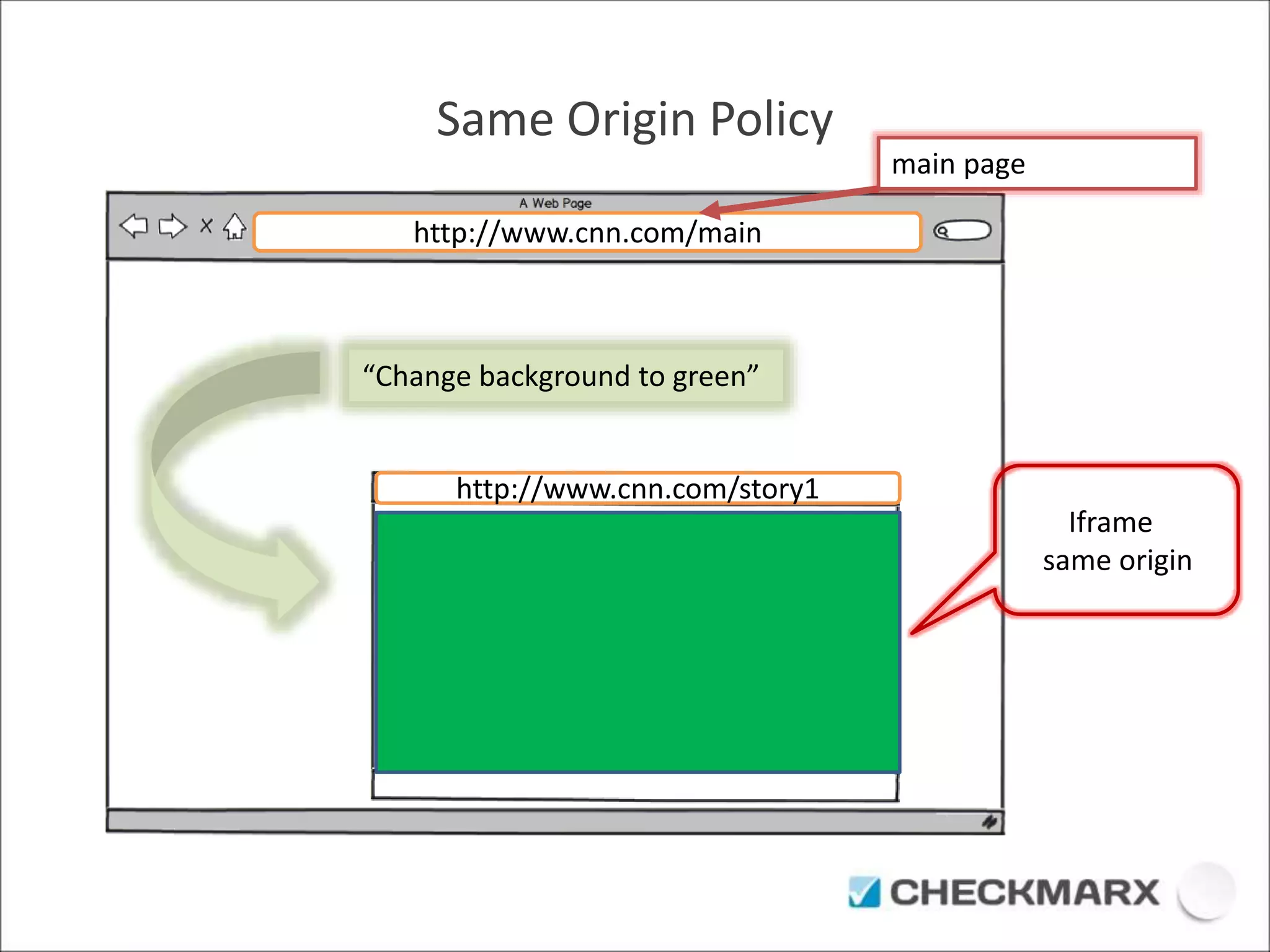
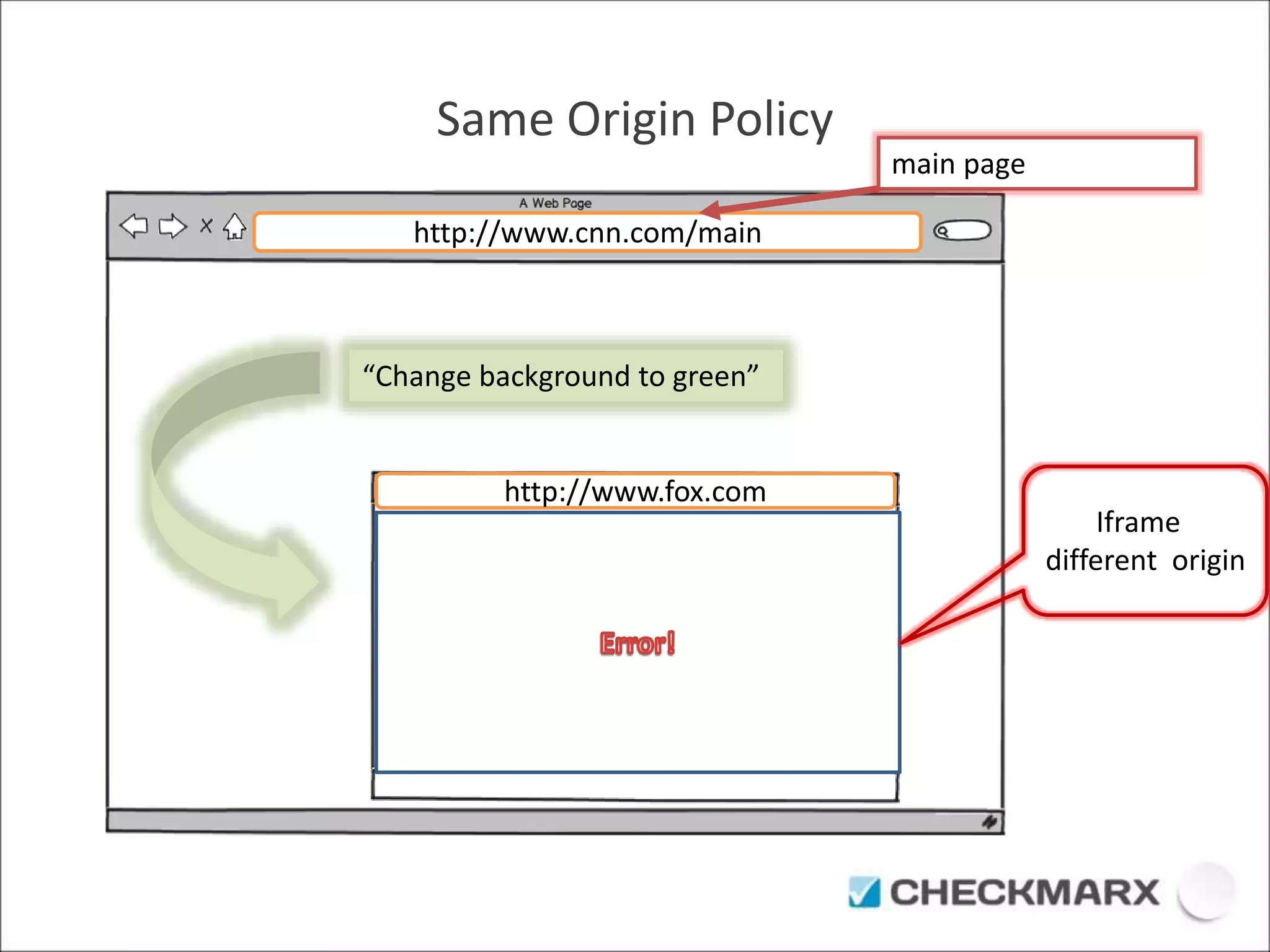
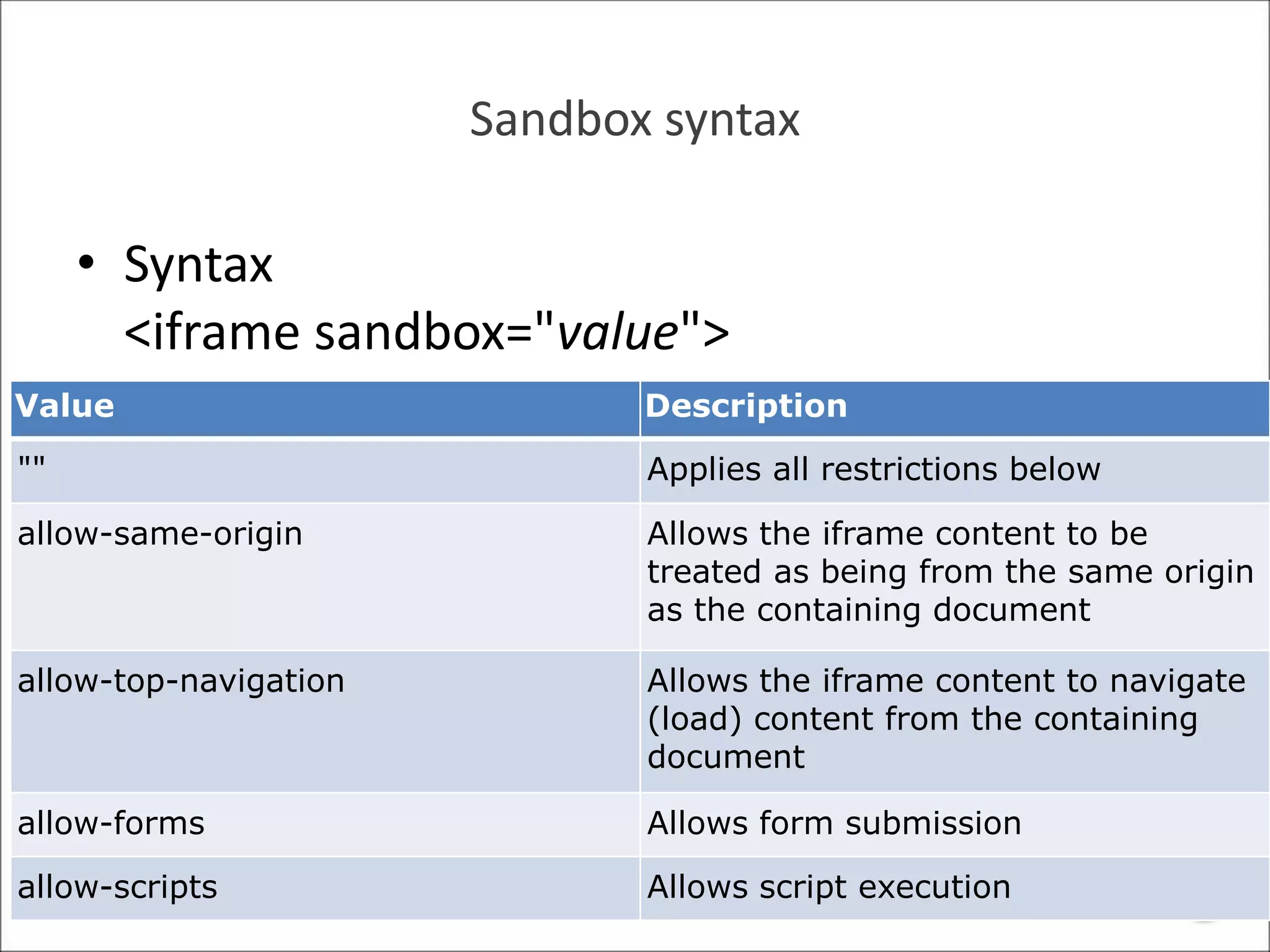
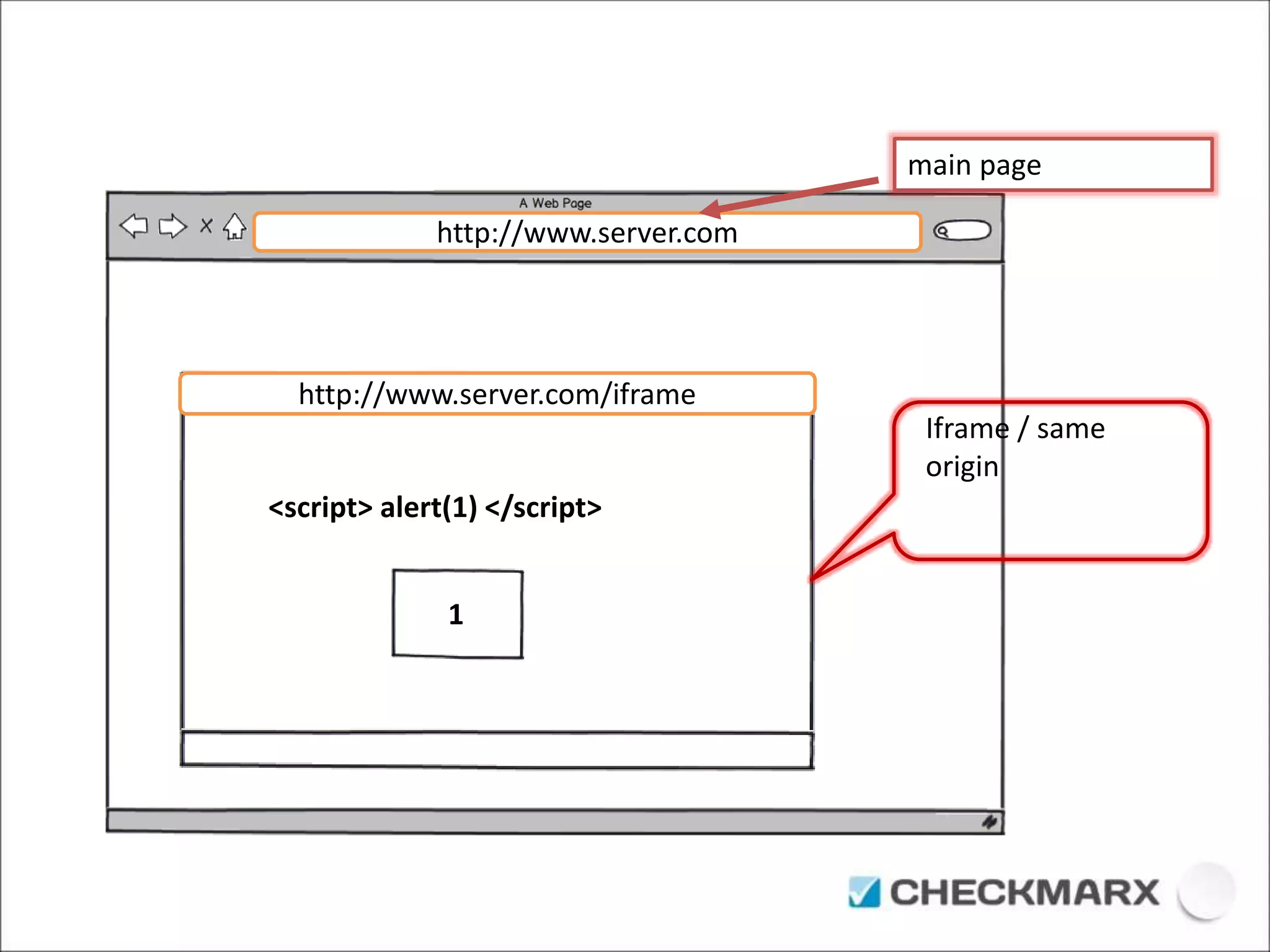
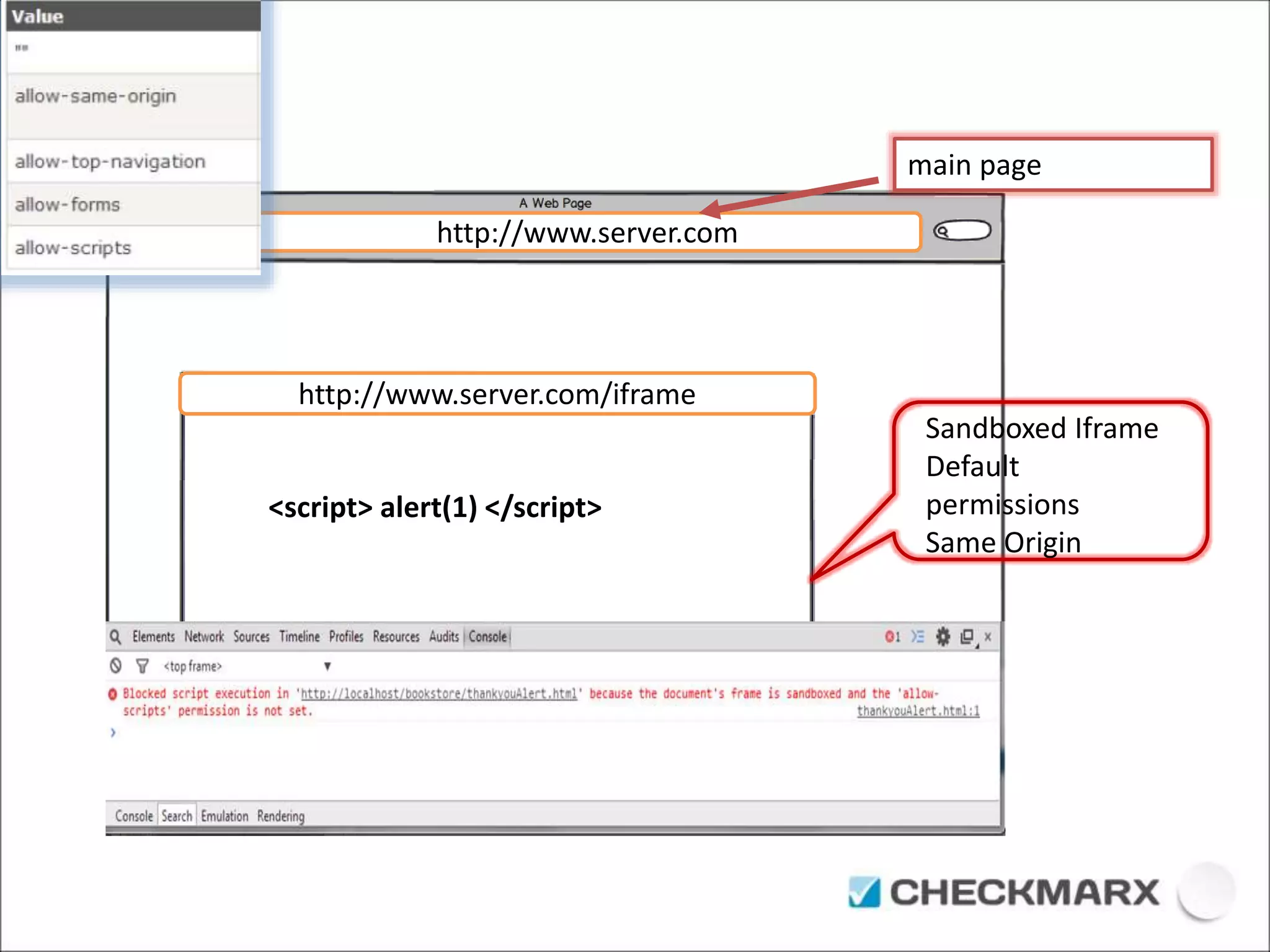
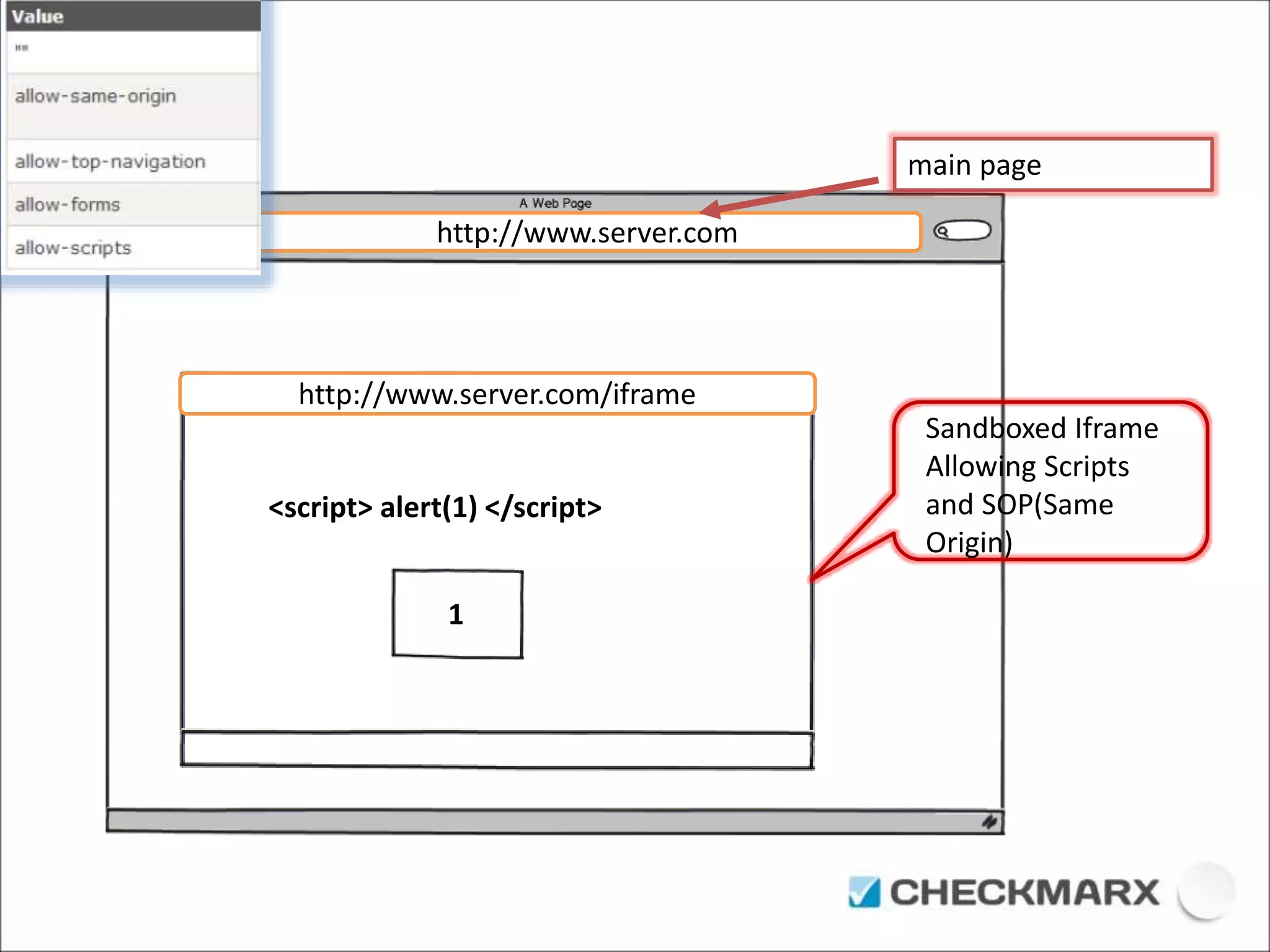
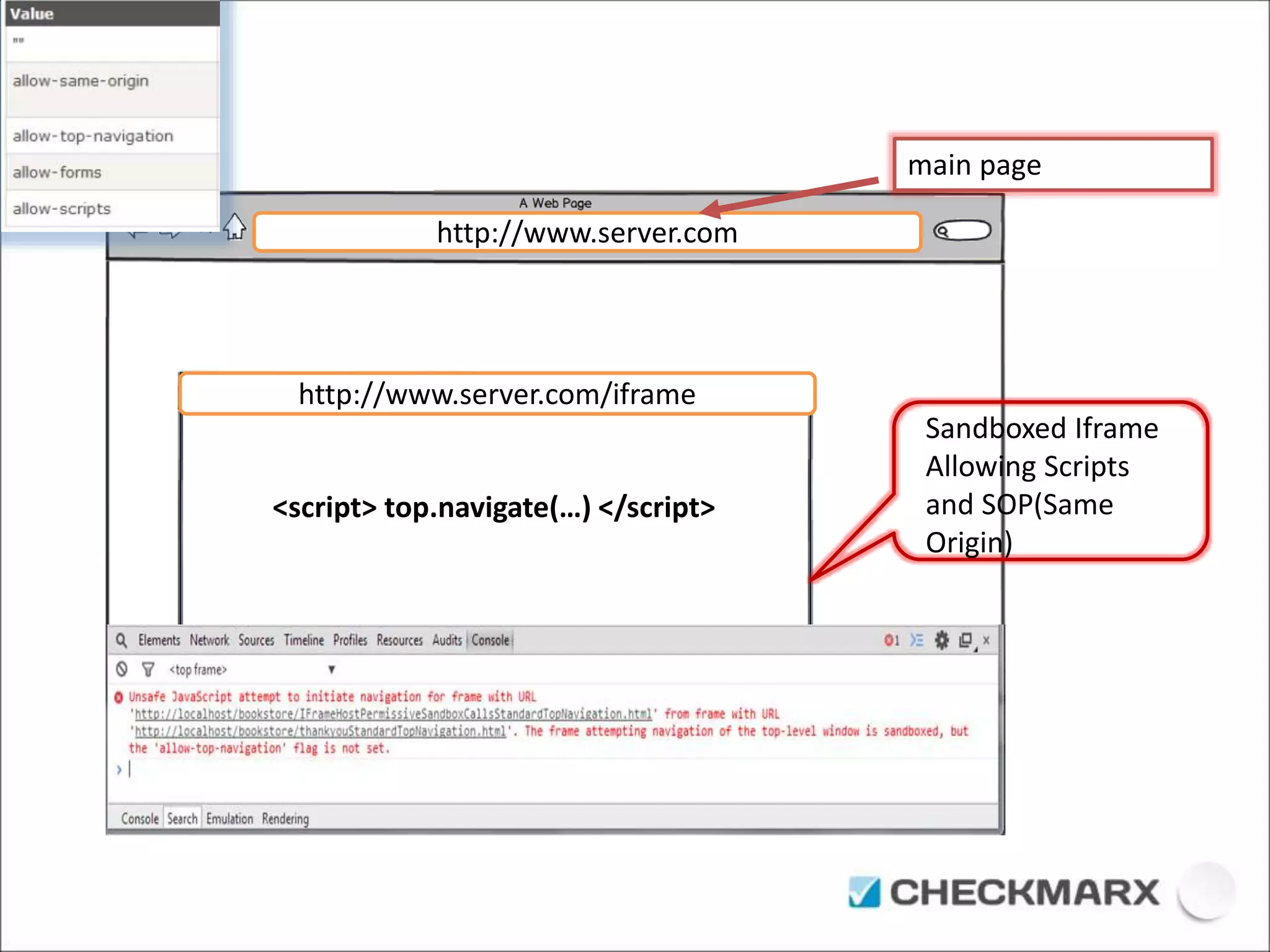
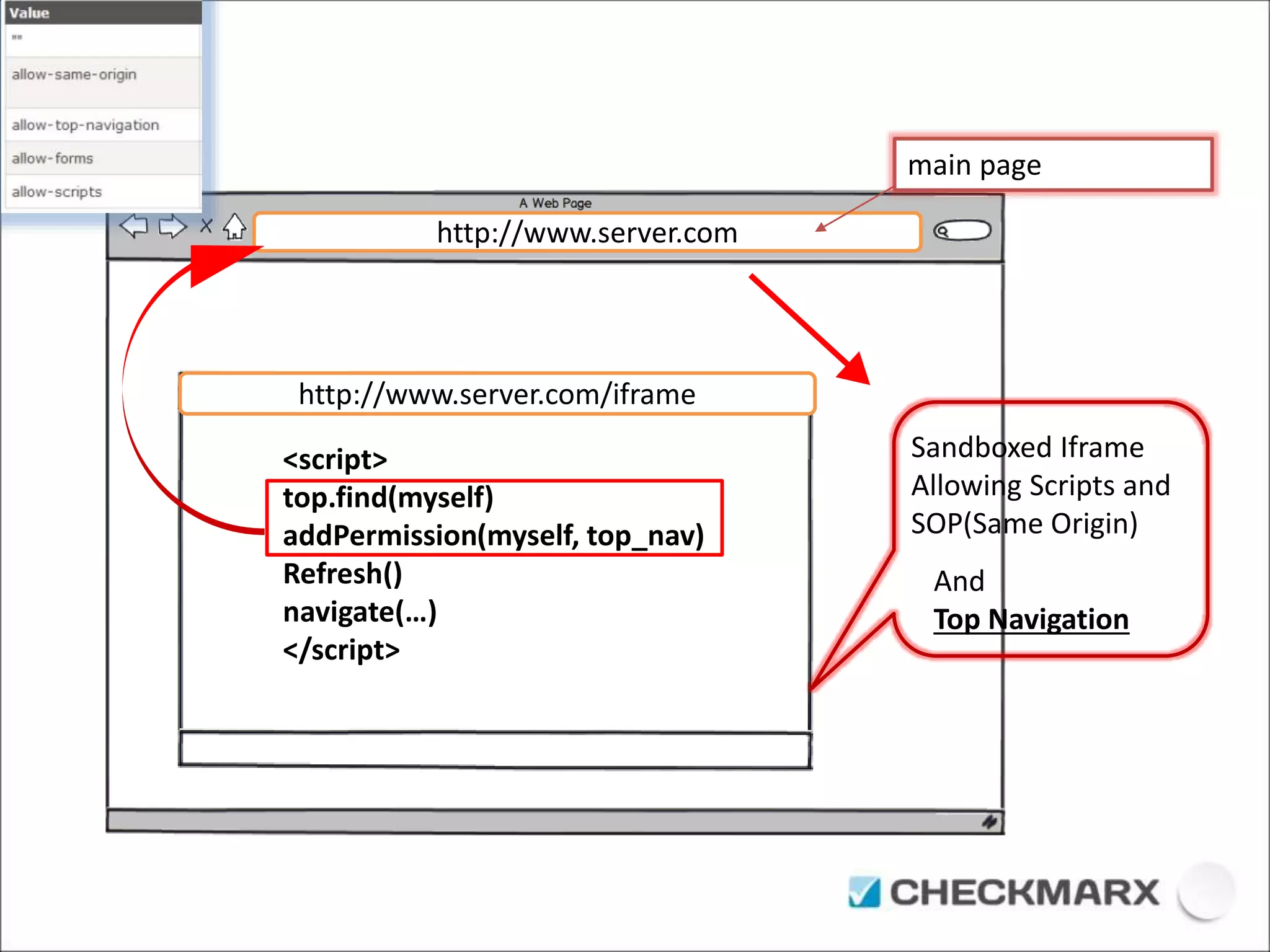
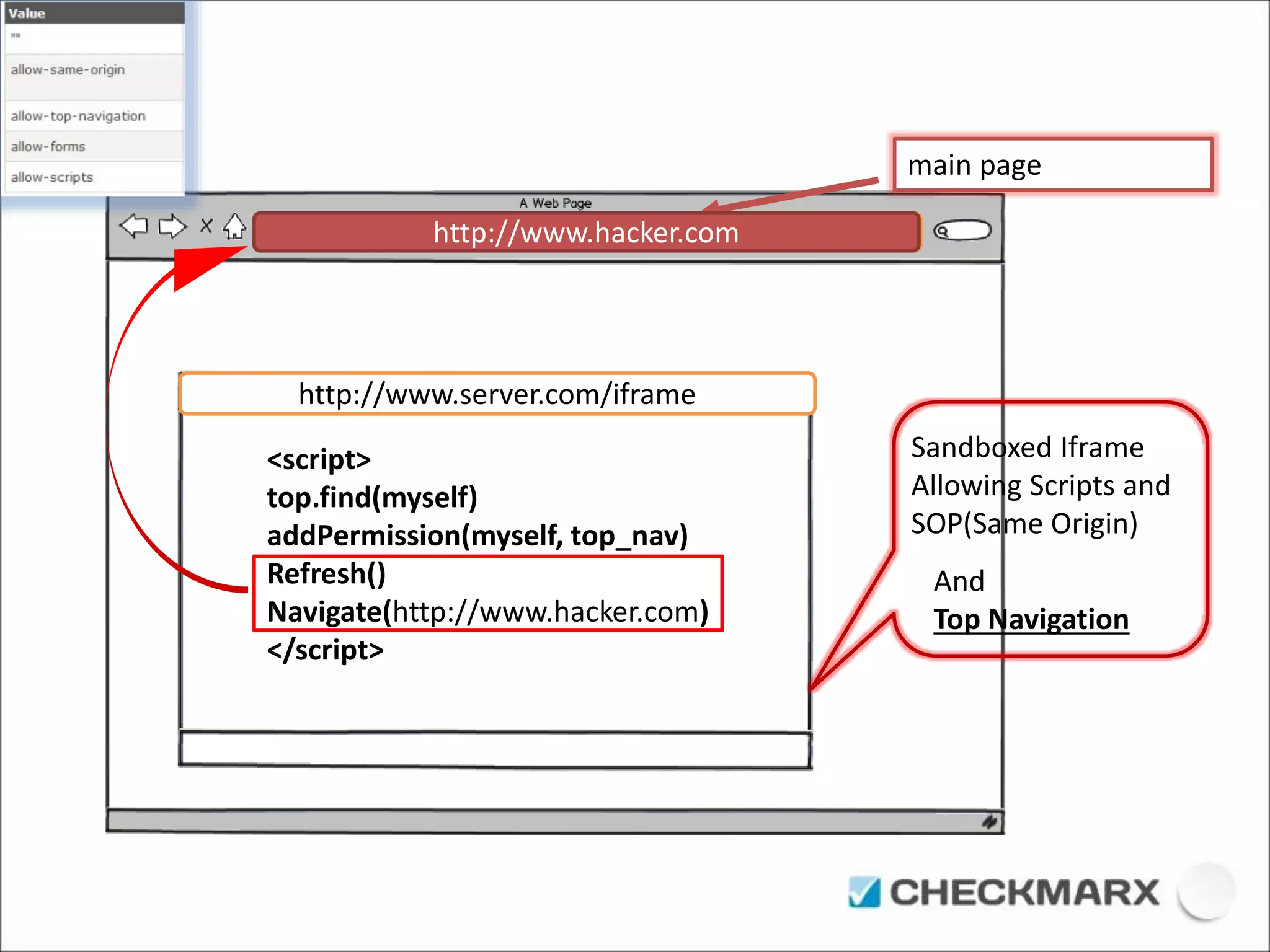
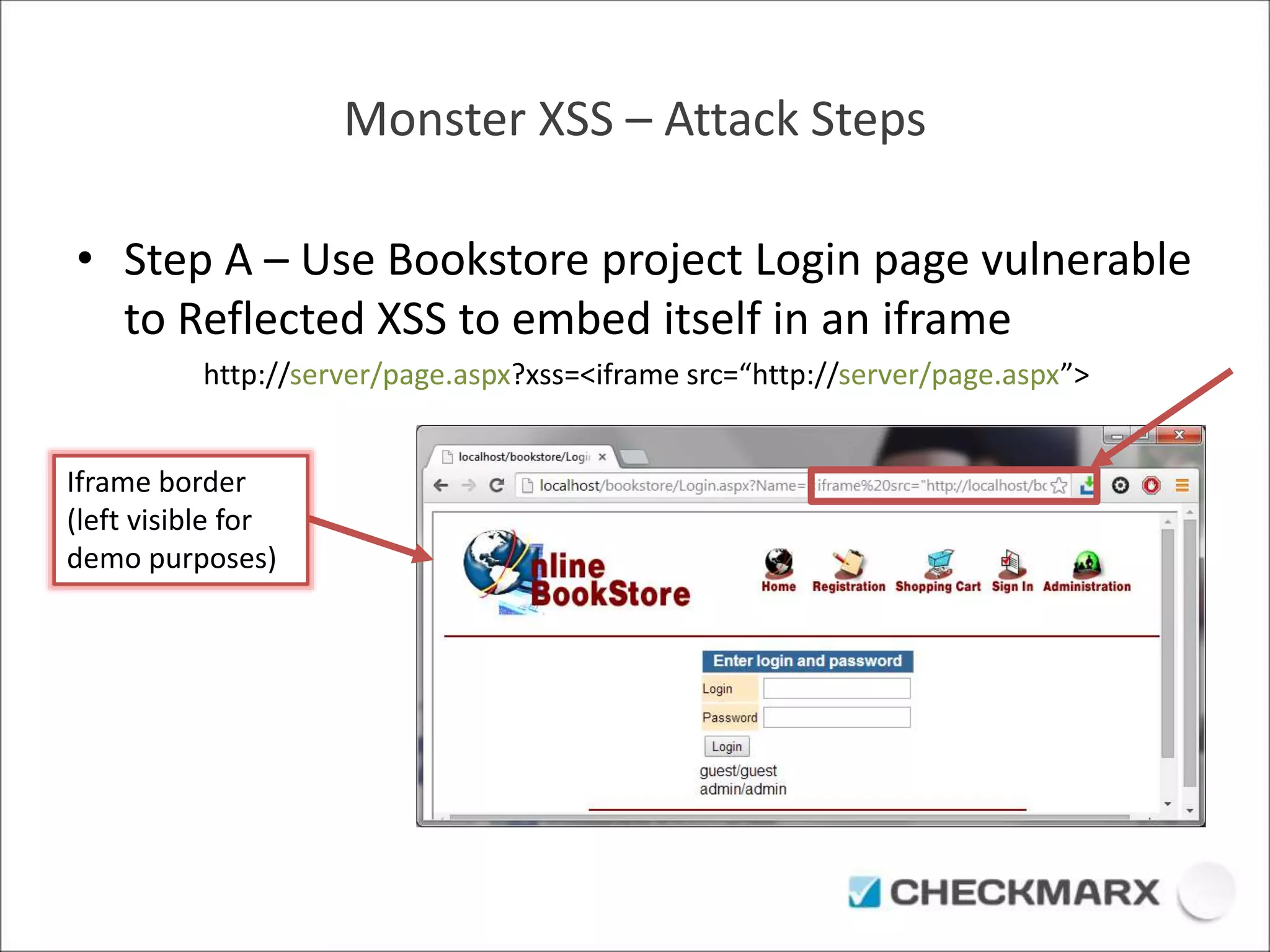
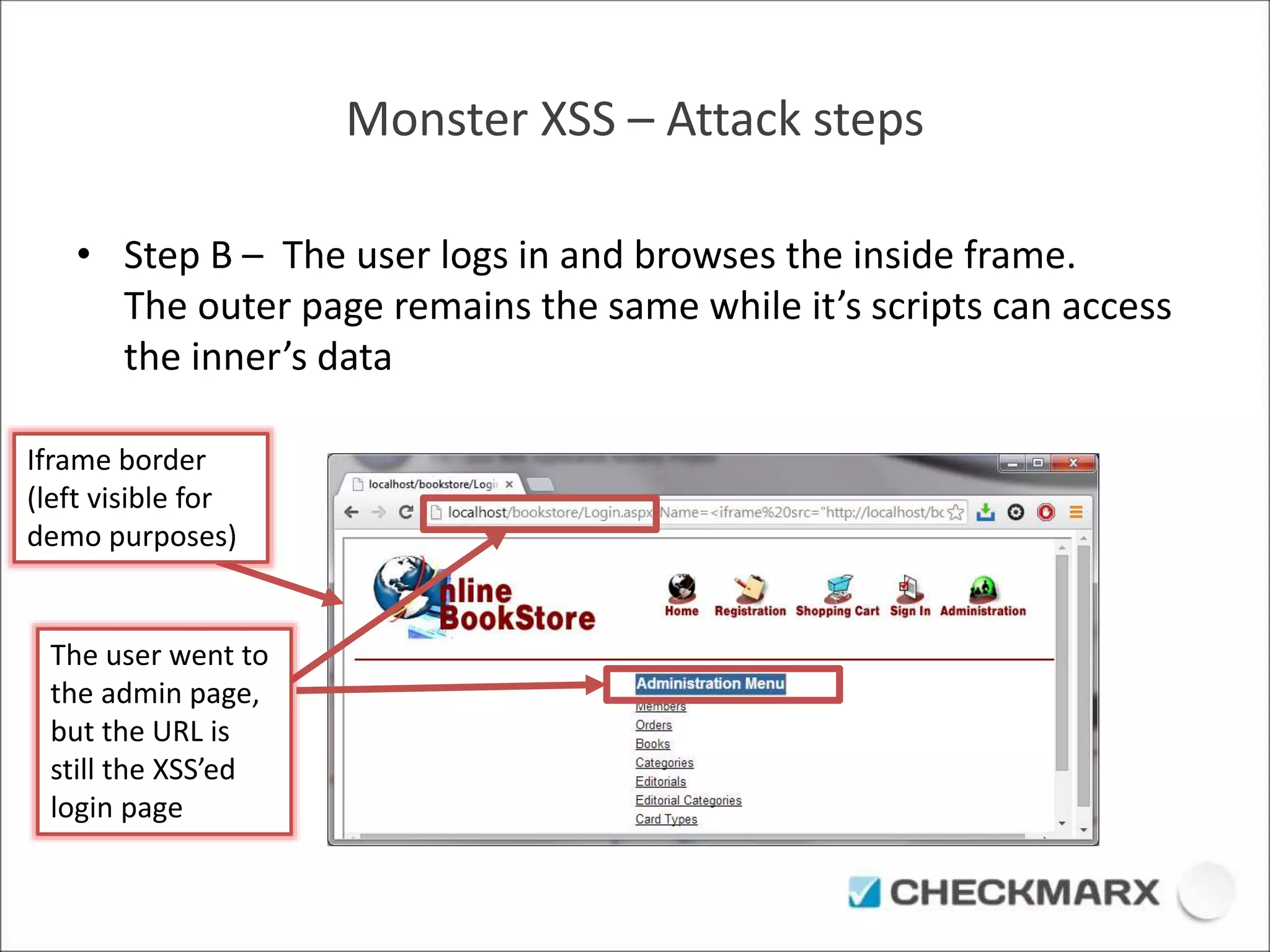
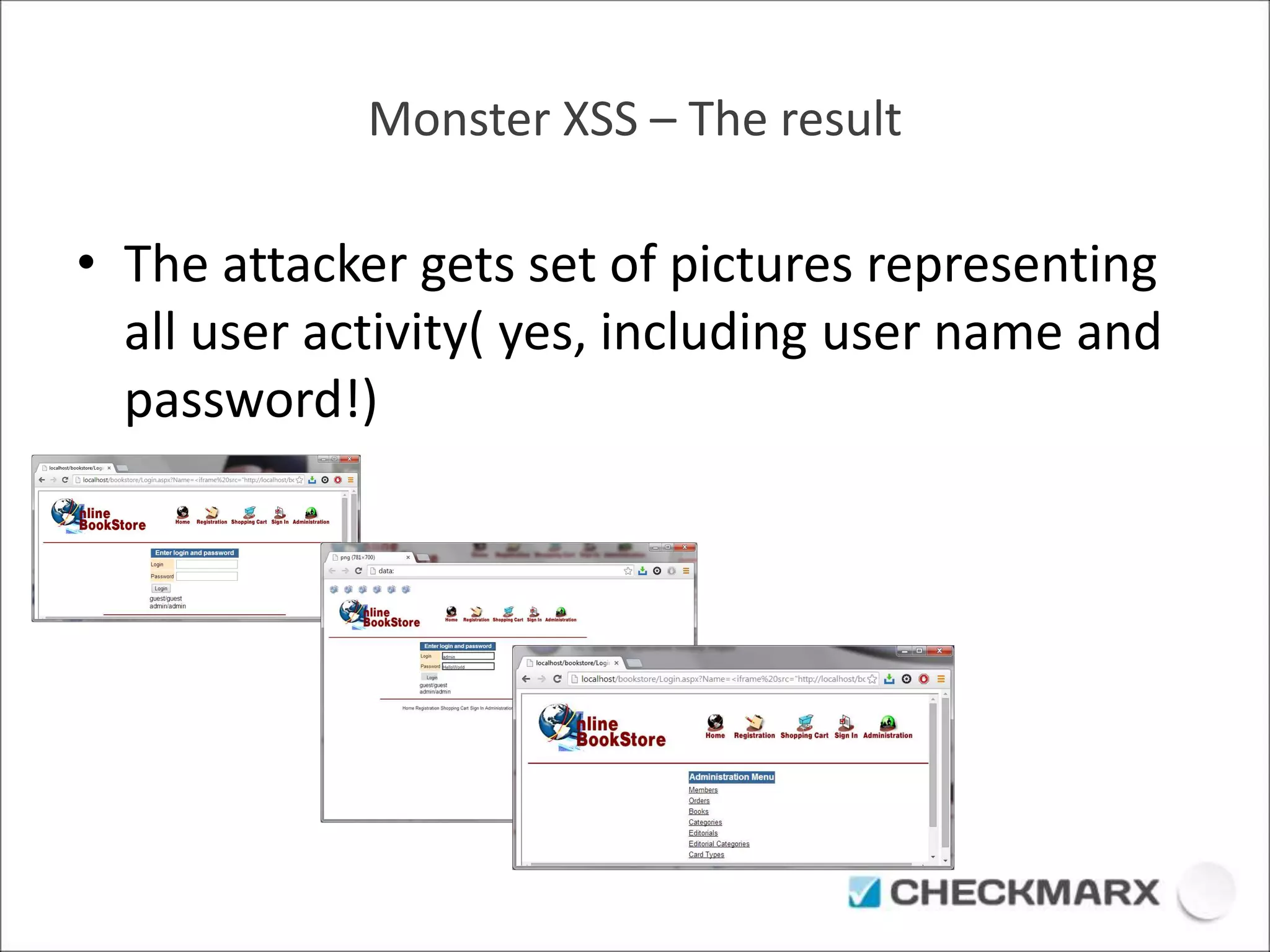
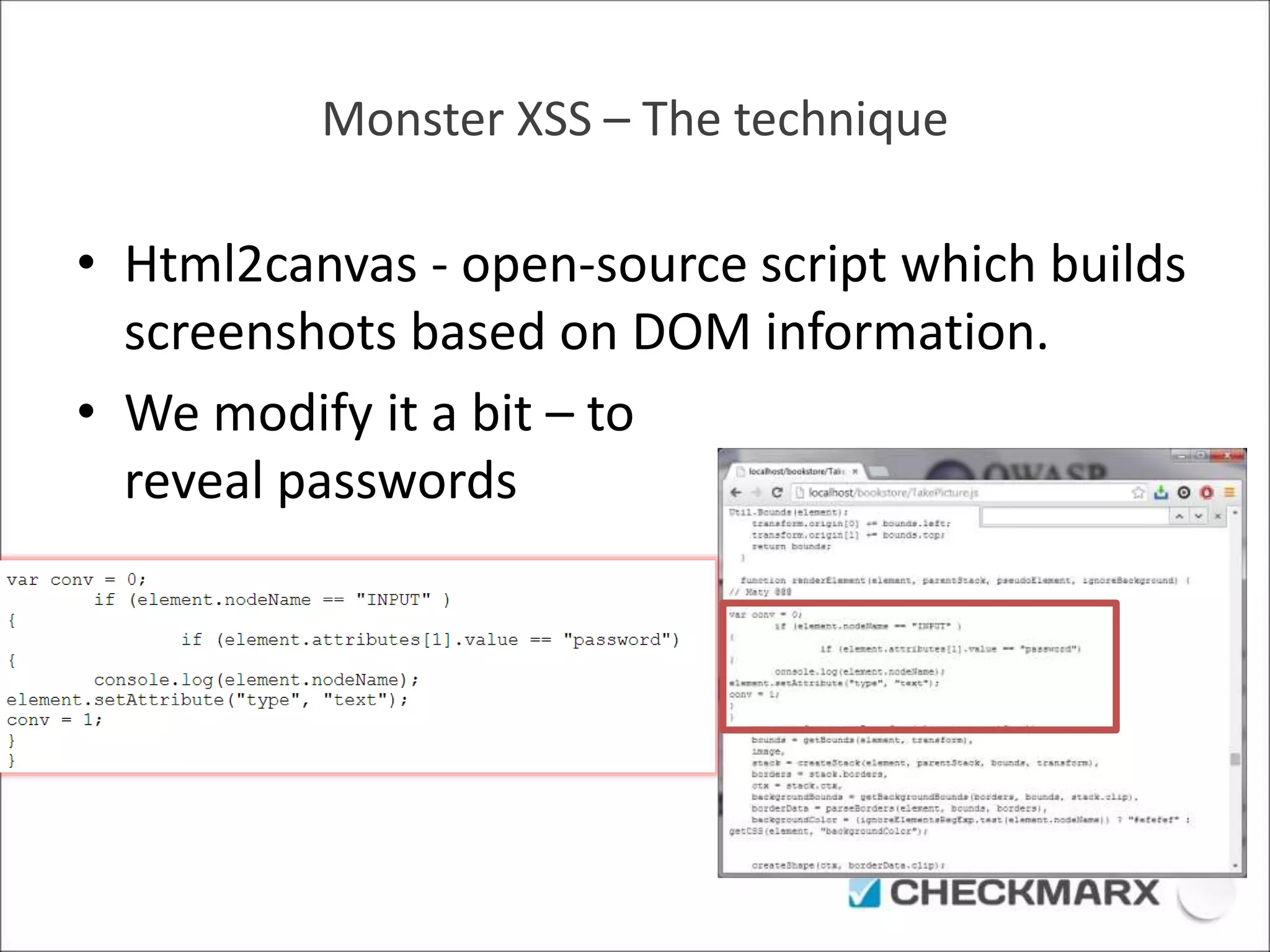
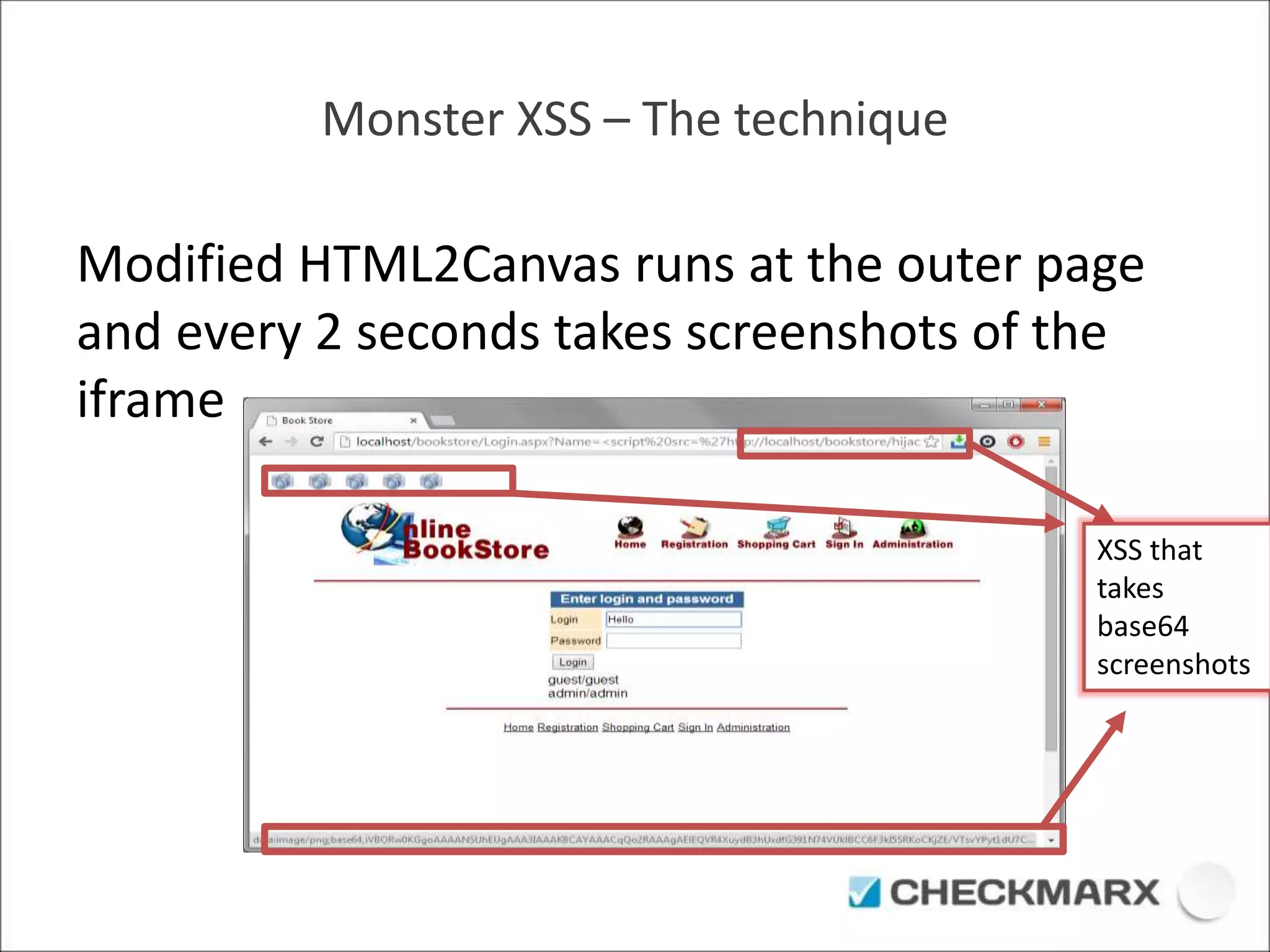
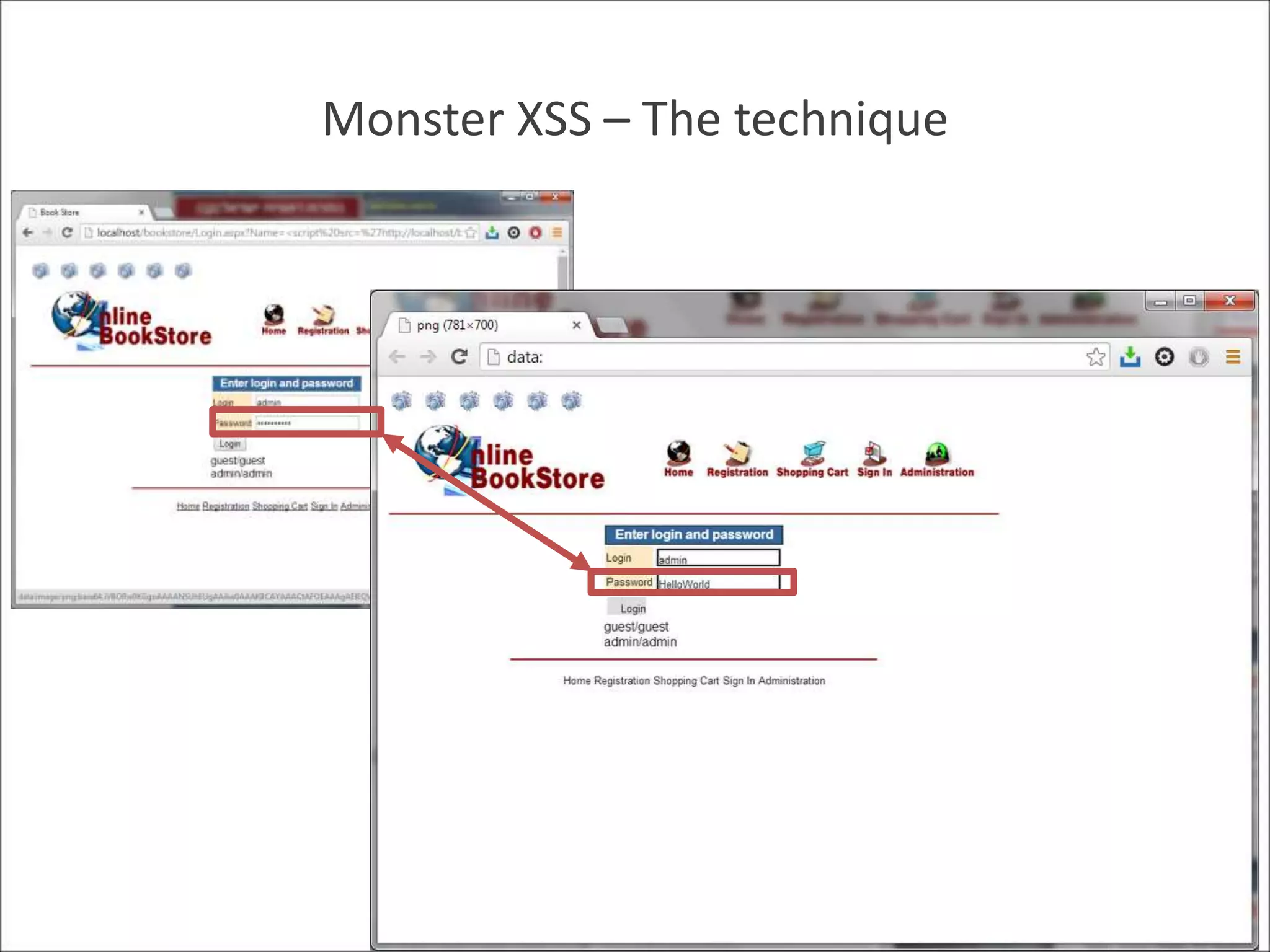
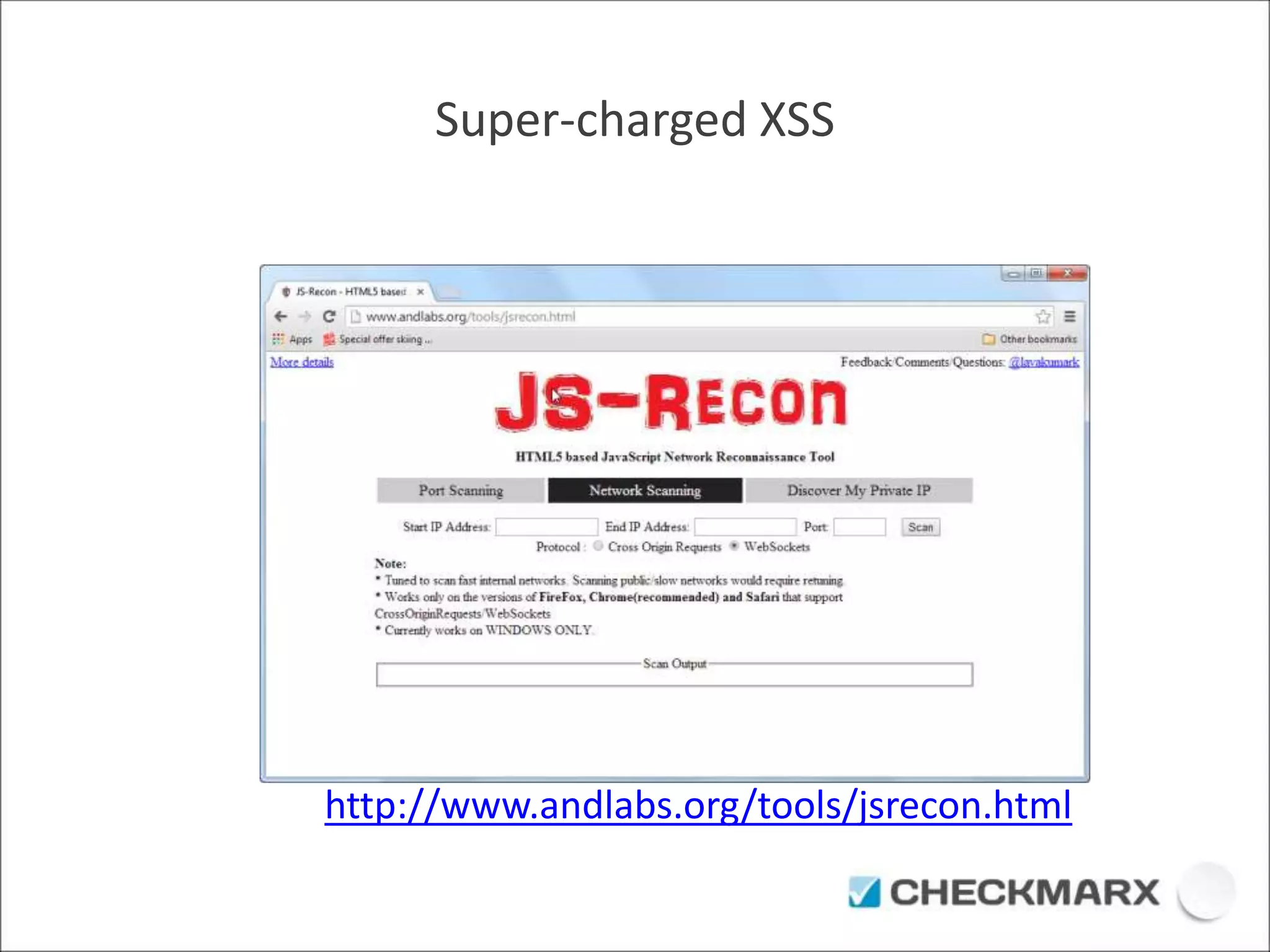
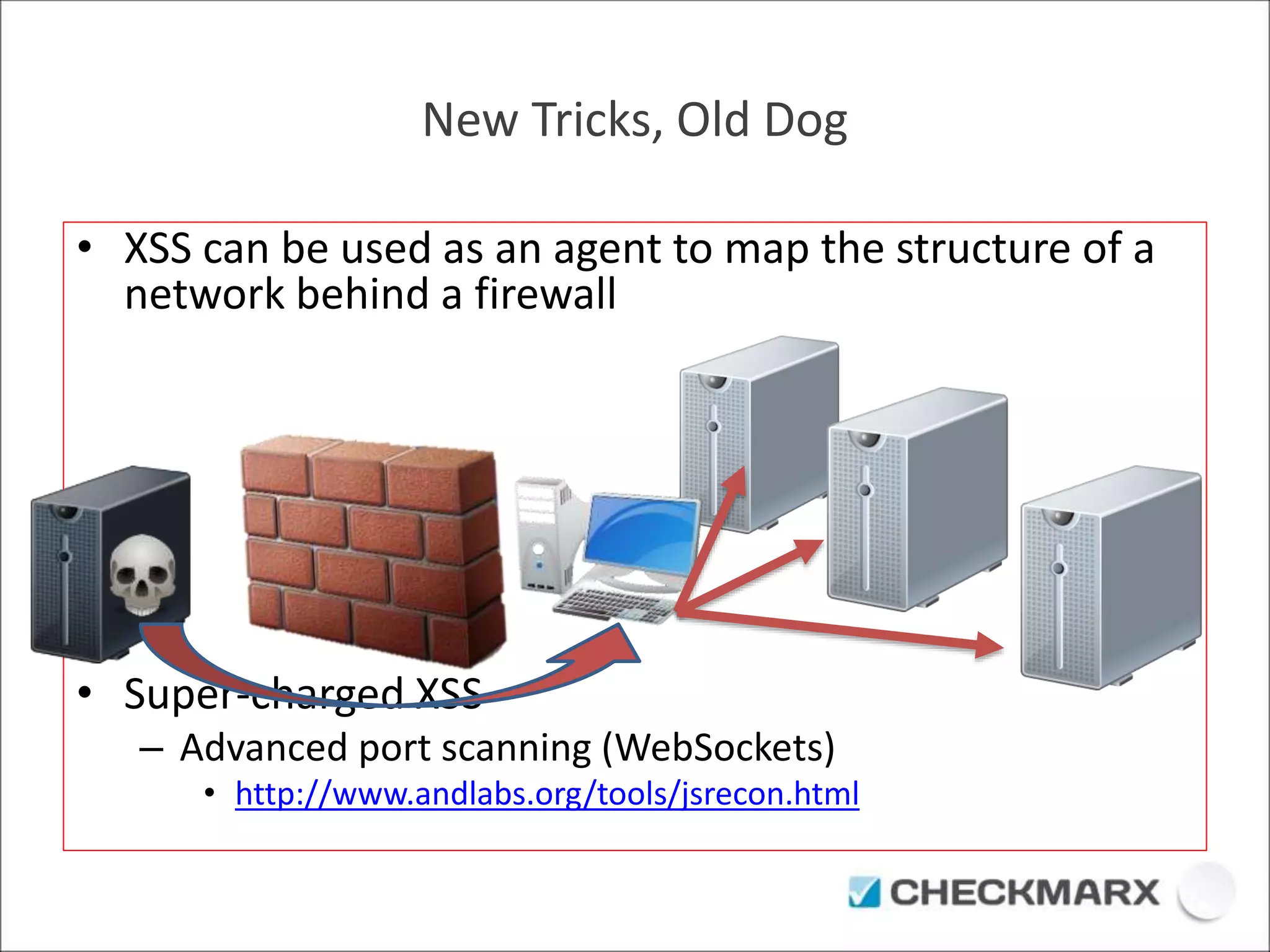
The document discusses security vulnerabilities in JavaScript, particularly focusing on the implications of HTML5 features like sandboxing and the risks associated with cross-site scripting (XSS). It details specific attack methods, such as 'monster XSS,' that exploit these vulnerabilities to capture user data, and emphasizes the importance of securing client-side applications. Recommendations provided include avoiding unnecessary permissions in iframes and maintaining vigilance against XSS attacks.