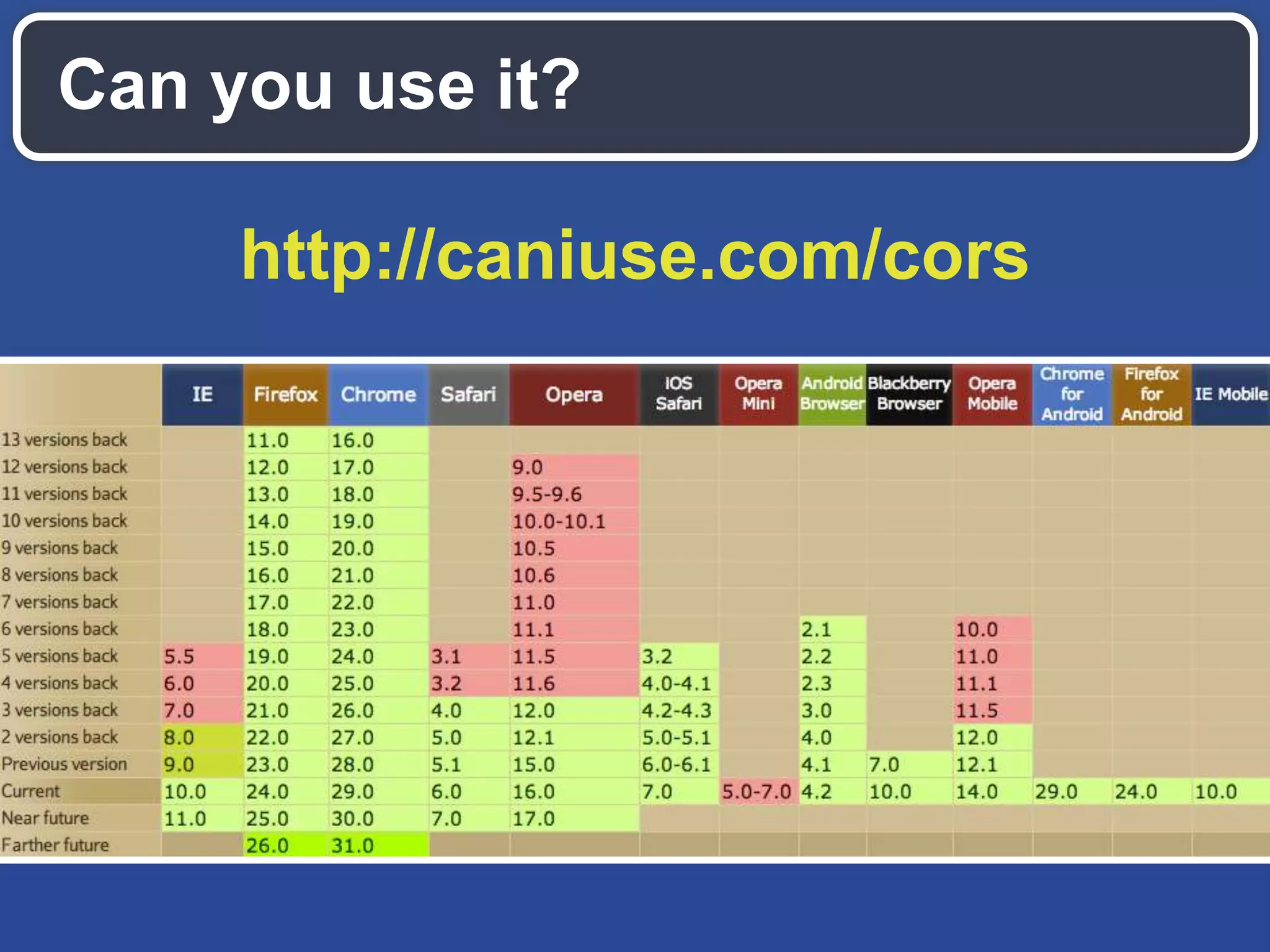
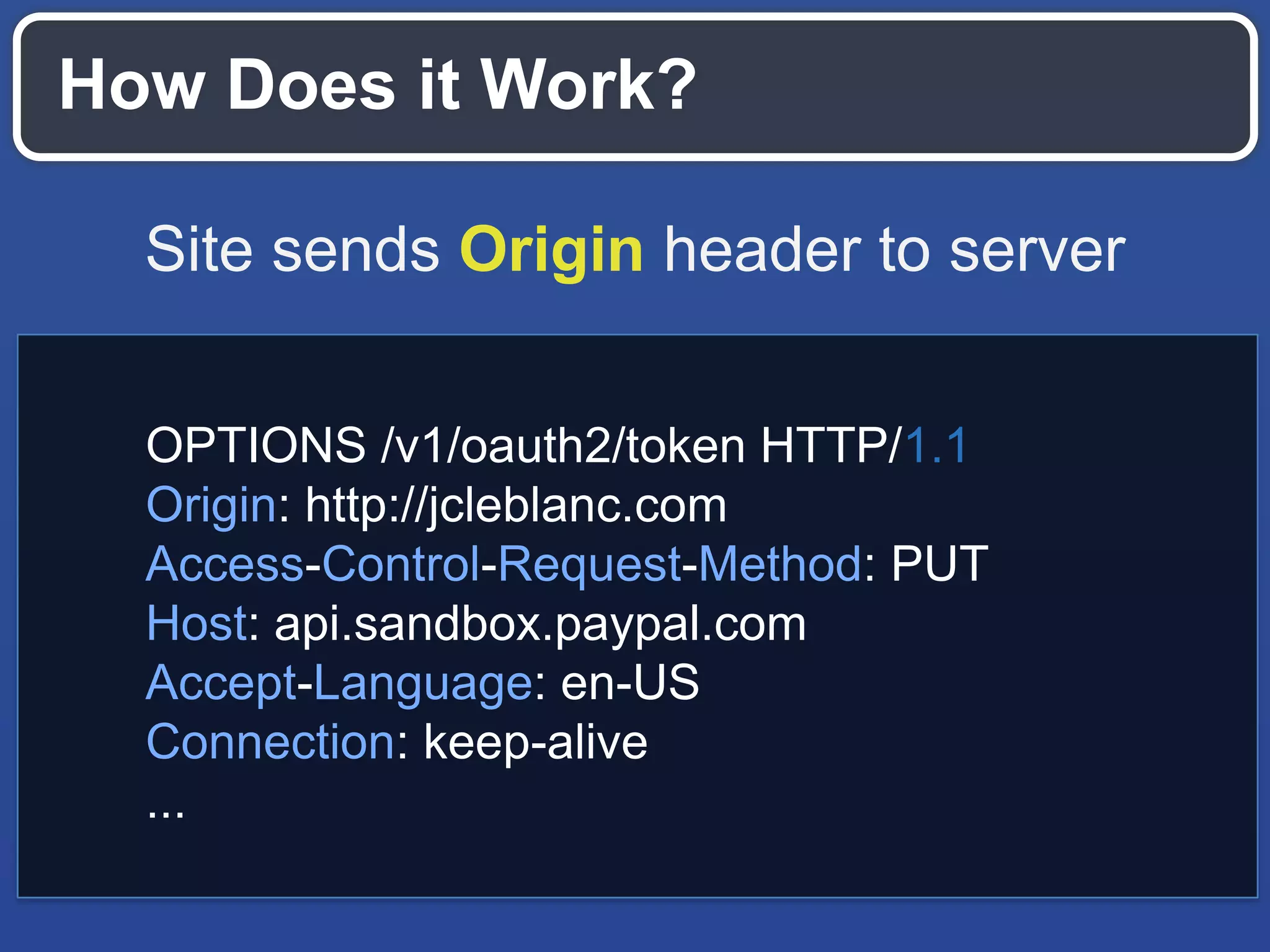
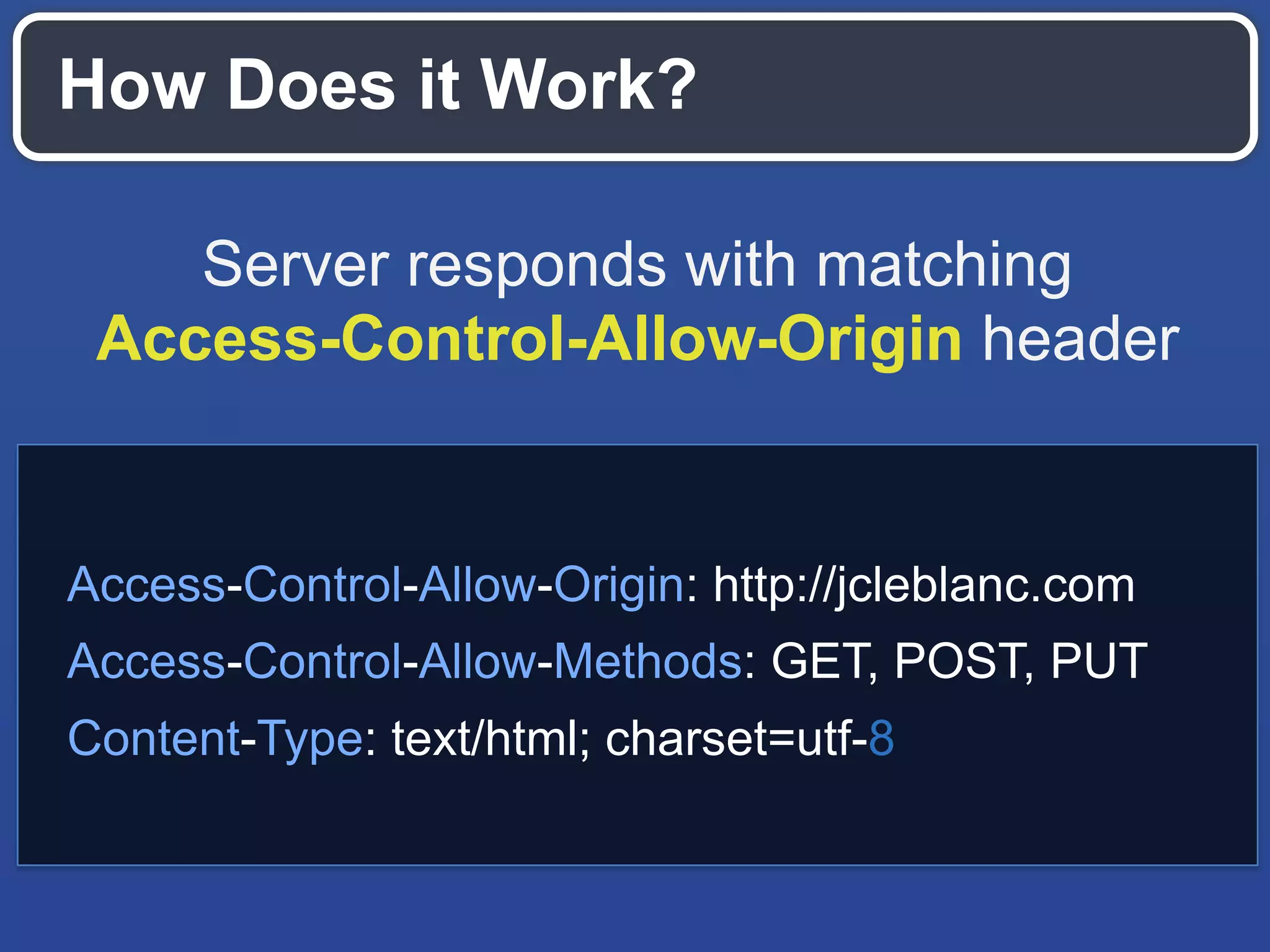
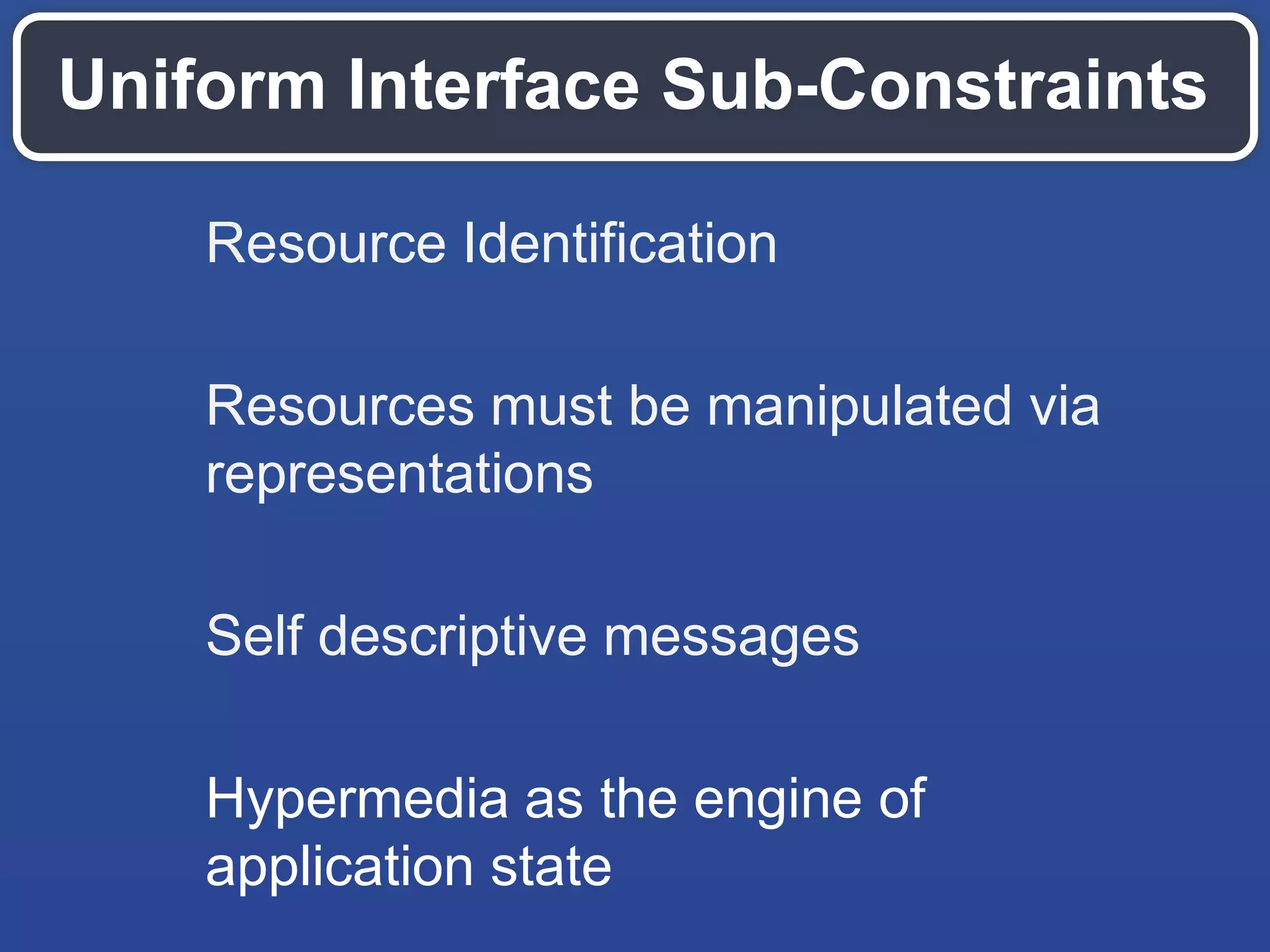
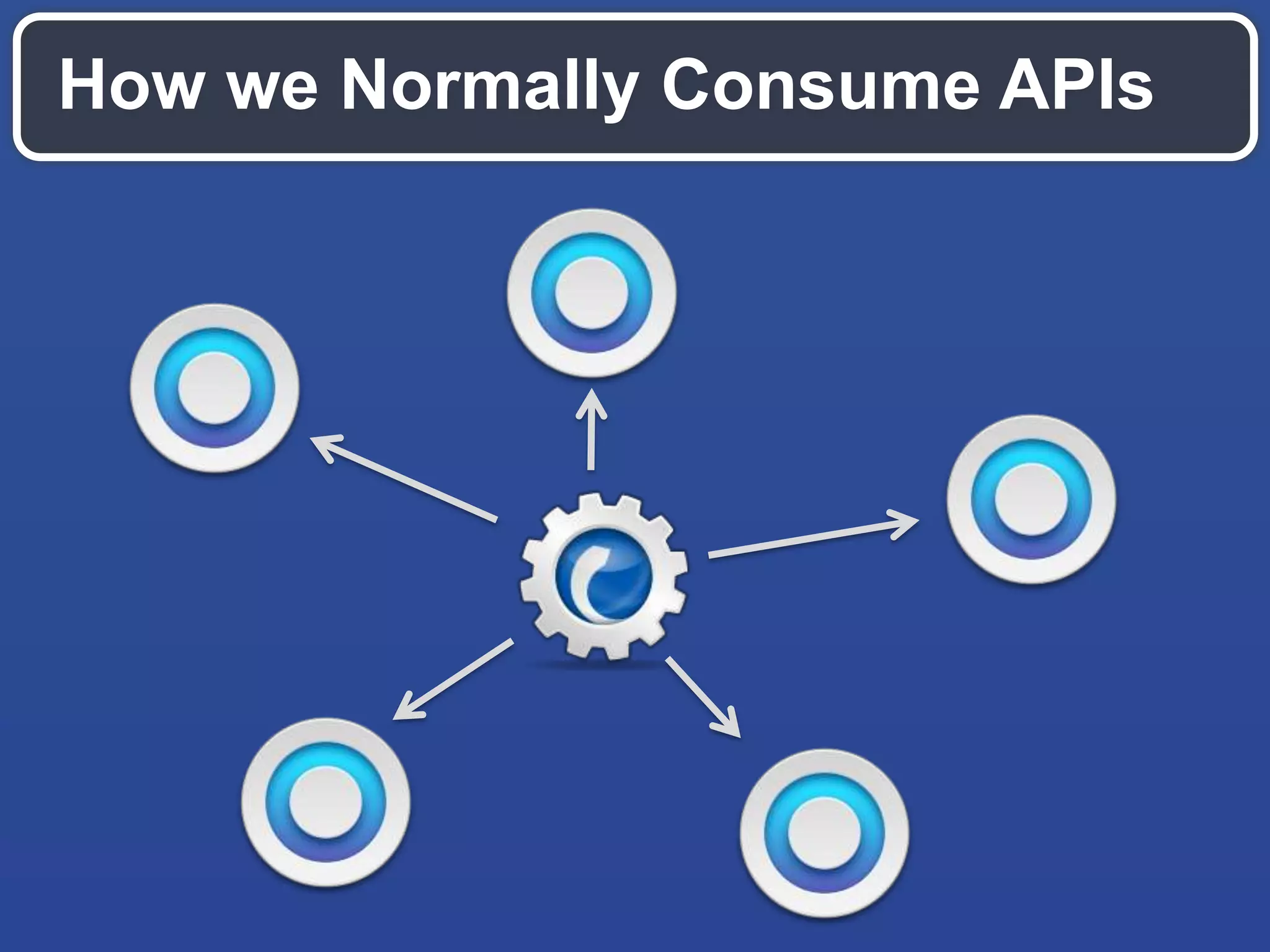
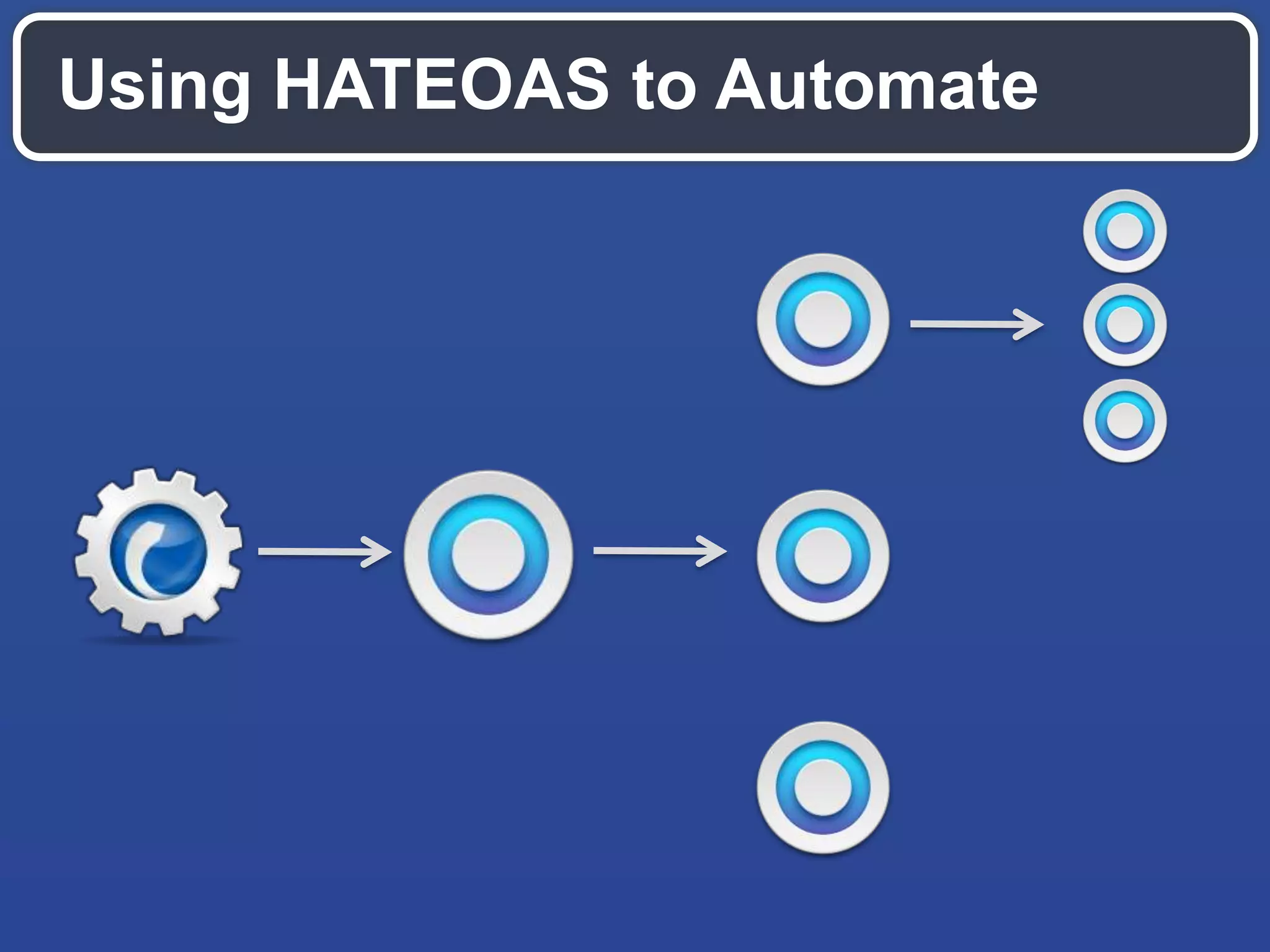
The document outlines best practices for secure RESTful API automation using JavaScript, emphasizing the challenges posed by the same-origin policy and the importance of securing private keys. It discusses user agent flows for OAuth 2, methods for handling CORS, and automation strategies using HATEOAS to streamline API interactions through stateless resource manipulation. Ultimately, it highlights the necessity of building systems that facilitate developer automation while ensuring security compliance.










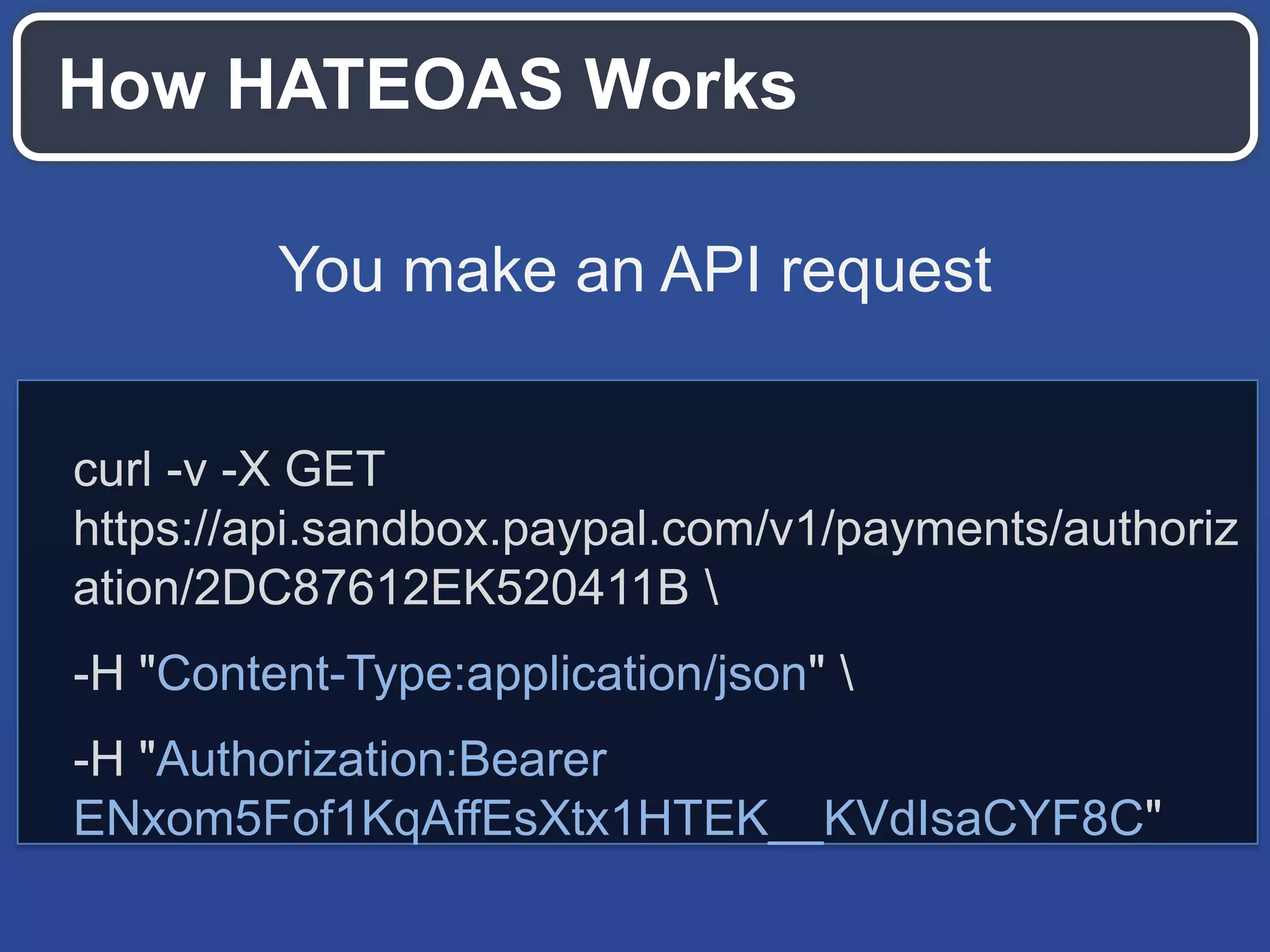
!["links": [ { "href":"https://api.sandbox.paypal.com/v1/payments/ authorization/6H149011U8307001M", "rel":"self", "method":"GET" },{ "href":"https://api.sandbox.paypal.com/v1/payments/ authorization/6H149011U8307001M/capture", "rel":"capture", "method":"POST" },{ "href":"https://api.sandbox.paypal.com/v1/payments/ authorization/6H149011U8307001M/void", "rel":"void", "method":"POST" } ]](https://image.slidesharecdn.com/2013octhtml5devconfrestjavascript-131018193611-phpapp02/75/Secure-RESTful-API-Automation-With-JavaScript-33-2048.jpg)
![Interactions Should be Stateless Send enough detail to not have to make another request to the API { "id": "PAY-17S8410768582940NKEE66EQ", "create_time": "2013-01-31T04:12:02Z", "update_time": "2013-01-31T04:12:04Z", "state": "approved", "intent": "sale", "payer": {...}, "transactions": [{...}], "links": [{...}] }](https://image.slidesharecdn.com/2013octhtml5devconfrestjavascript-131018193611-phpapp02/75/Secure-RESTful-API-Automation-With-JavaScript-35-2048.jpg)