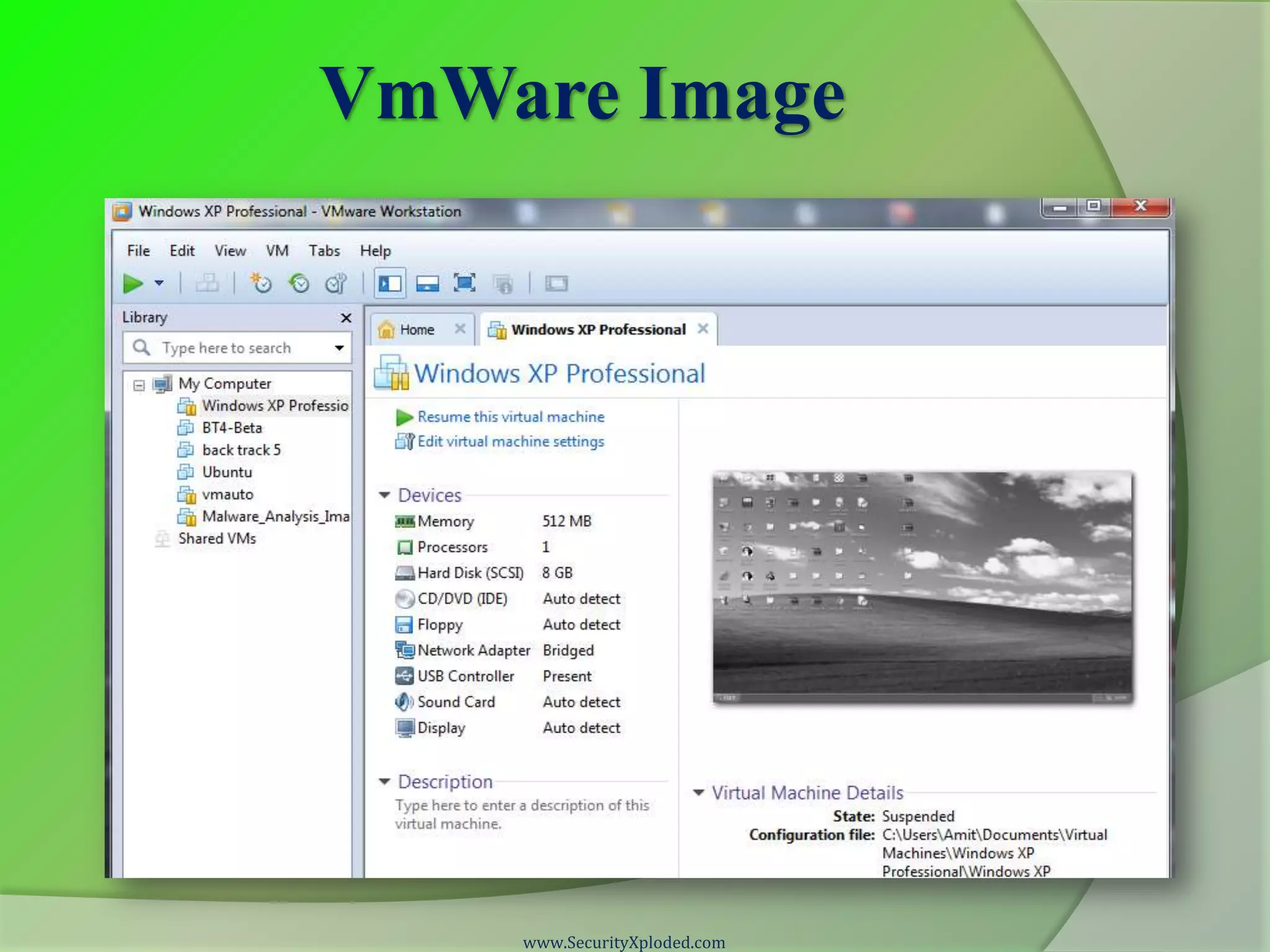
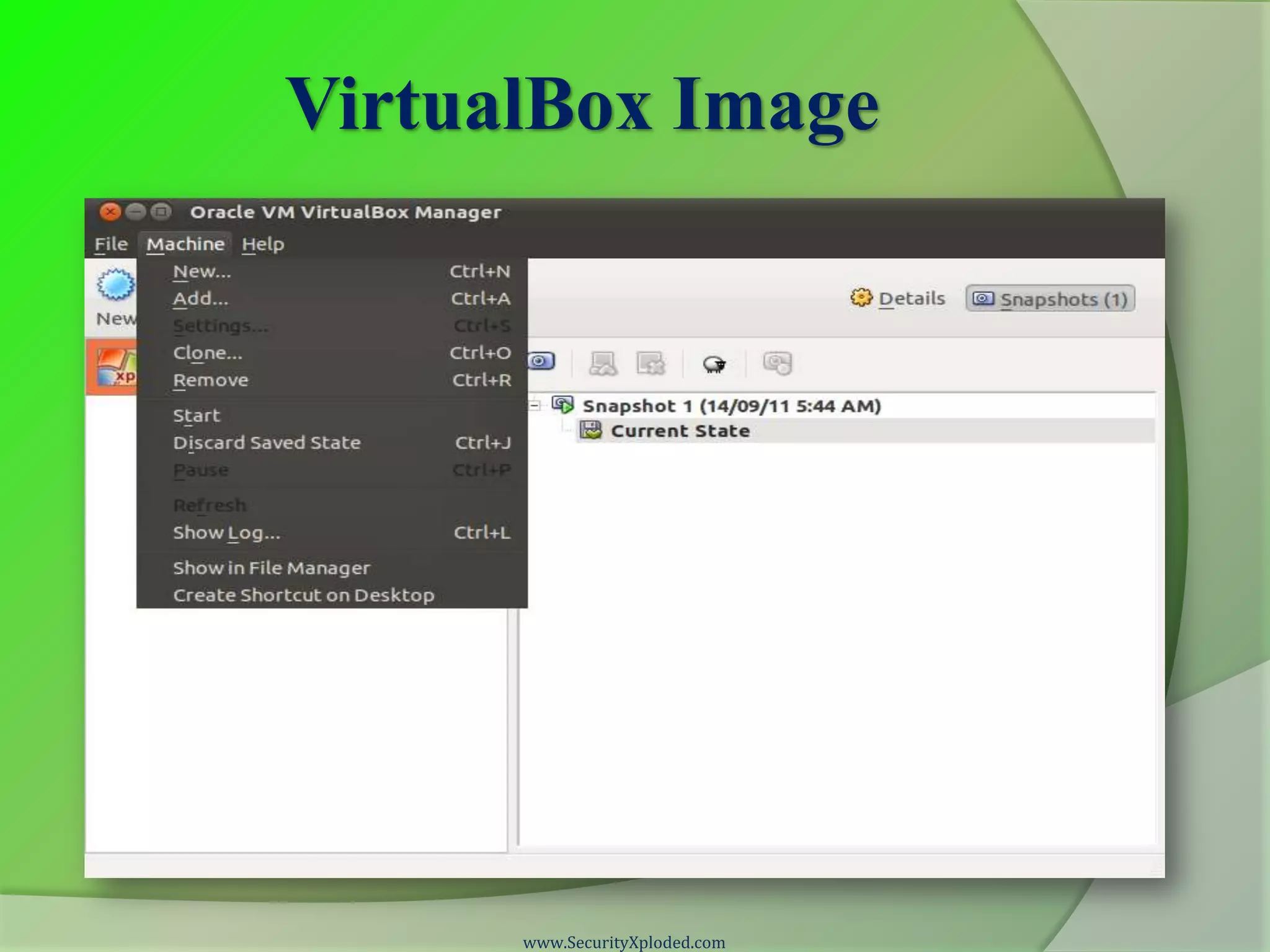
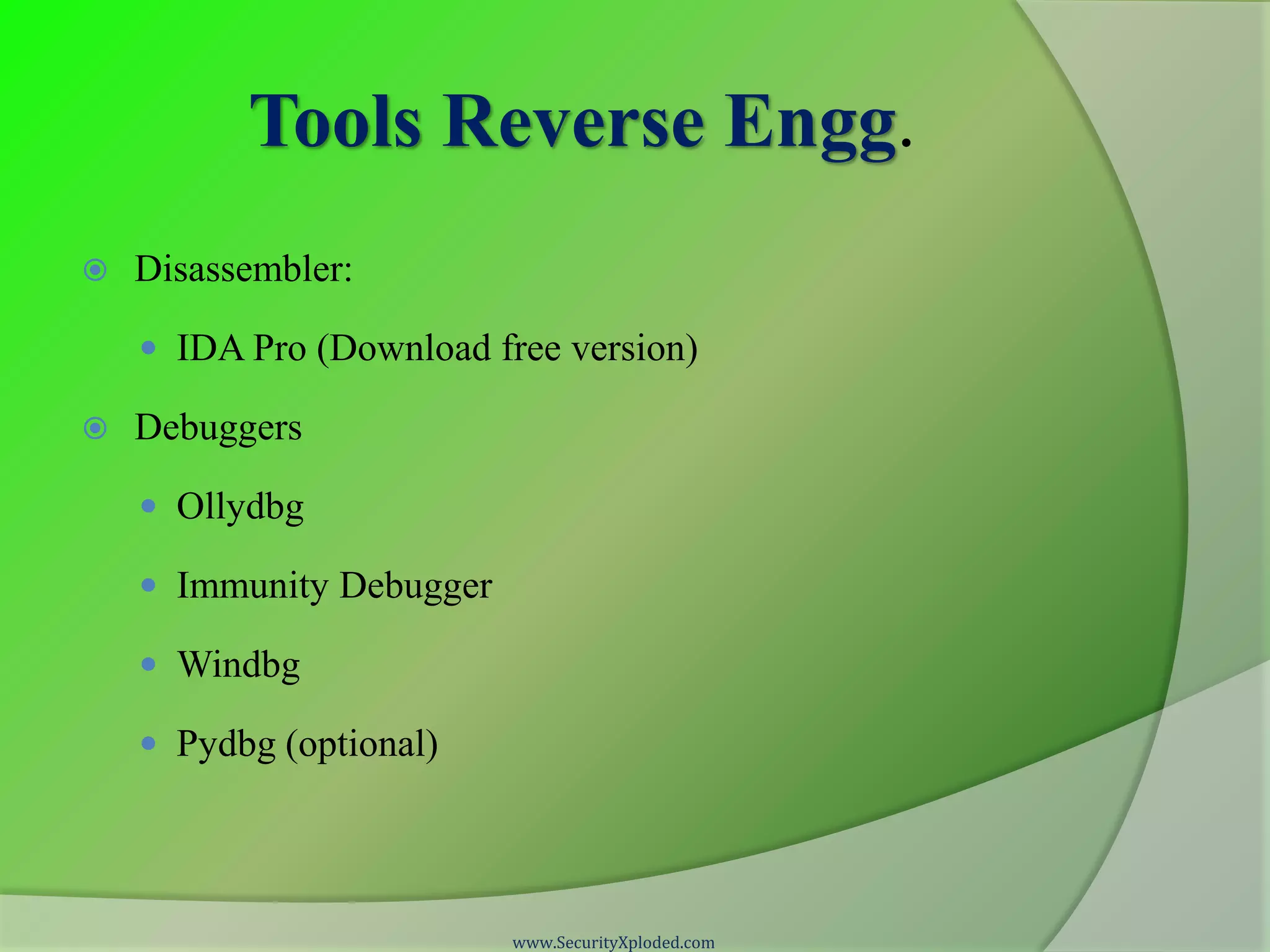
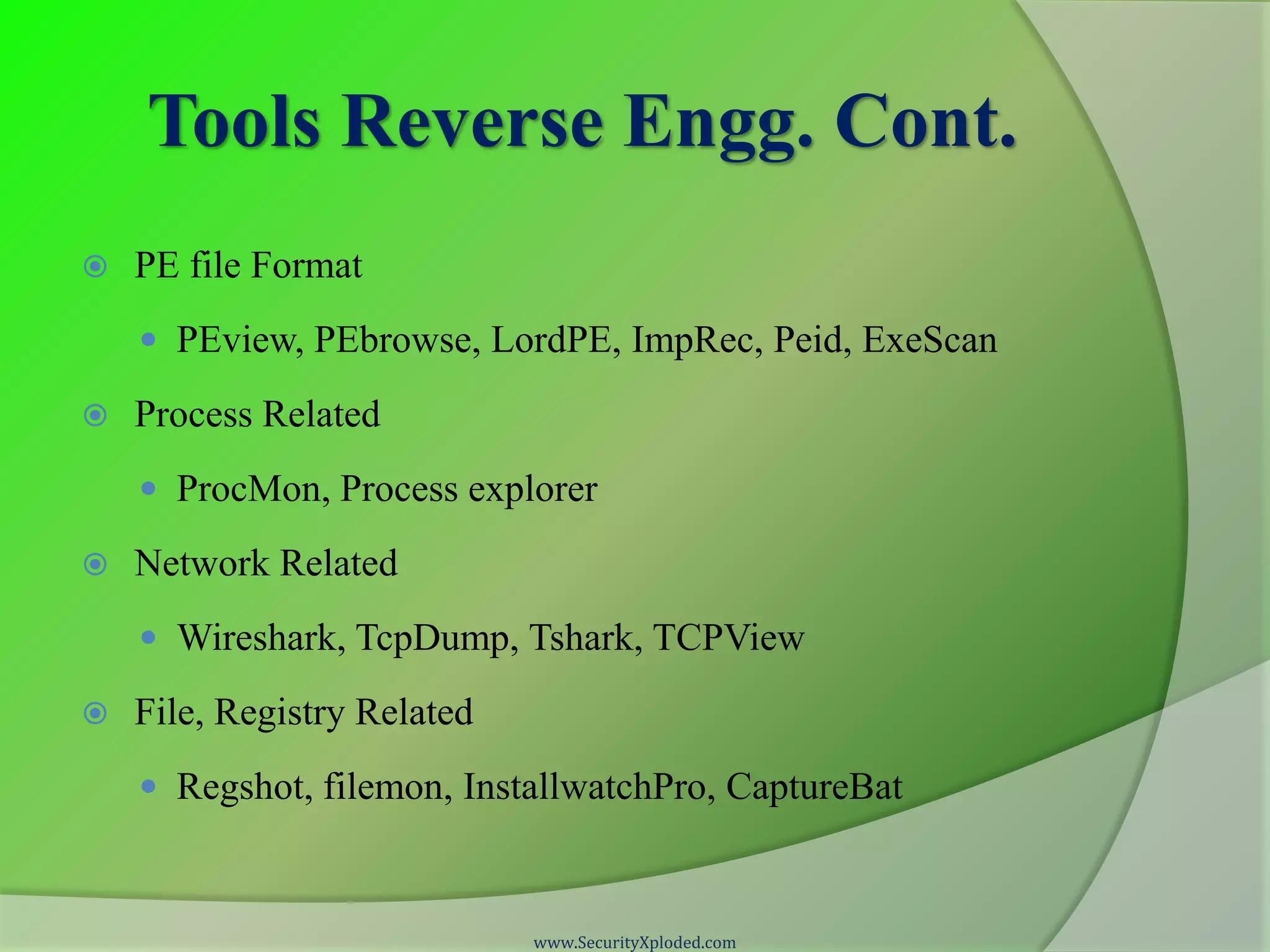
The document provides a disclaimer regarding the content and source code related to reverse engineering and malware analysis training offered by SecurityXploded, specifying that it is presented 'as is' without warranty. It acknowledges the contributions of the trainers and communities, outlines the training program's focus on essential tools and techniques, and lists various tools used for virtualization, development, and reverse engineering. The document serves as a guide for participants in the training course, detailing resources and tools relevant for effective analysis.