Download as PDF, PPTX

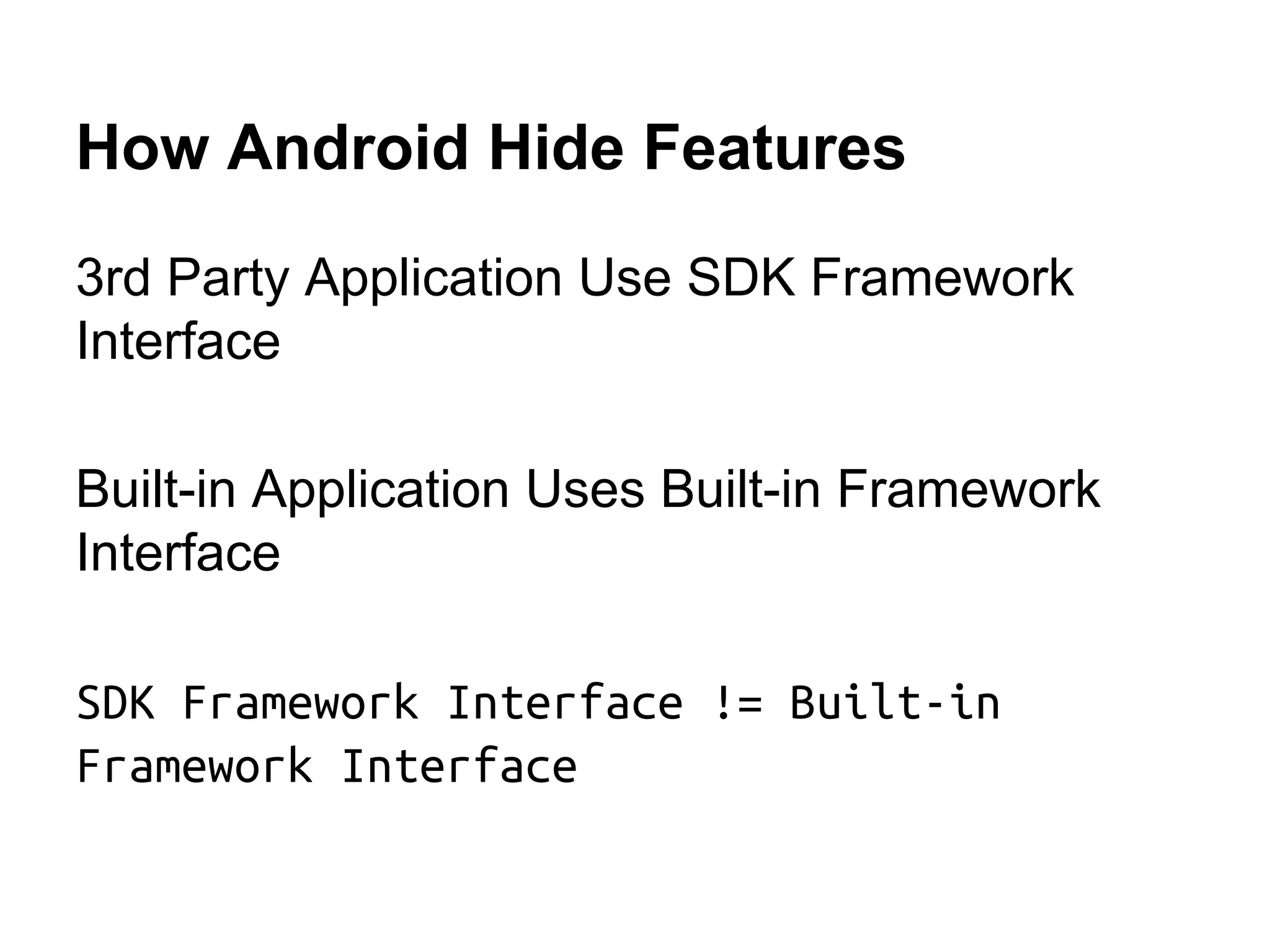
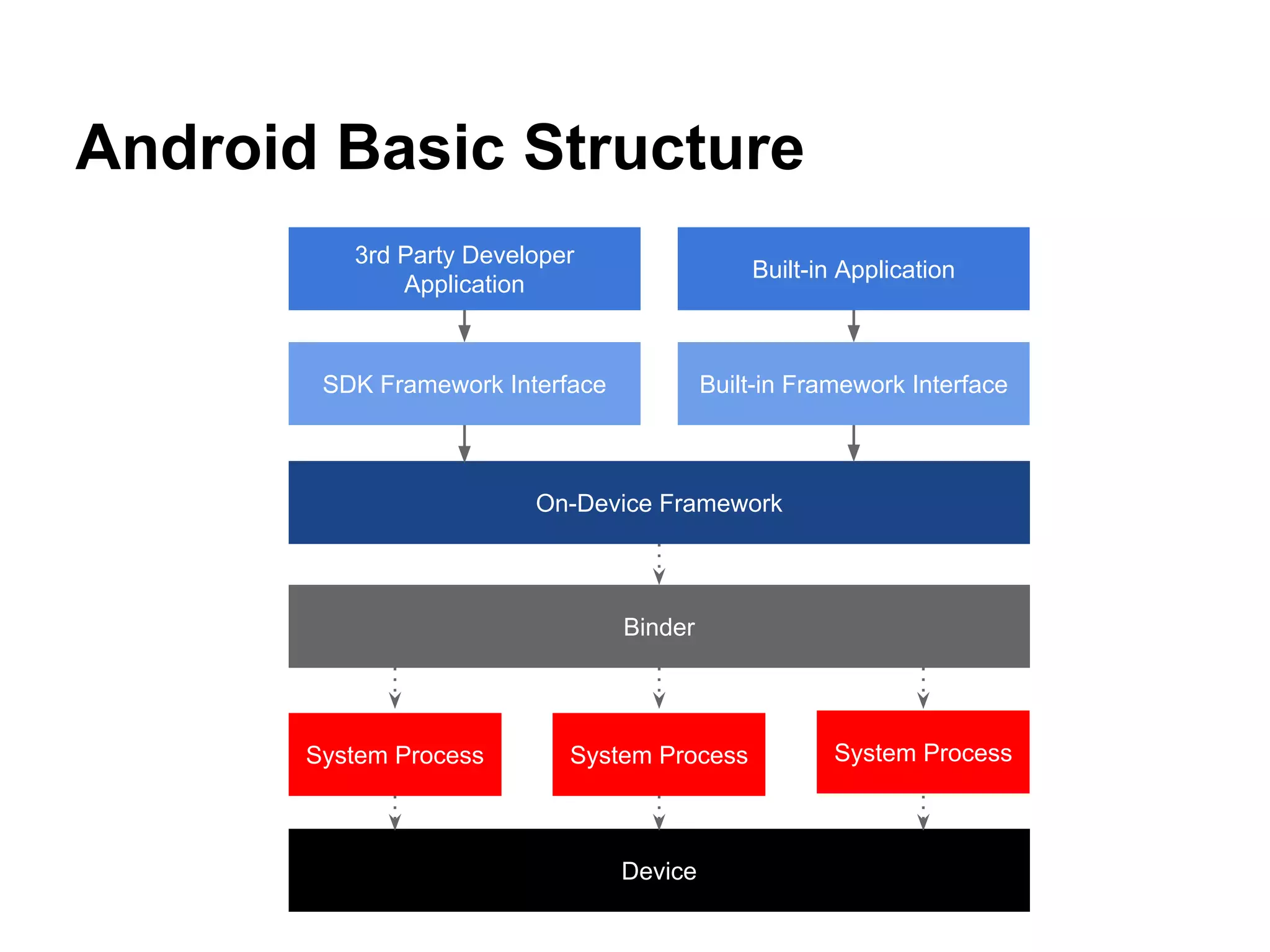
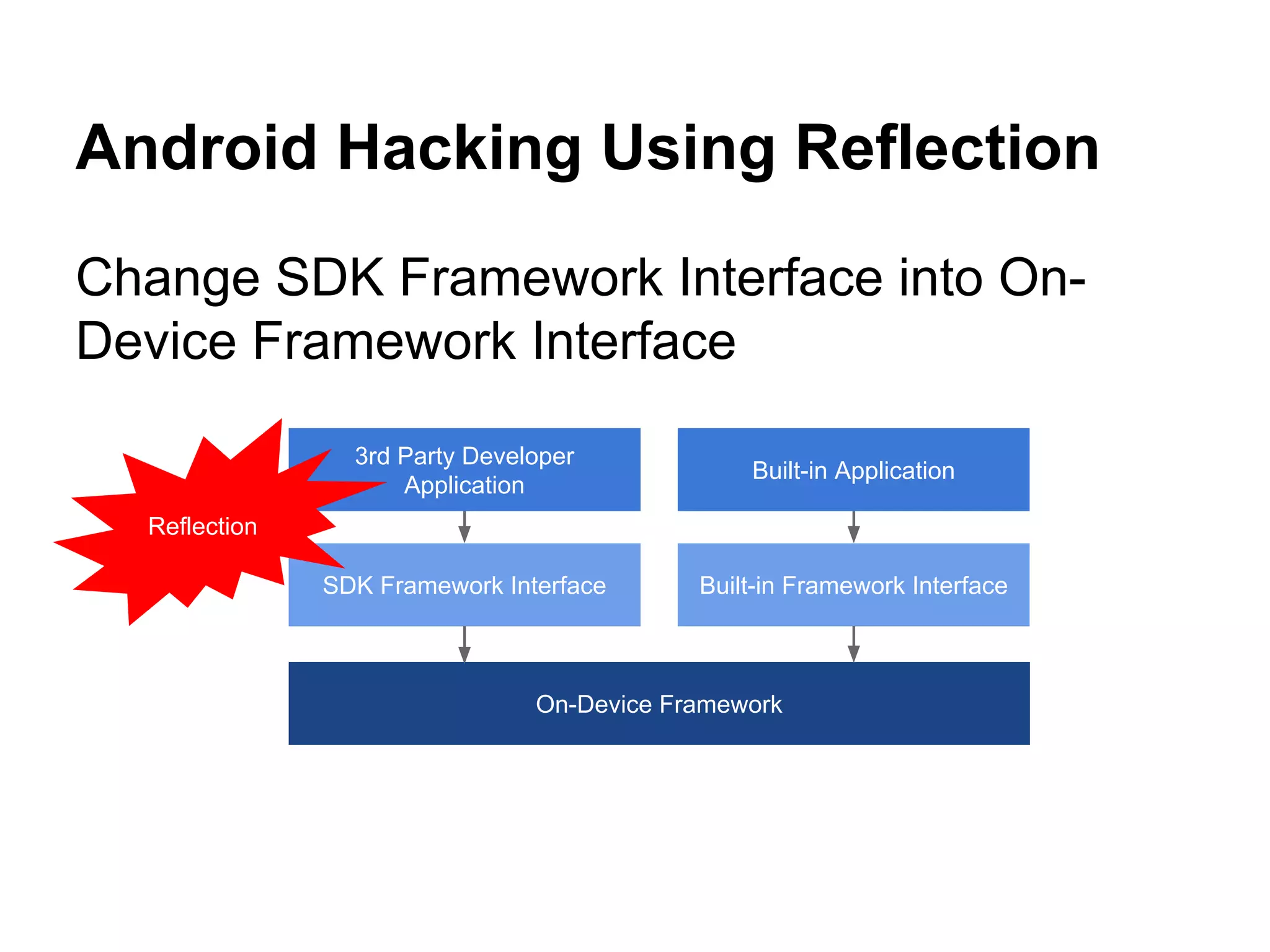
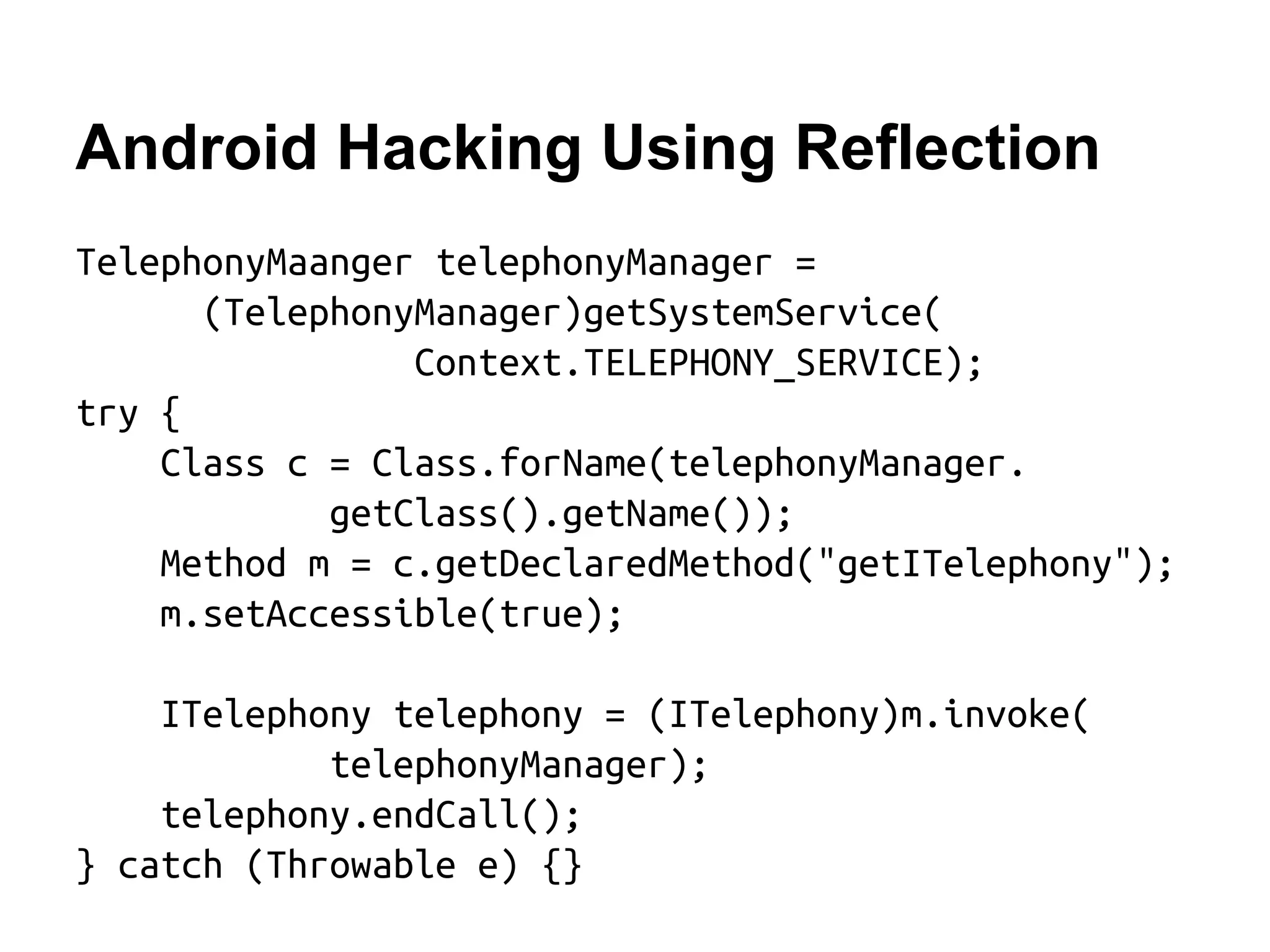

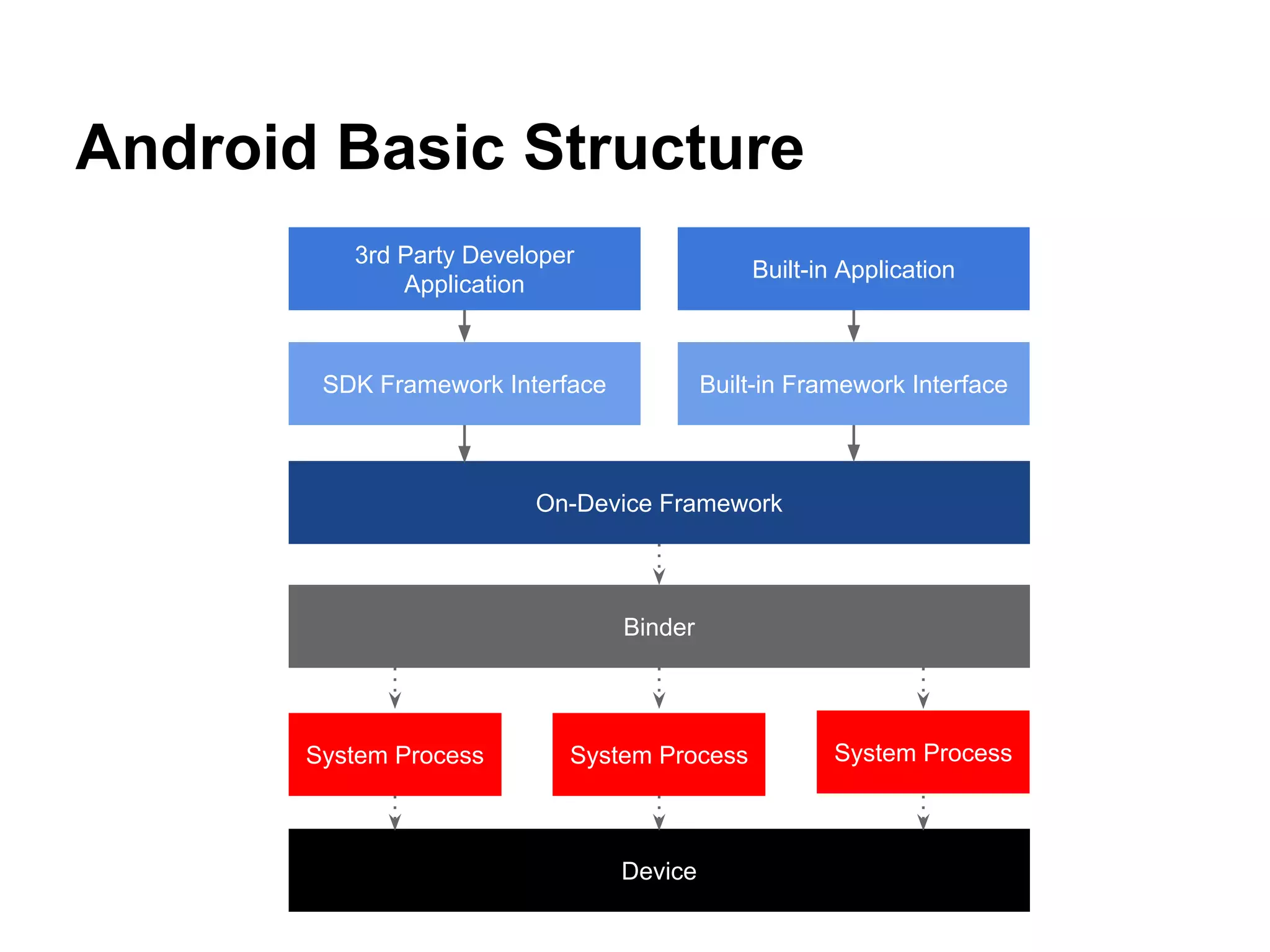
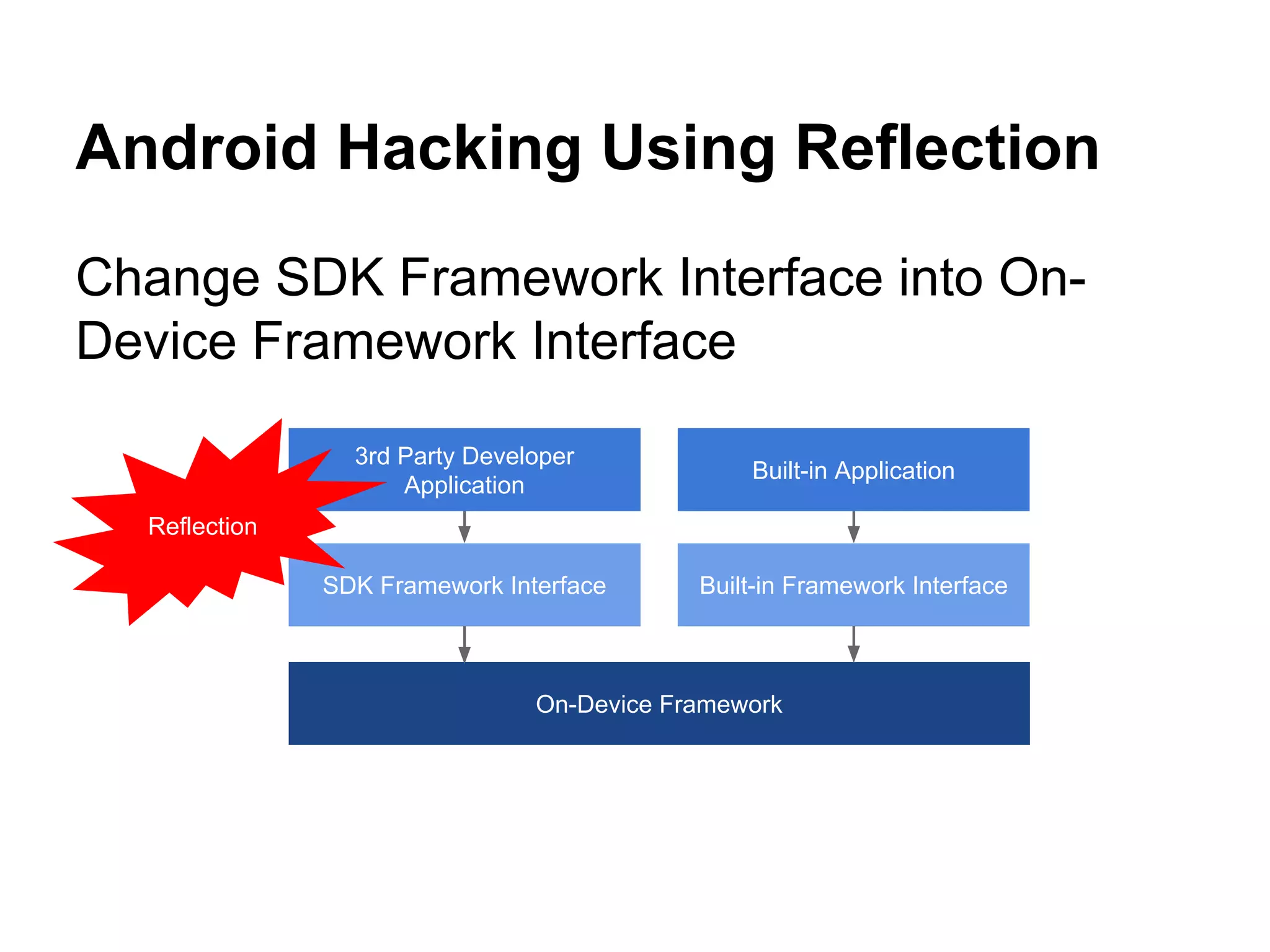
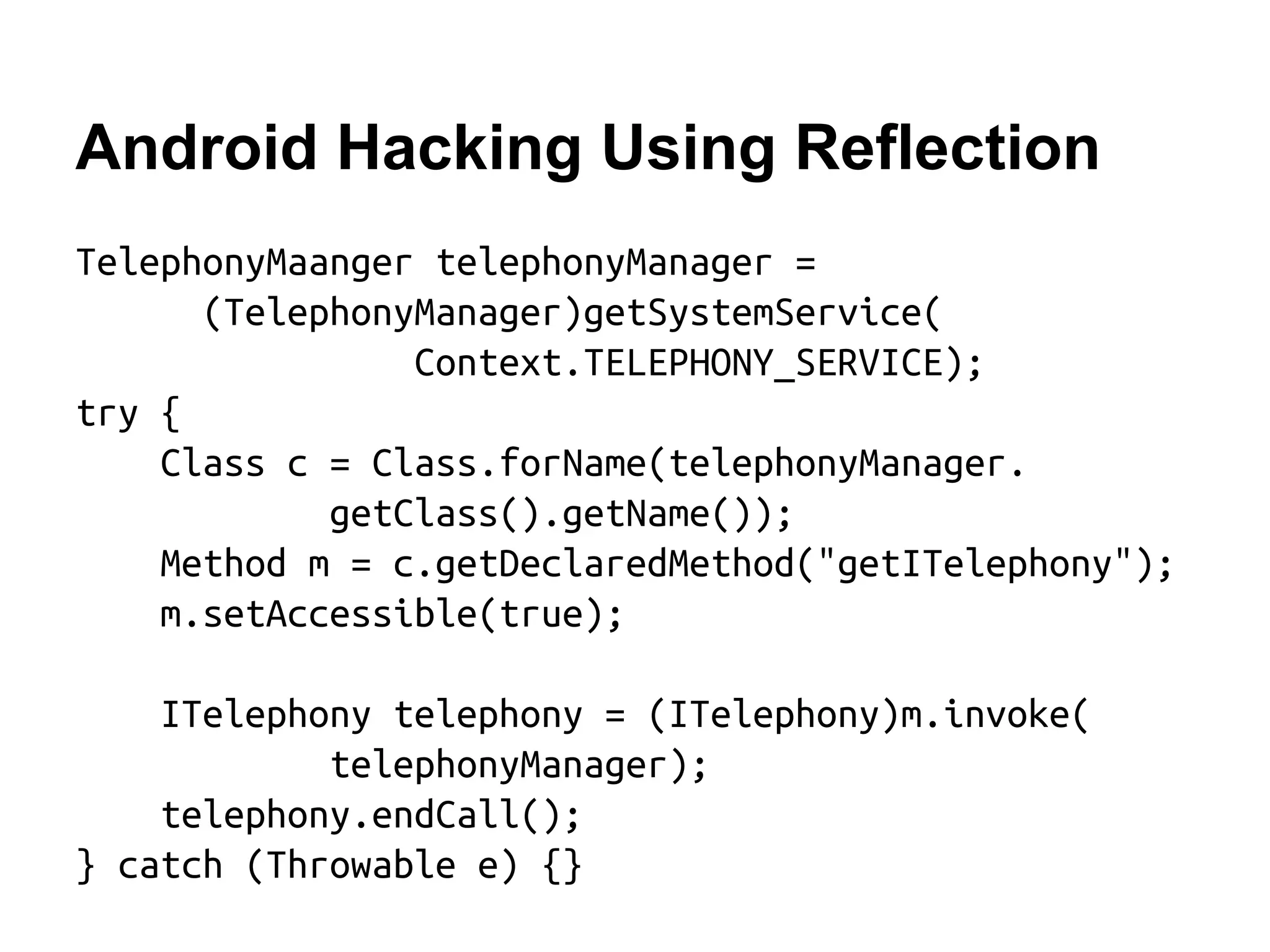
This document discusses using reflection in Android to access hidden and restricted features. It describes how Android separates interfaces for third-party and built-in apps. It then explains how reflection can be used to change the interface and allow third-party apps to access features usually only available to built-in apps, with examples of how to end a call via reflection. However, it notes reflection has limitations like performance overhead and may not work on all devices.