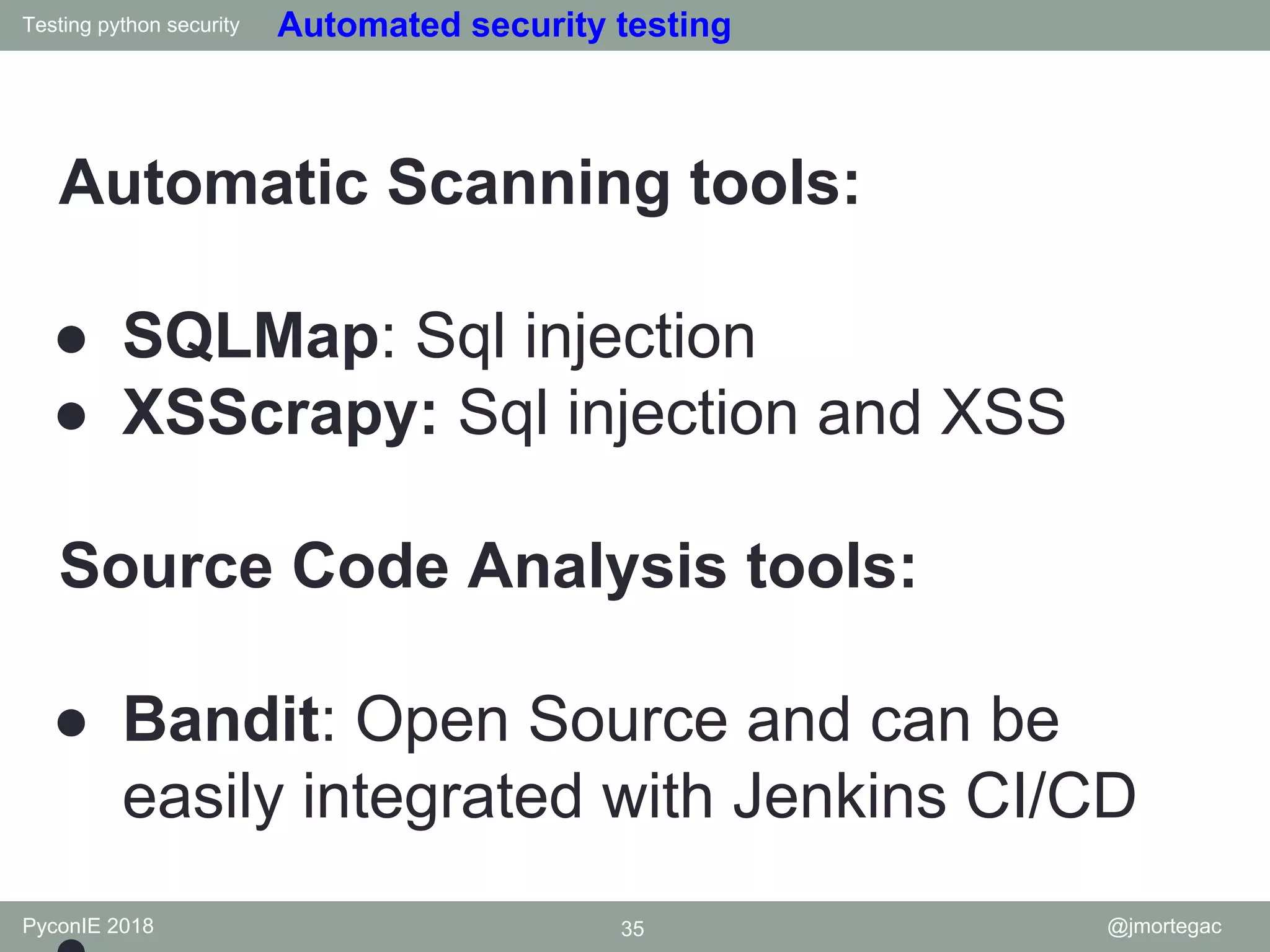
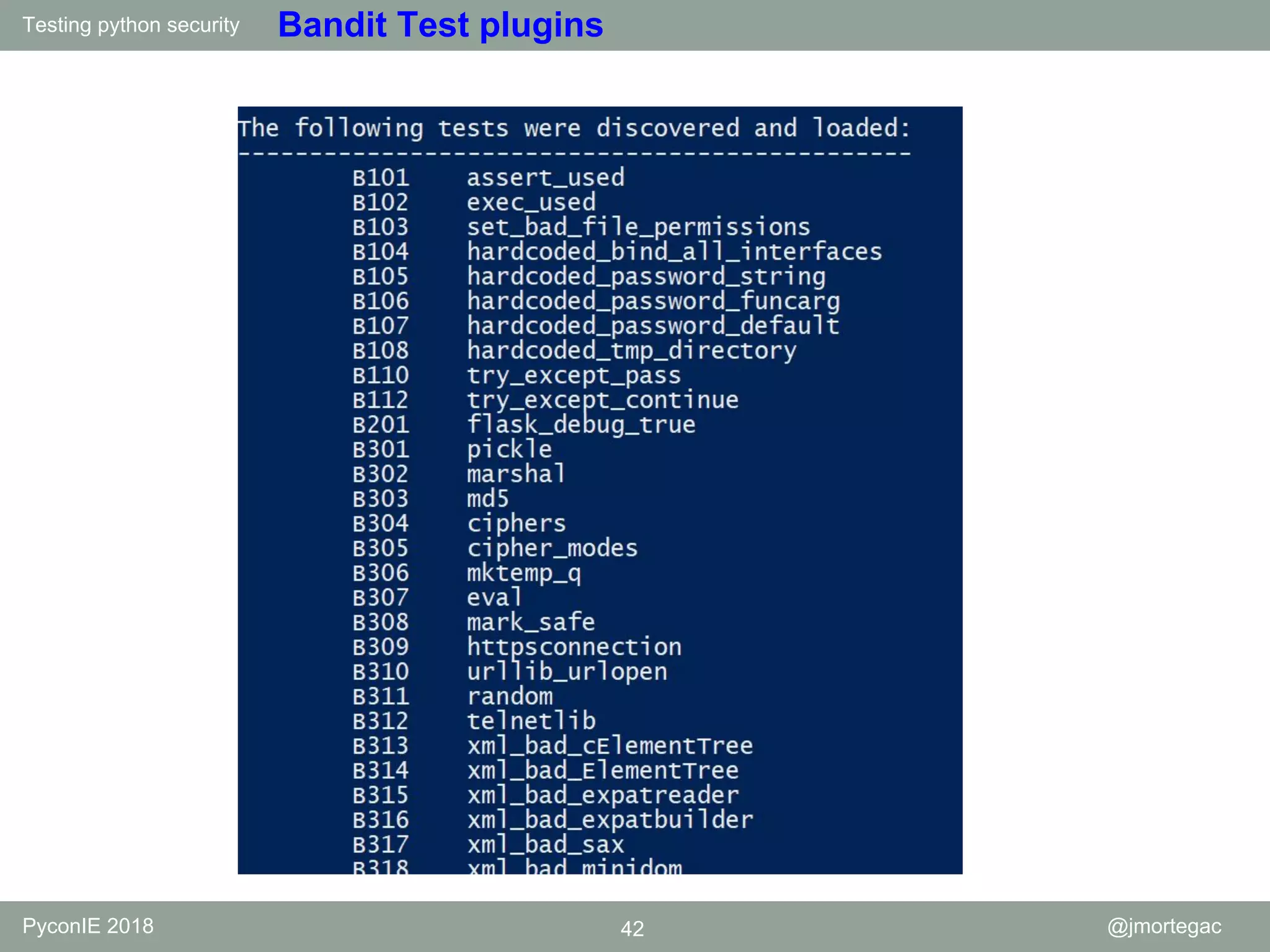
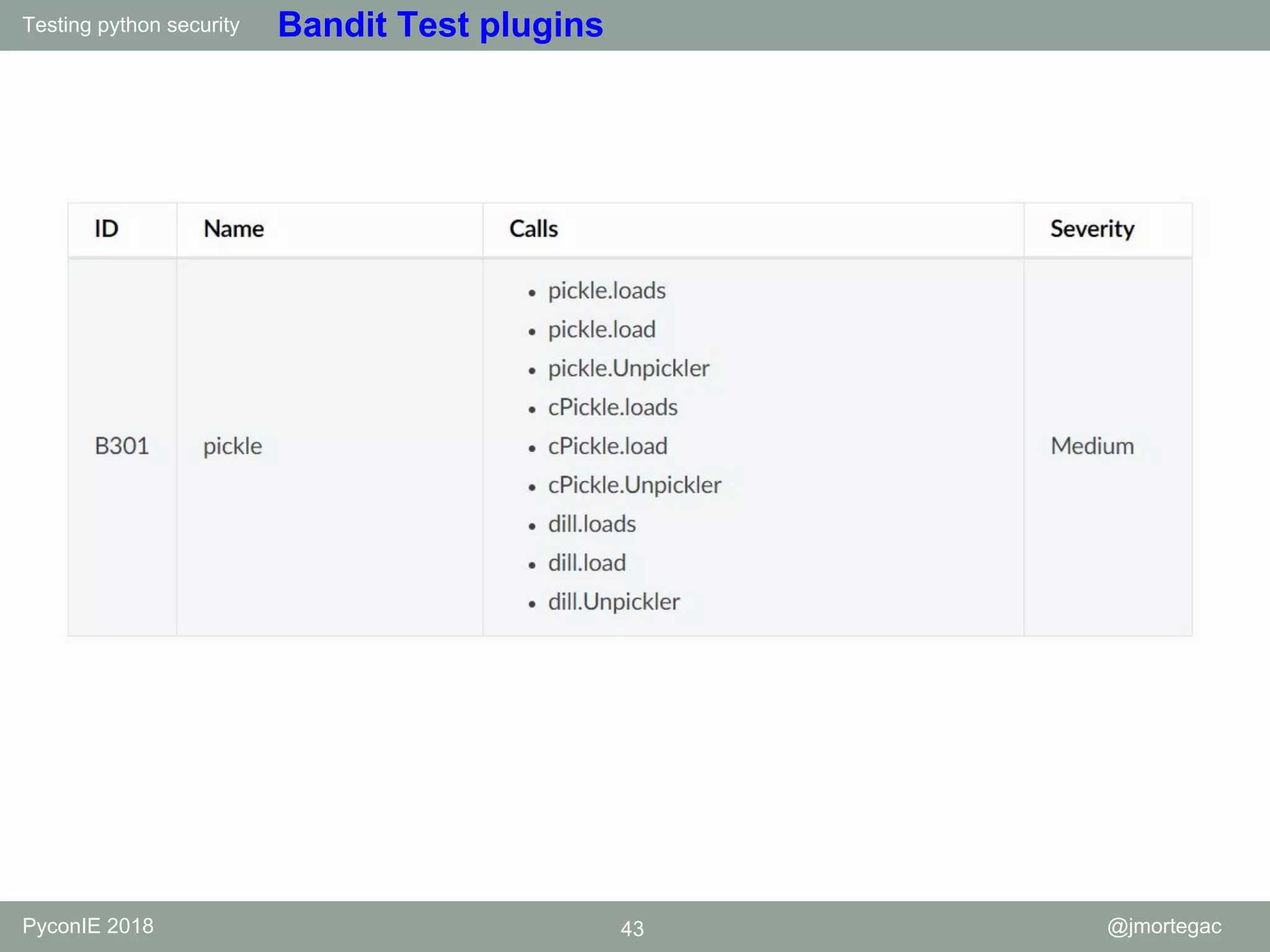
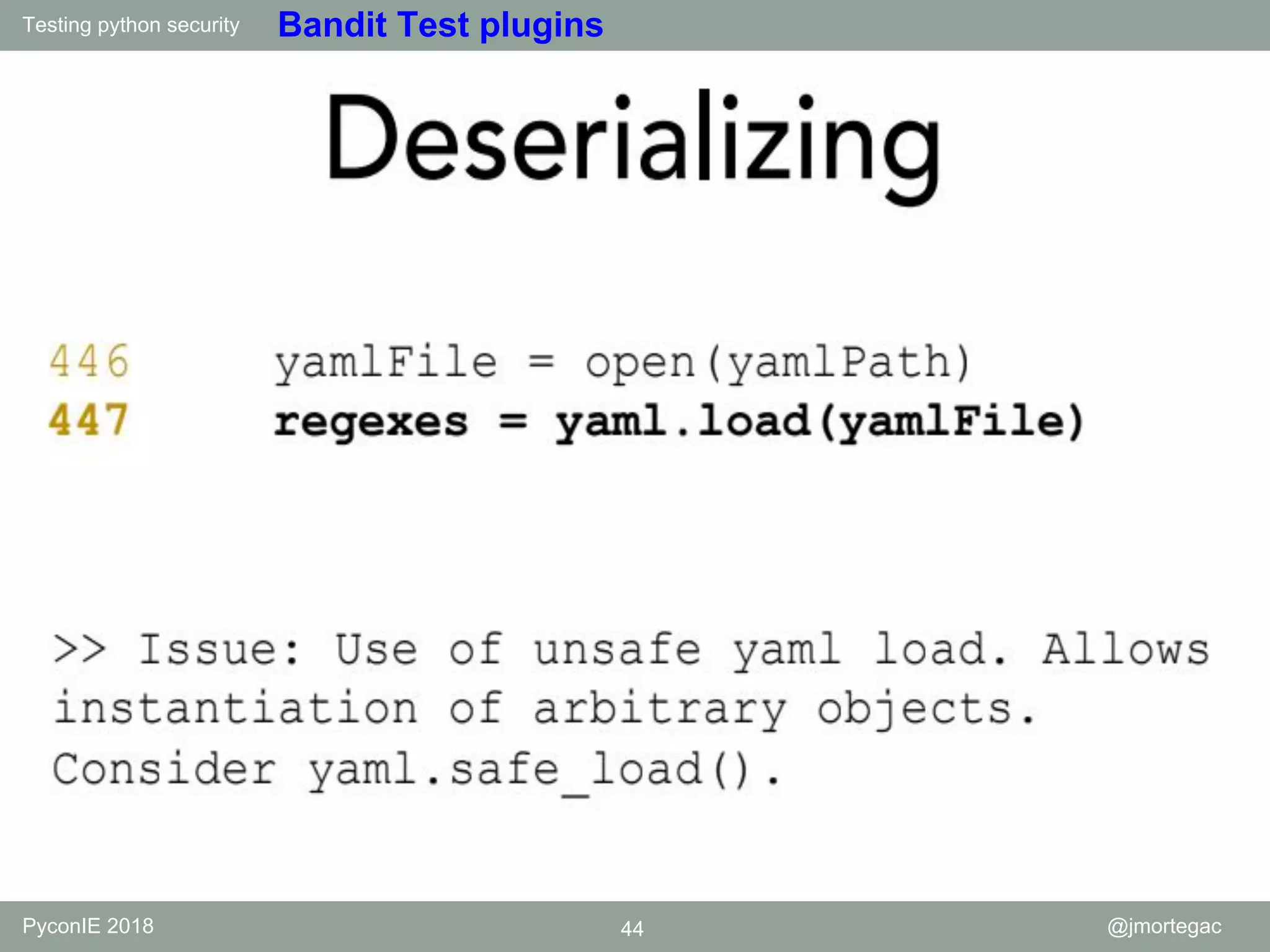
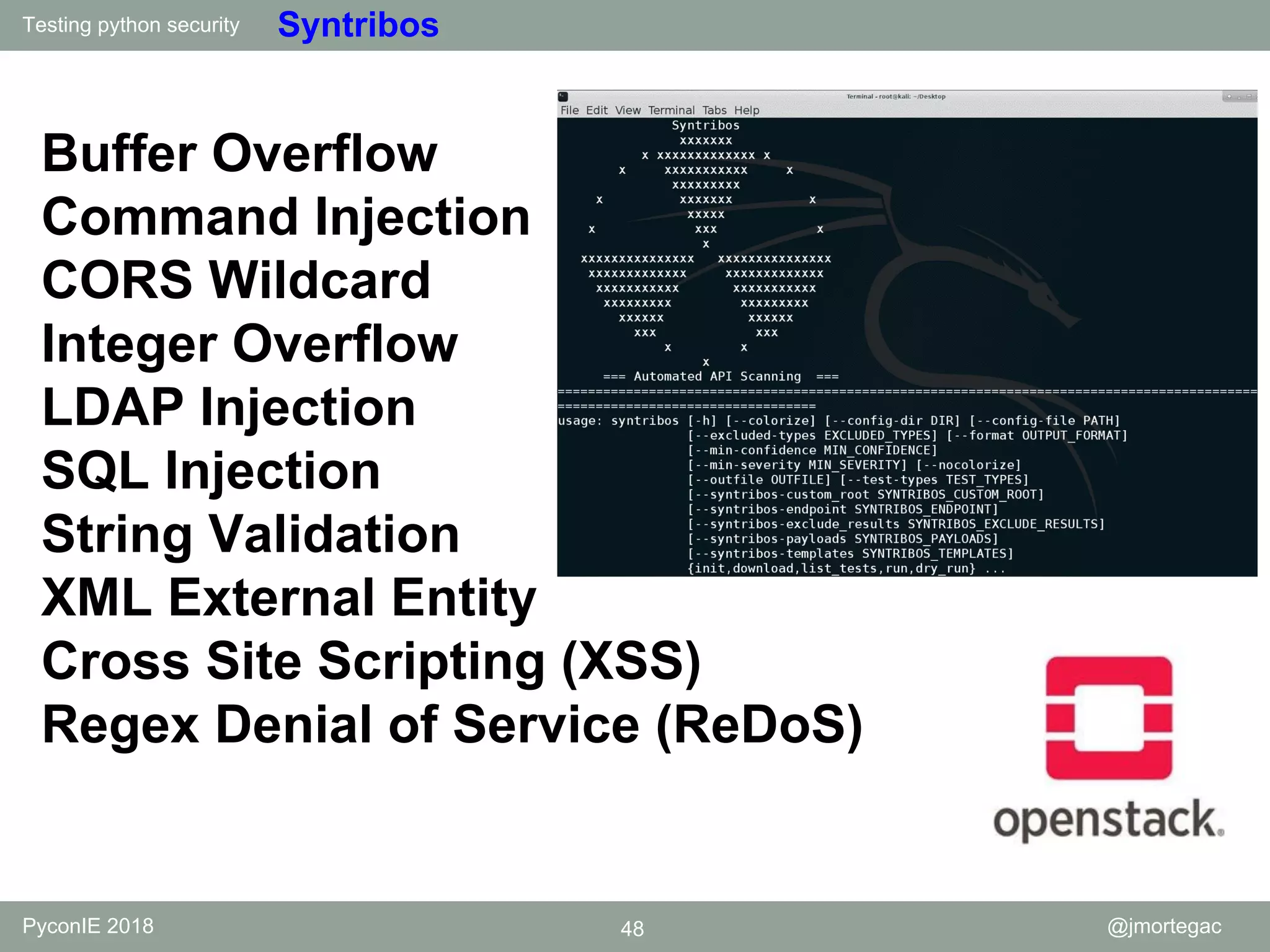
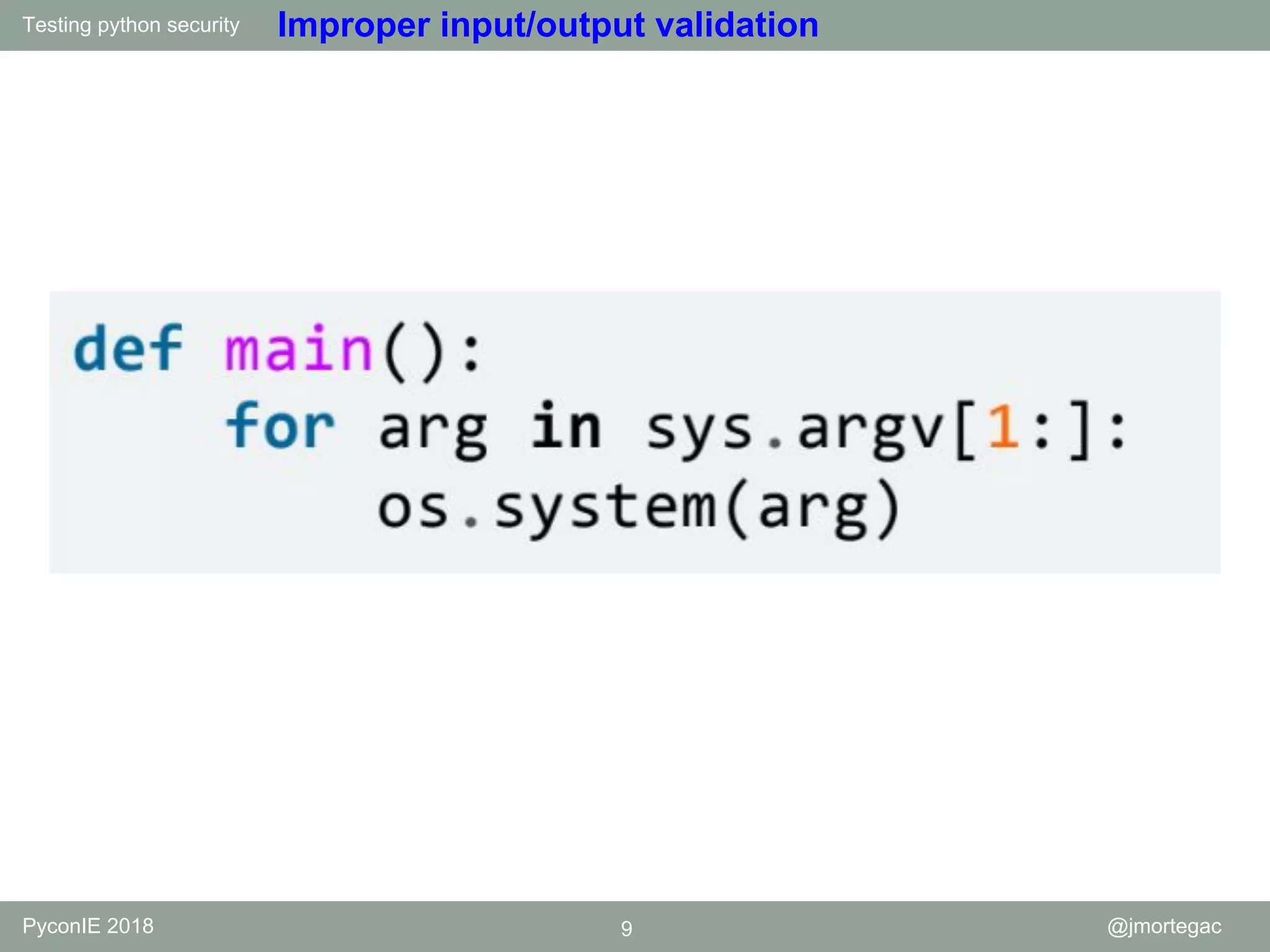
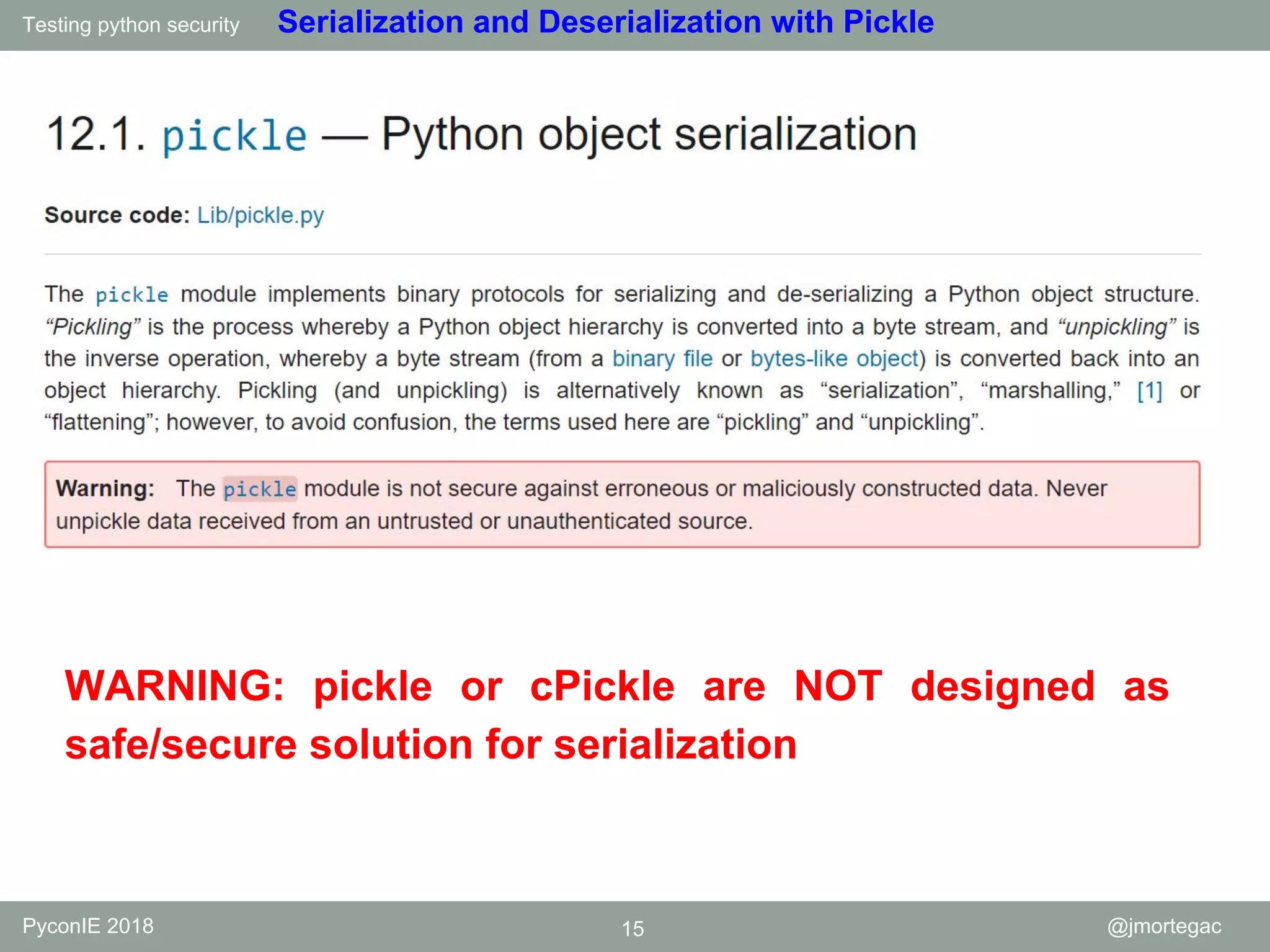
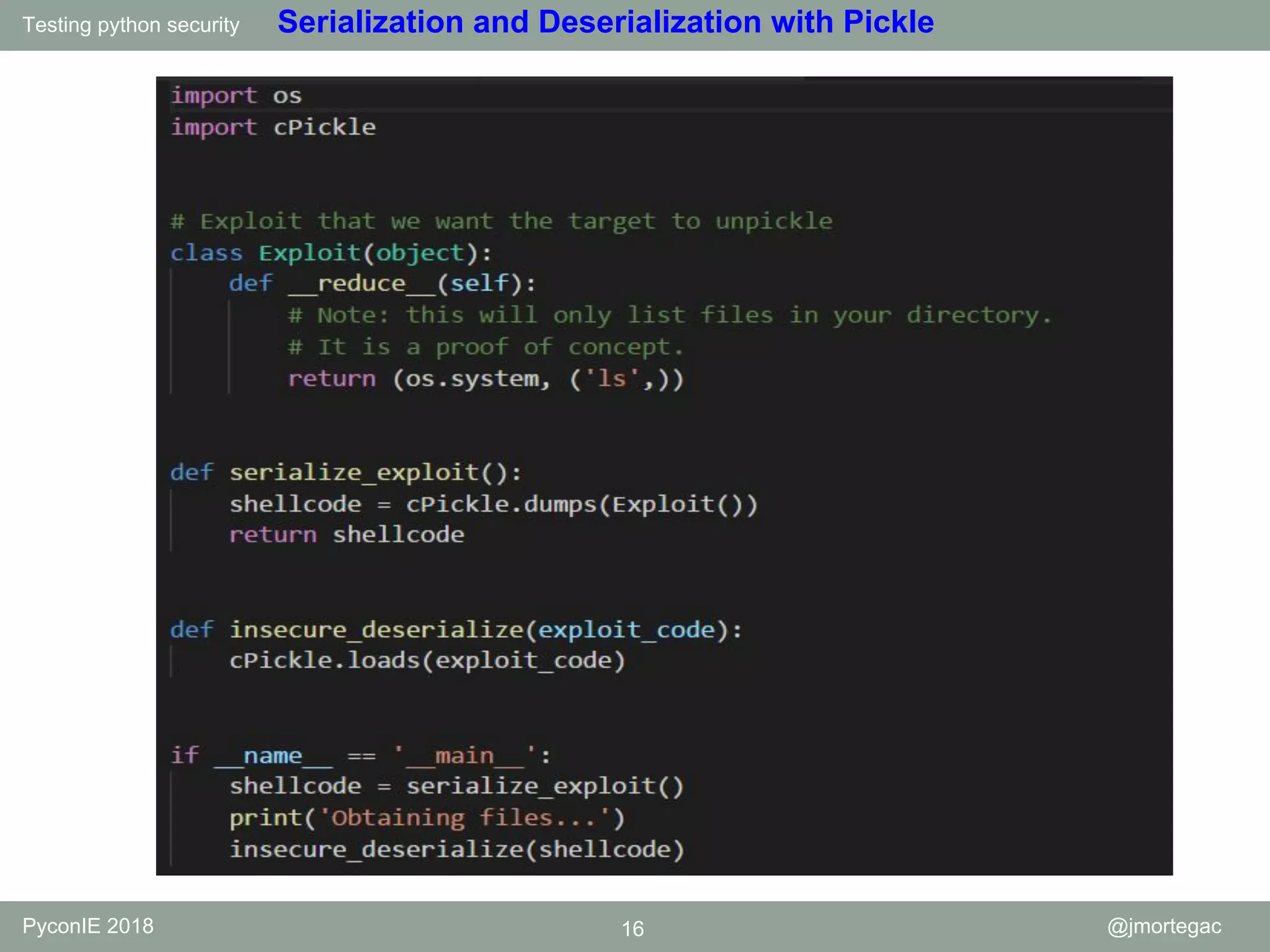
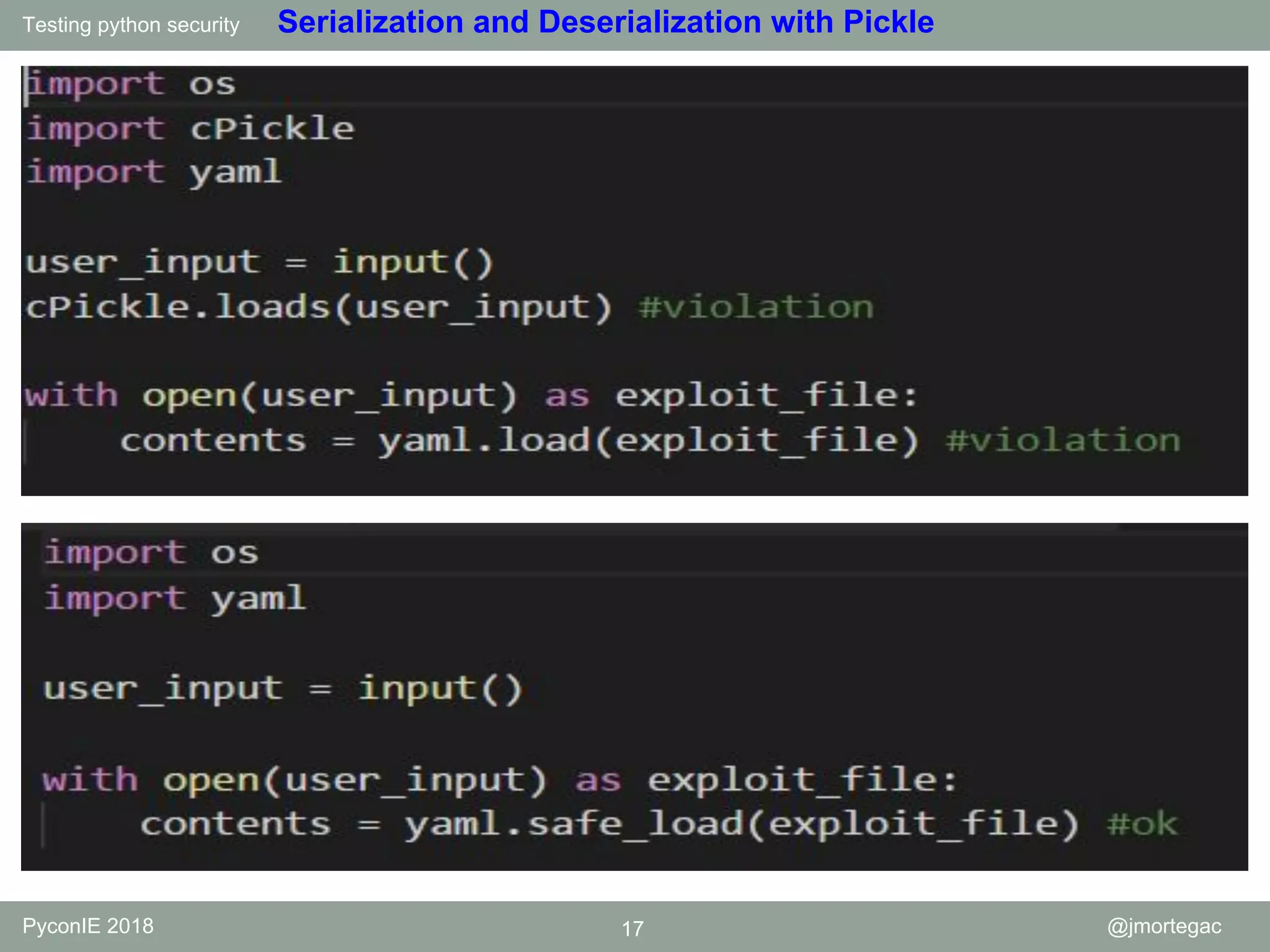
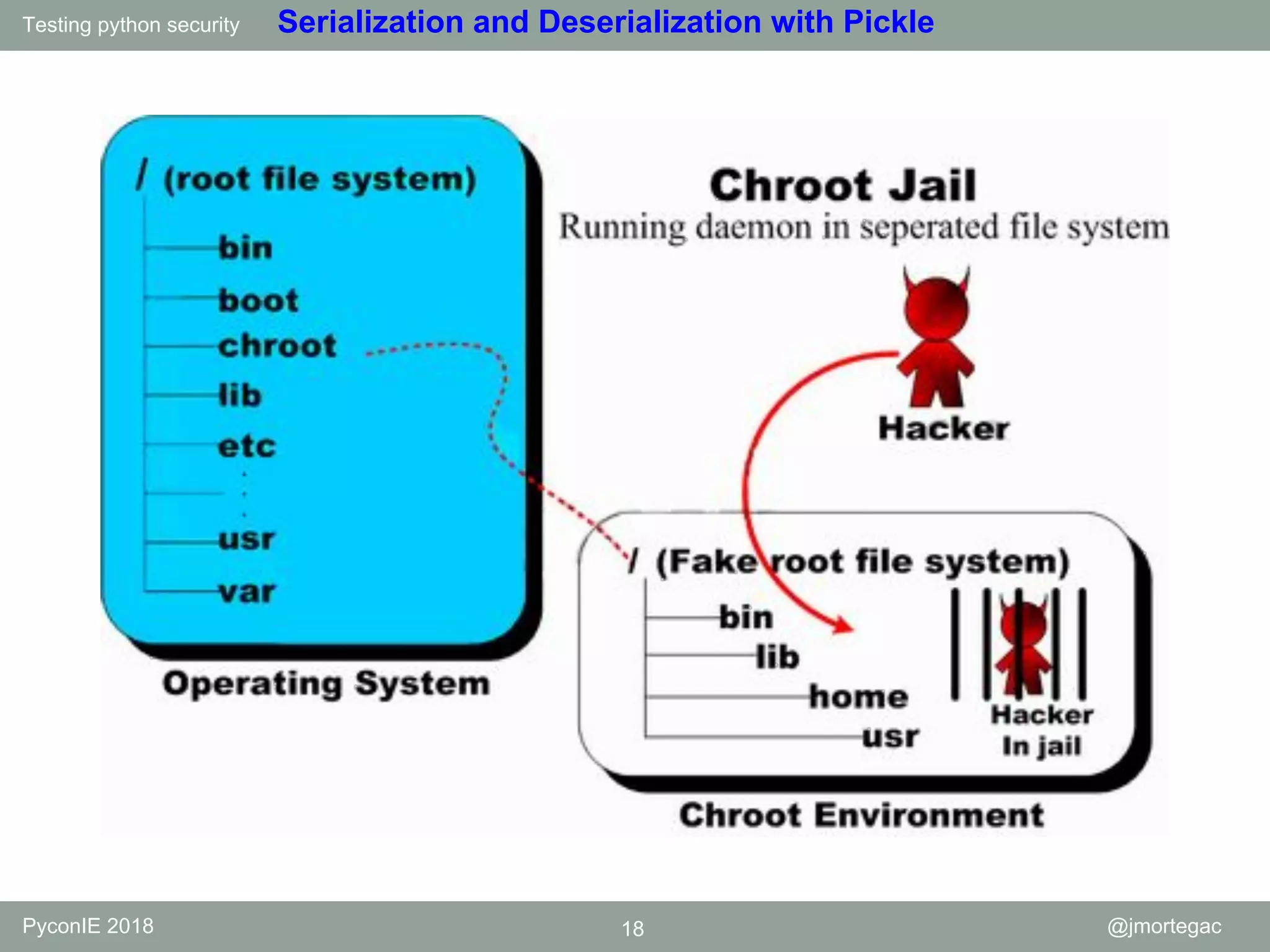
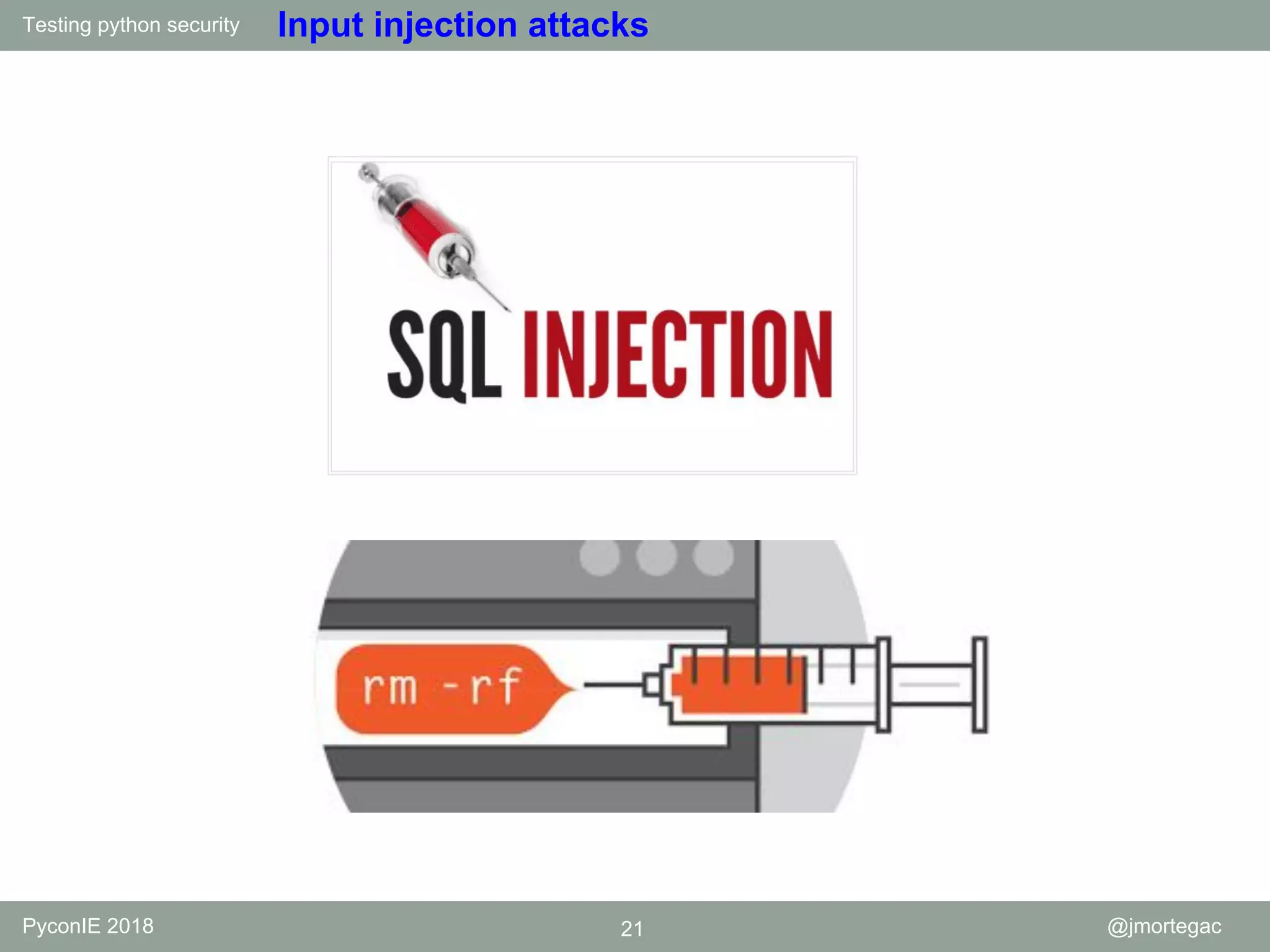
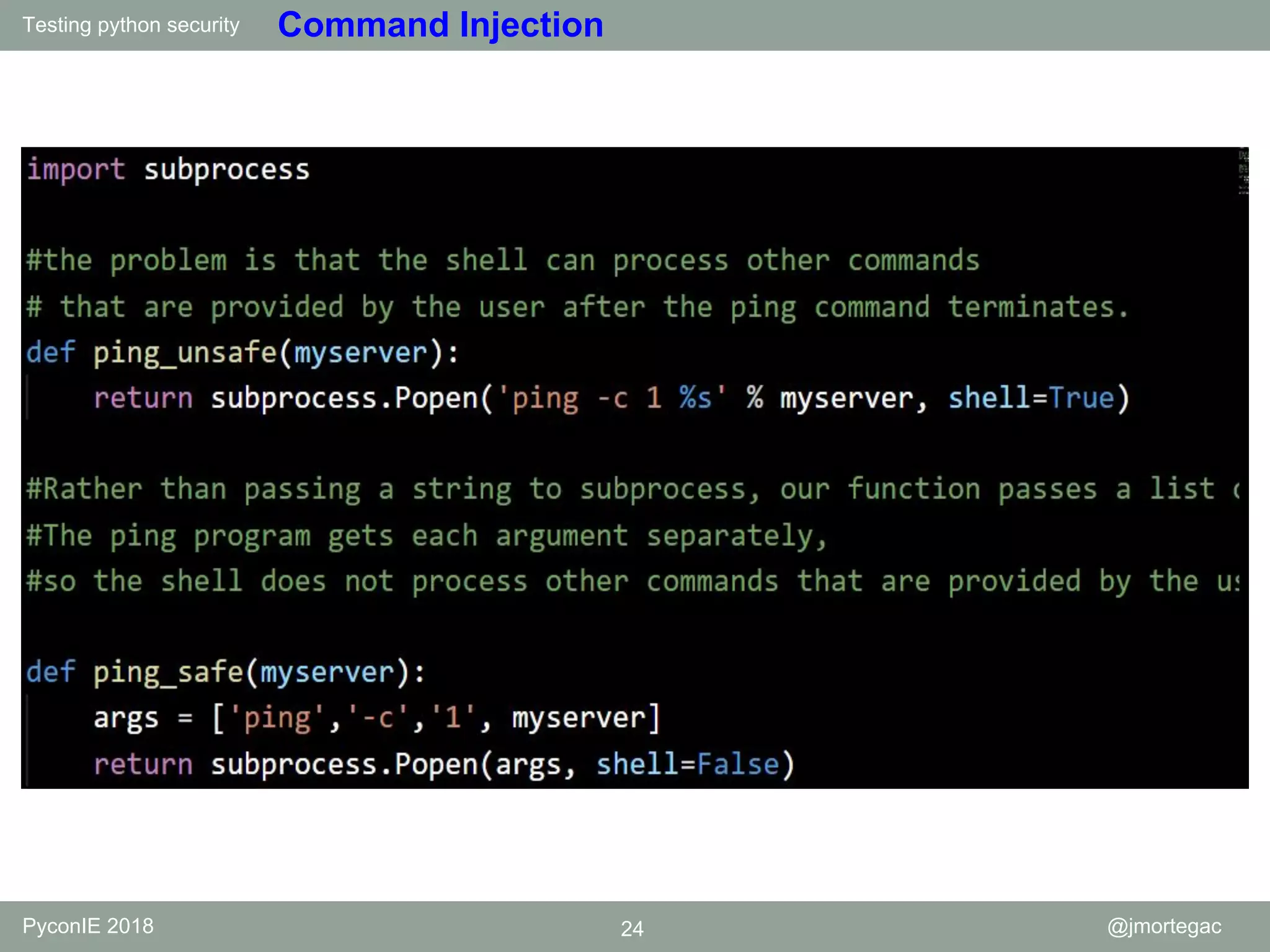
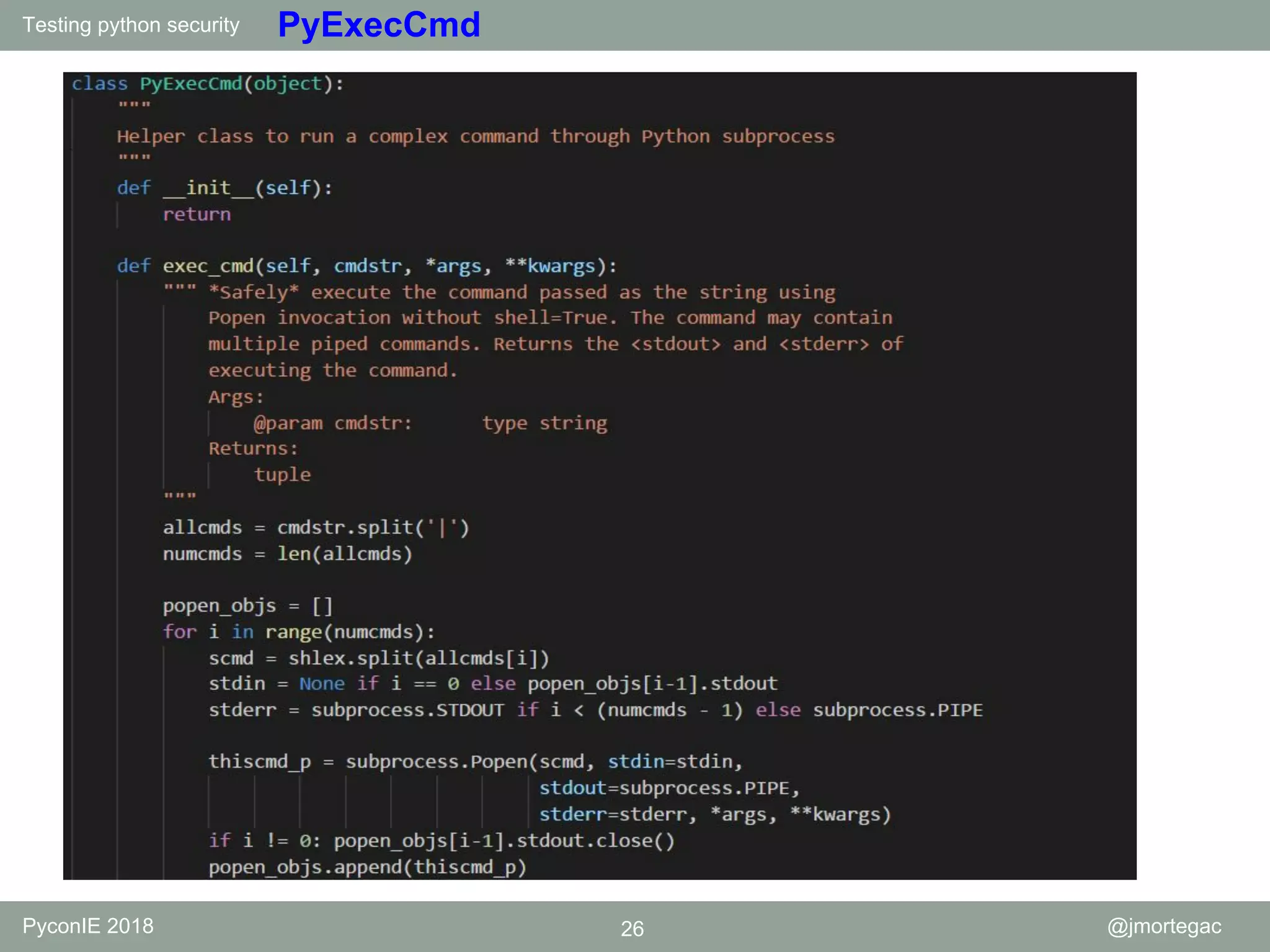
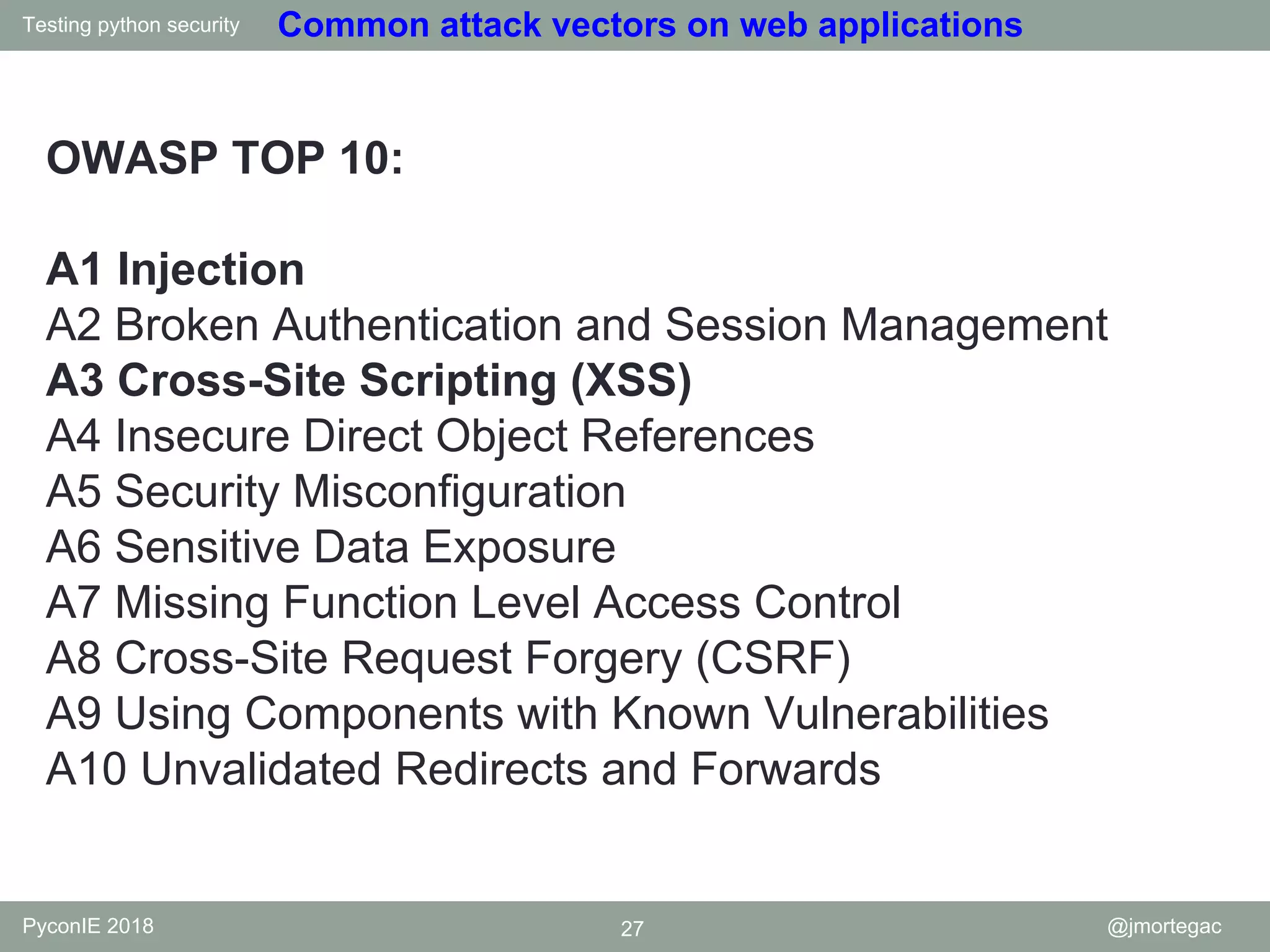
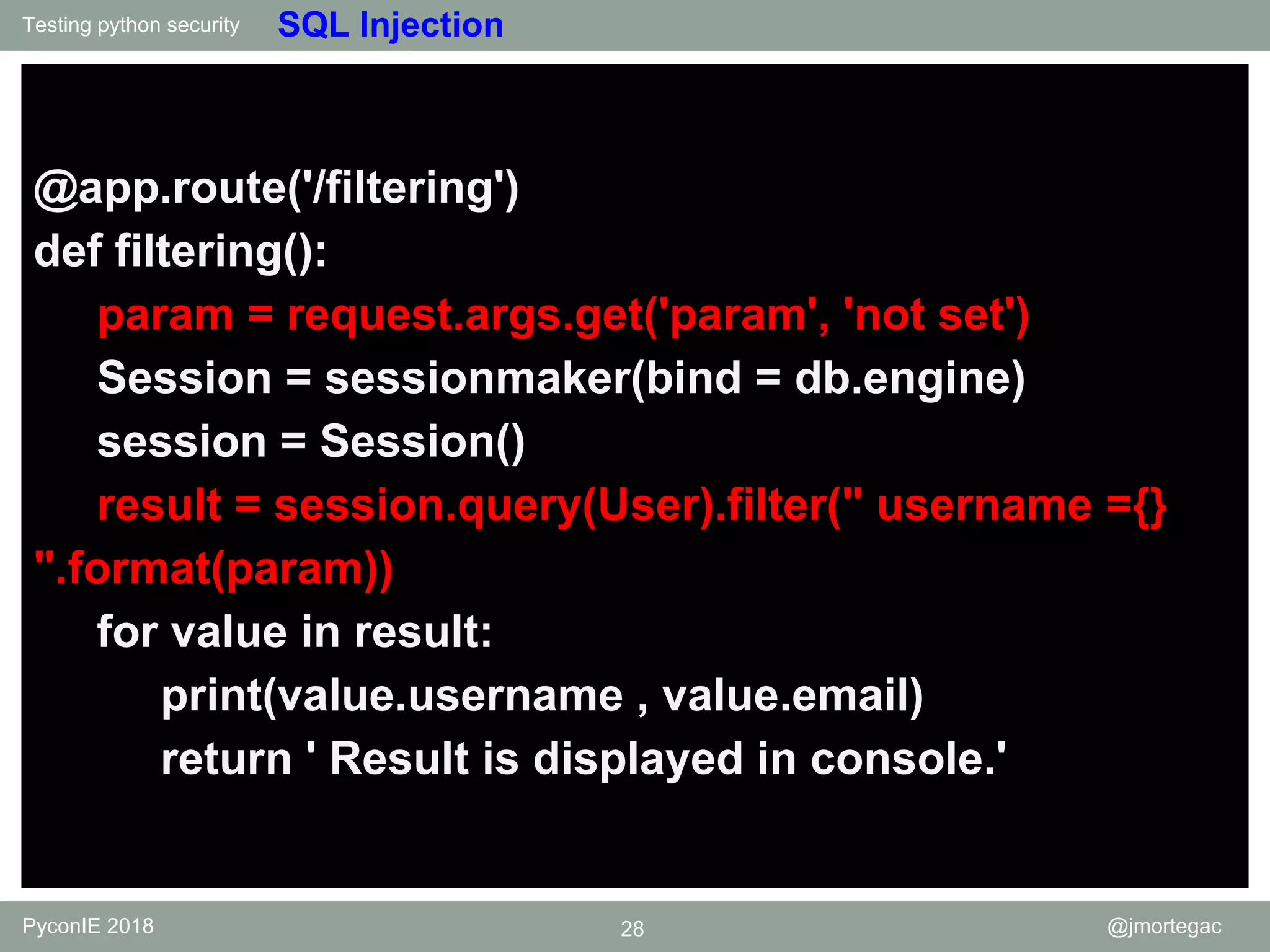
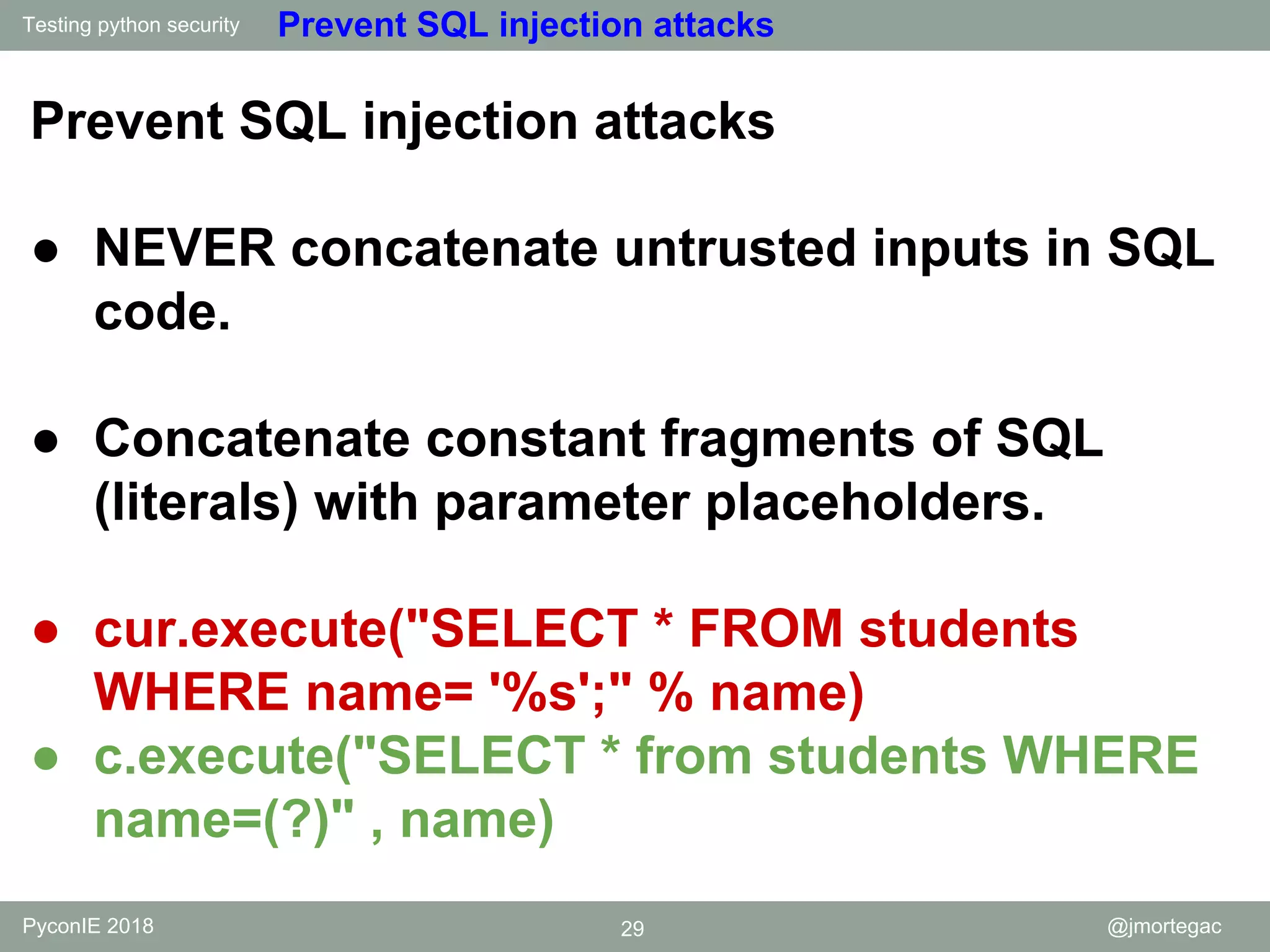
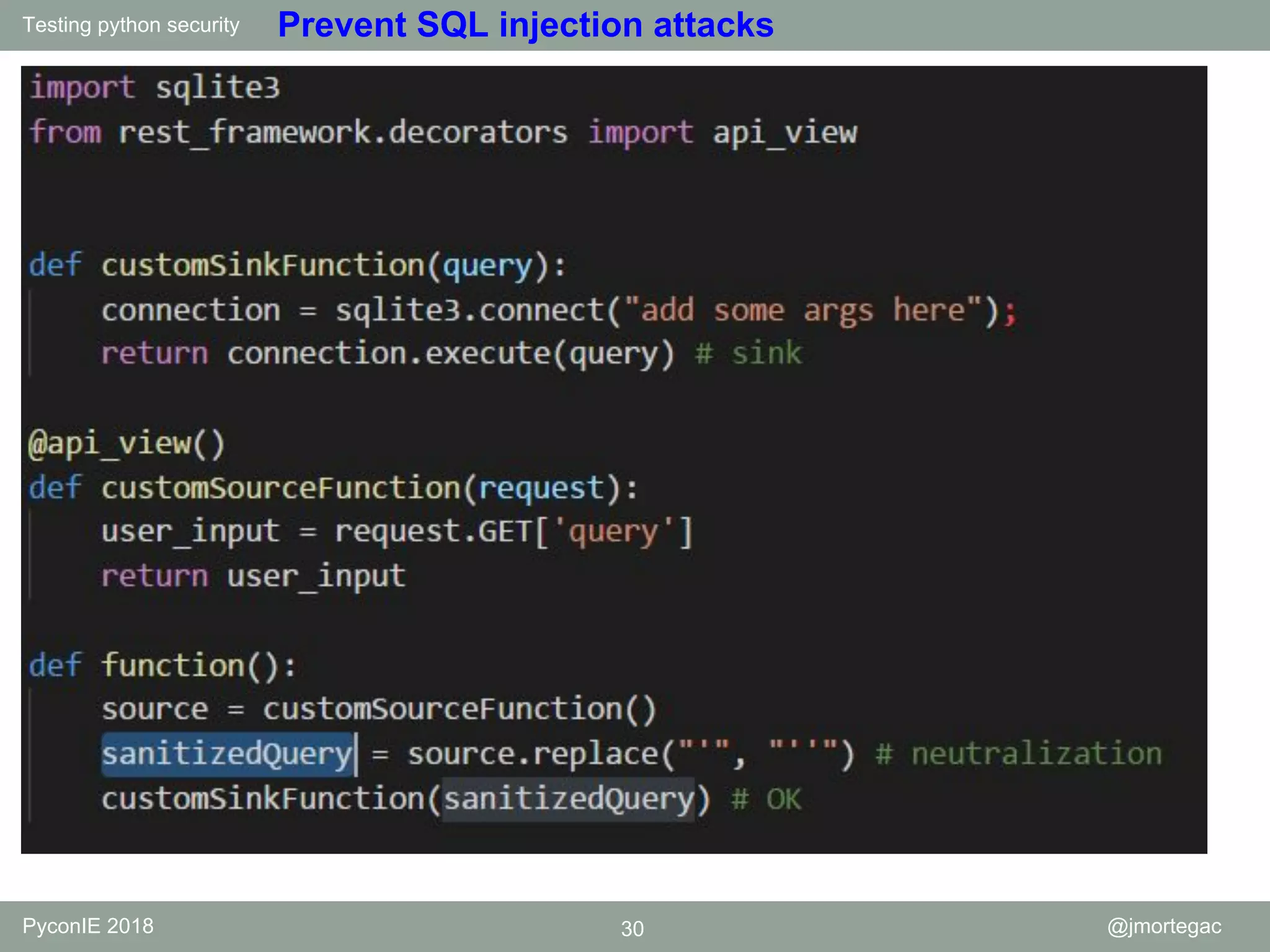
The document outlines various security practices for Python programming, focusing on automating security tasks and identifying vulnerabilities. It discusses secure coding techniques, common attack vectors (such as SQL injection and XSS), and methods to prevent such vulnerabilities. Additionally, it presents automated security testing tools and highlights potential security issues with Python components.


![Testing python security PyconIE 2018 10 @jmortegac eval() eval(expression[, globals[, locals]])](https://image.slidesharecdn.com/testingpythonsecurityv2-181111112630/75/Testing-python-security-PyCon-IE-10-2048.jpg)
![Testing python security PyconIE 2018 22 @jmortegac Command Injection @app.route('/menu',methods =['POST']) def menu(): param = request.form [ ' suggestion '] command = ' echo ' + param + ' >> ' + ' menu.txt ' subprocess.call(command,shell = True) with open('menu.txt','r') as f: menu = f.read() return render_template('command_injection.html', menu = menu)](https://image.slidesharecdn.com/testingpythonsecurityv2-181111112630/75/Testing-python-security-PyCon-IE-22-2048.jpg)
![Testing python security PyconIE 2018 23 @jmortegac Command Injection @app.route('/menu',methods =['POST']) def menu(): param = request.form [ ' suggestion '] command = ' echo ' + param + ' >> ' + ' menu.txt ' subprocess.call(command,shell = False) with open('menu.txt','r') as f: menu = f.read() return render_template('command_injection.html', menu = menu)](https://image.slidesharecdn.com/testingpythonsecurityv2-181111112630/75/Testing-python-security-PyCon-IE-23-2048.jpg)
![Testing python security PyconIE 2018 31 @jmortegac XSS from flask import Flask , request , make_response app = Flask(__name__) @app.route ('/XSS_param',methods =['GET ]) def XSS(): param = request.args.get('param','not set') html = open('templates/XSS_param.html ').read() resp = make_response(html.replace('{{ param}}',param)) return resp if __name__ == ' __main__ ': app.run(debug = True)](https://image.slidesharecdn.com/testingpythonsecurityv2-181111112630/75/Testing-python-security-PyCon-IE-31-2048.jpg)