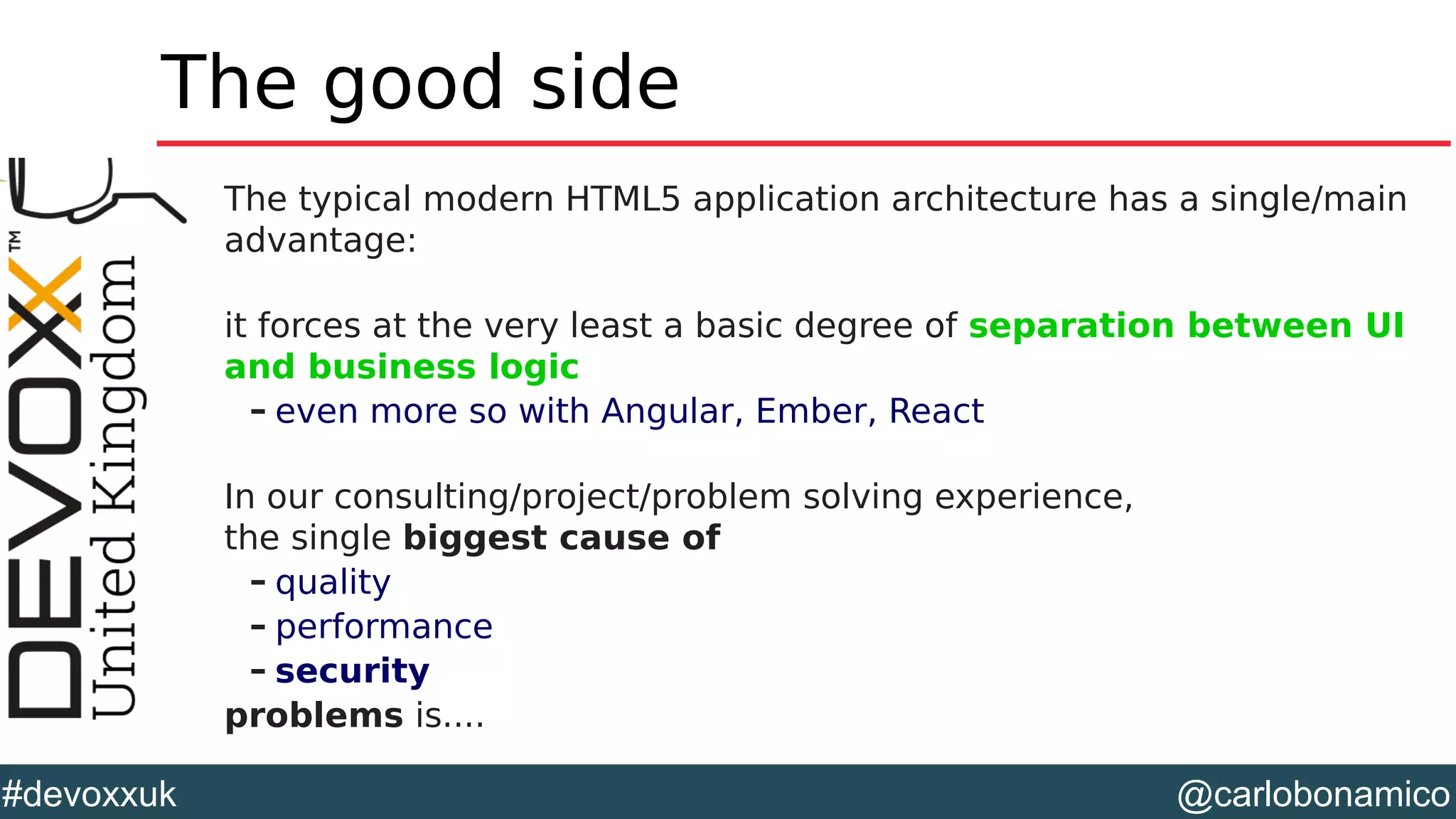
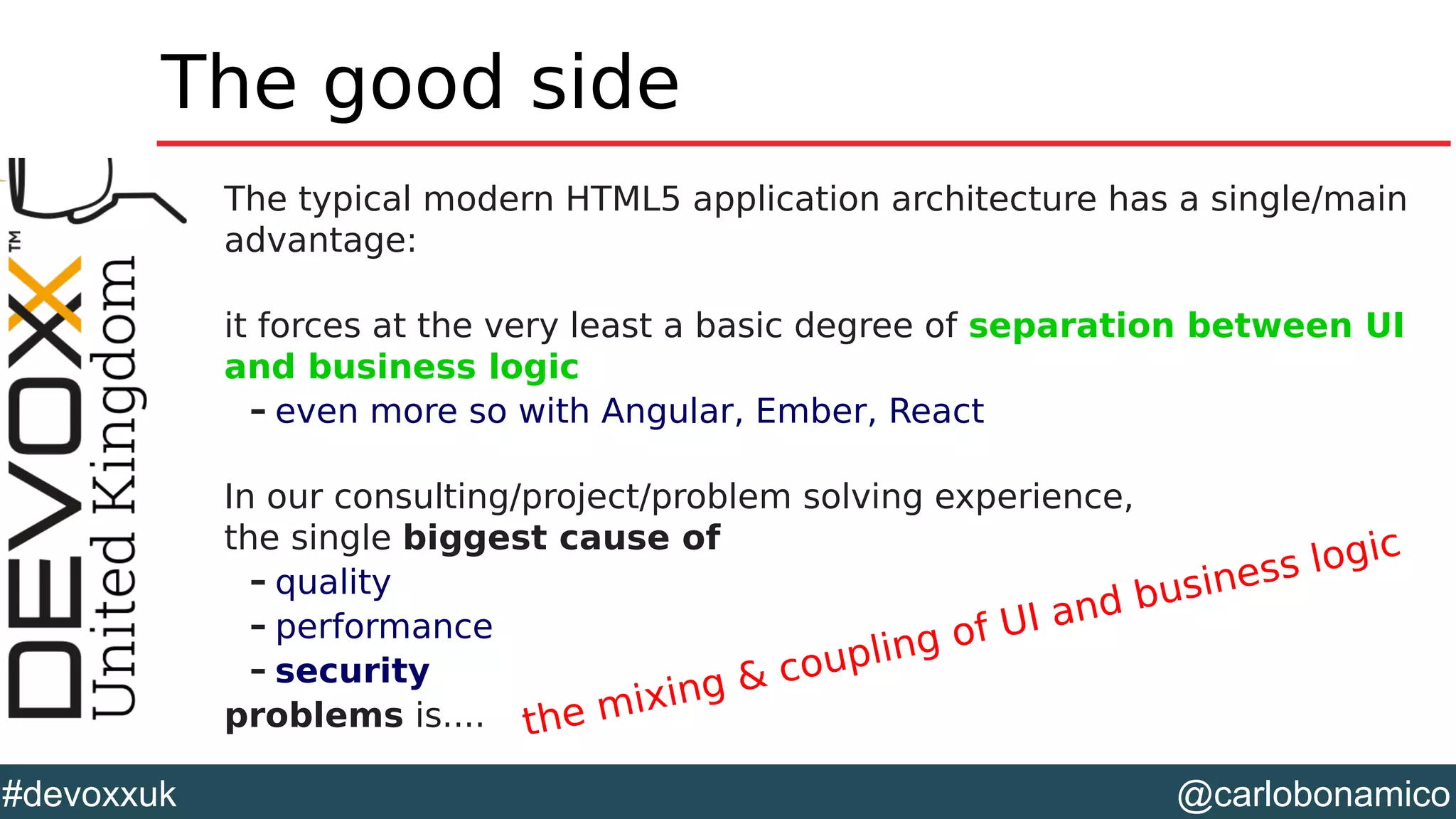
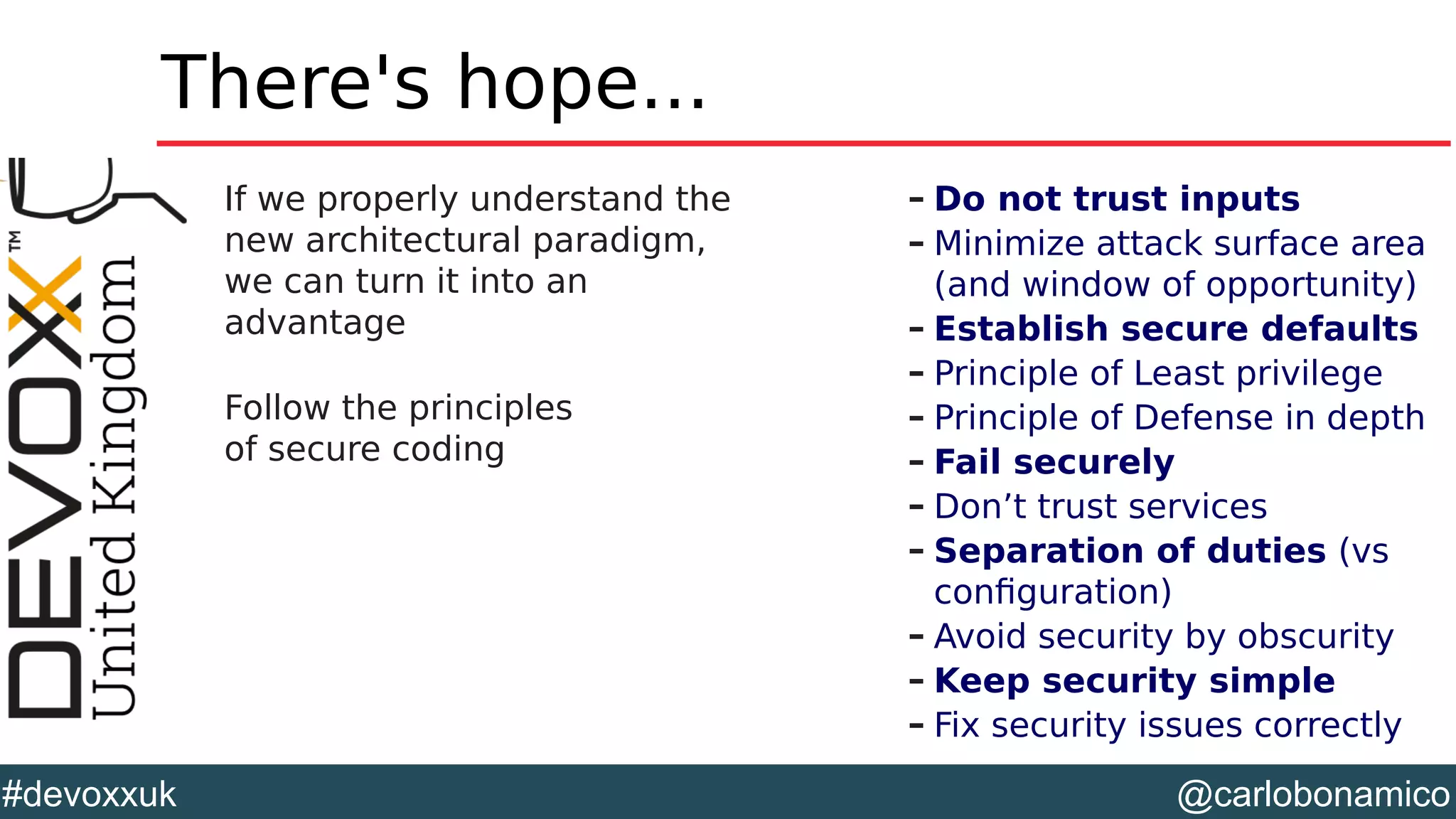
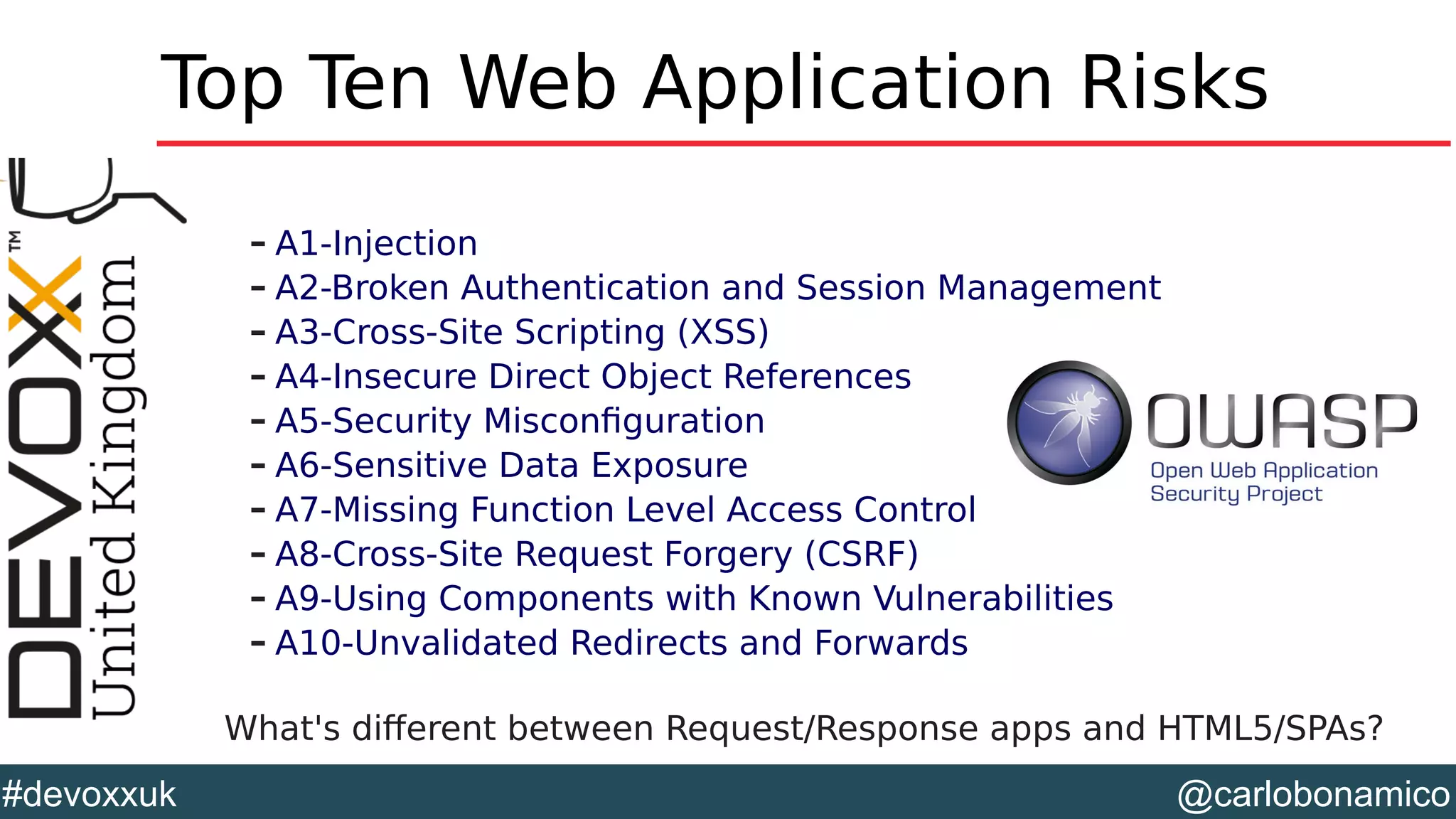
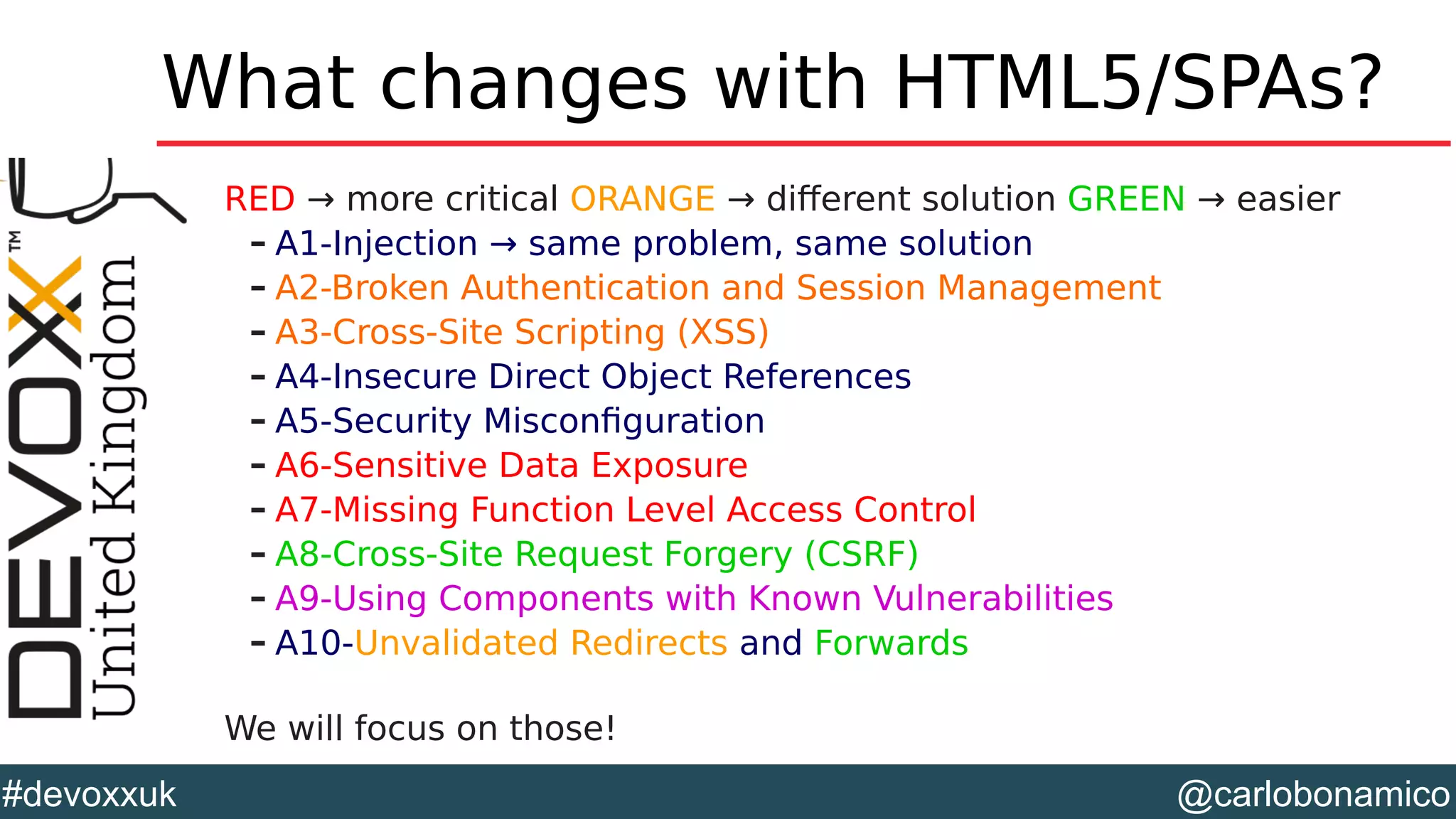
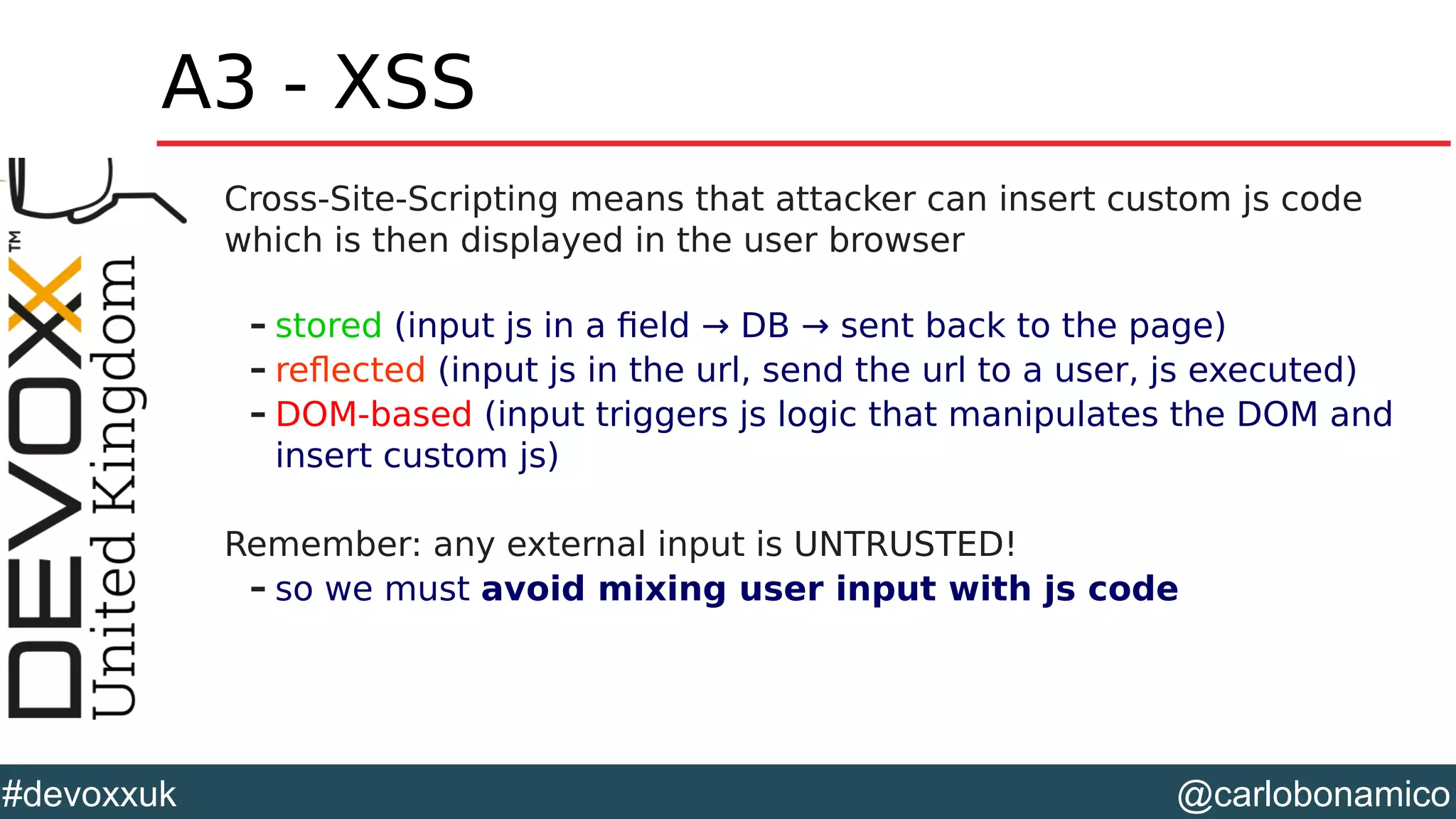
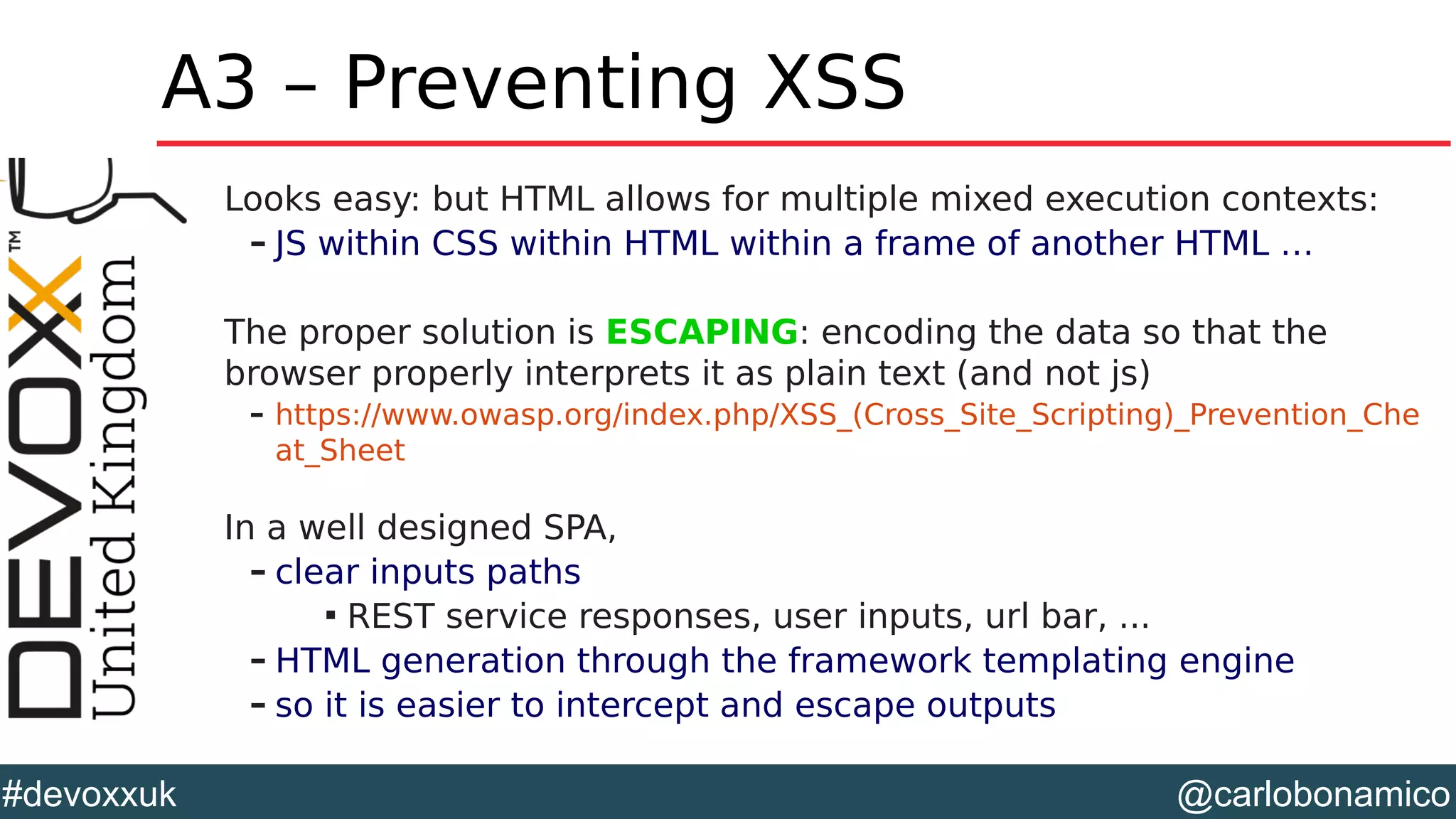
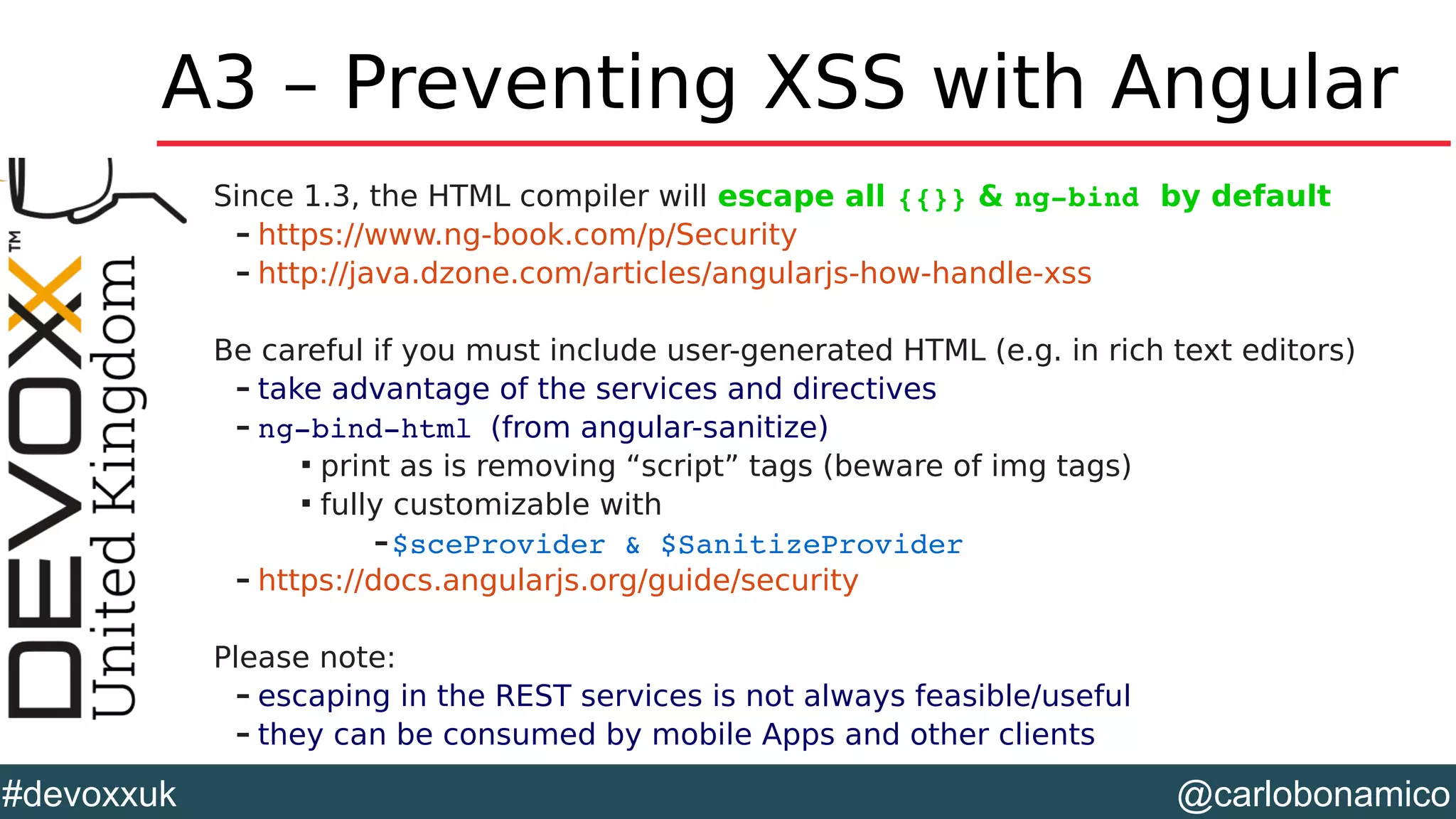
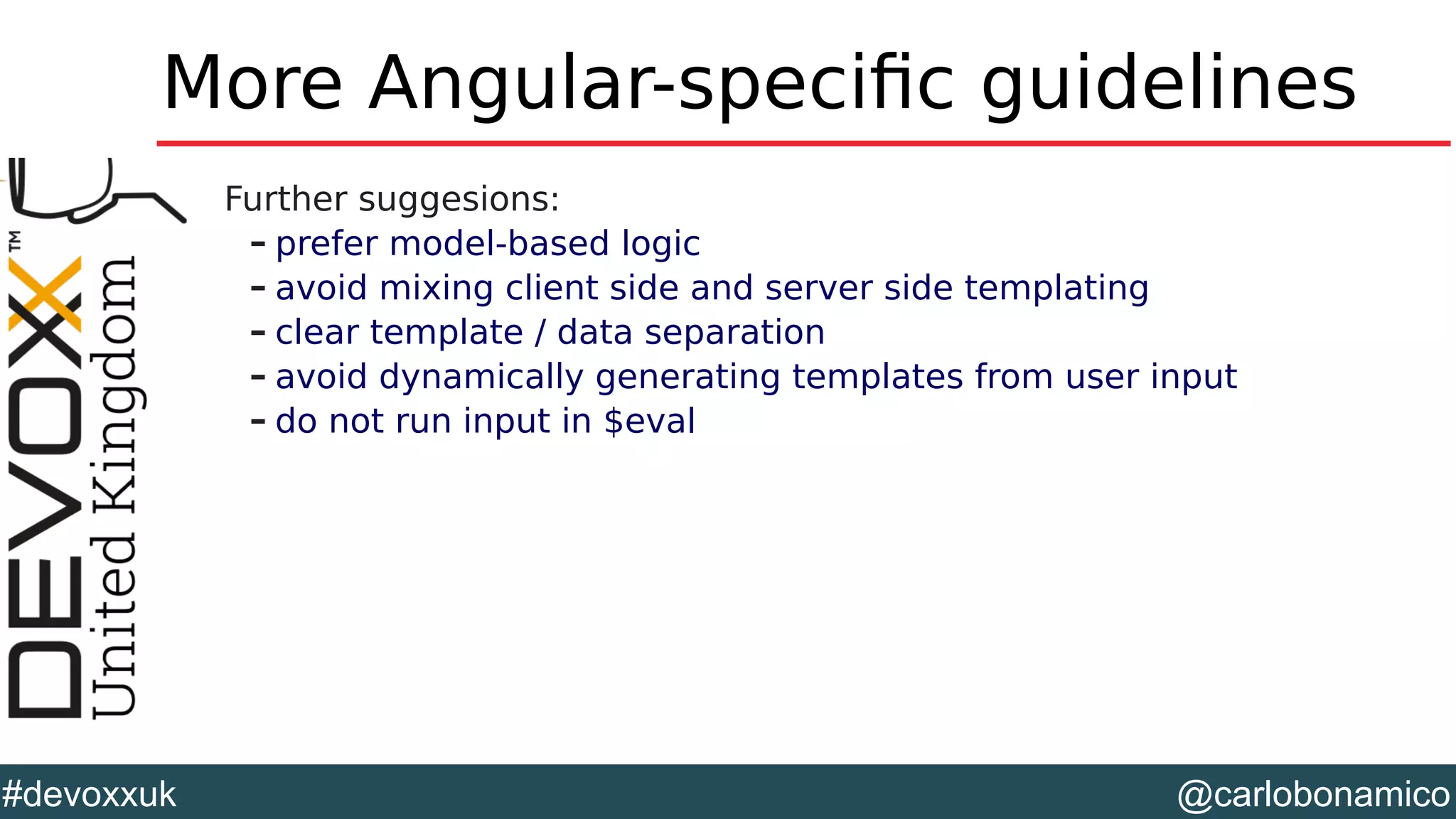
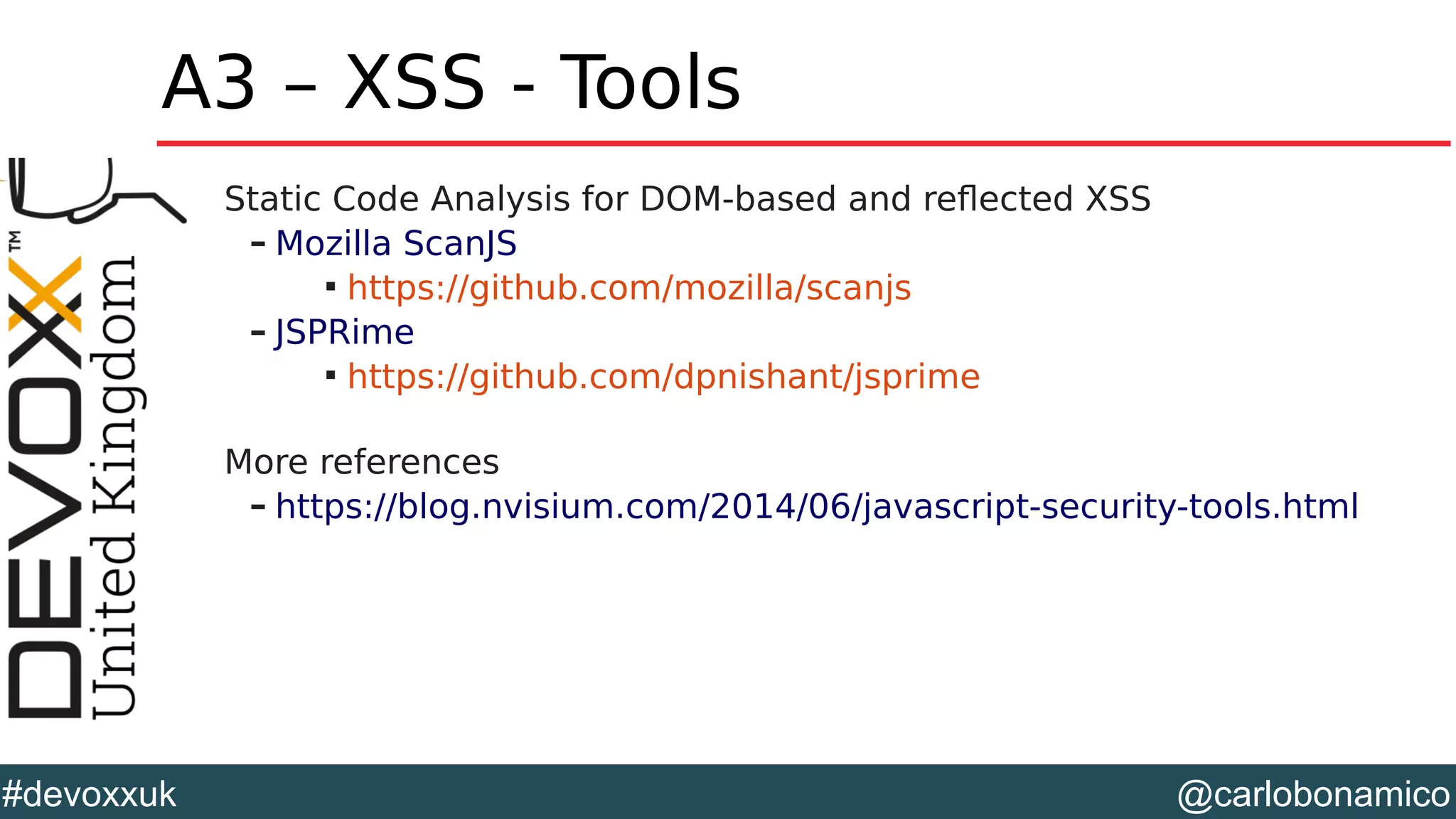
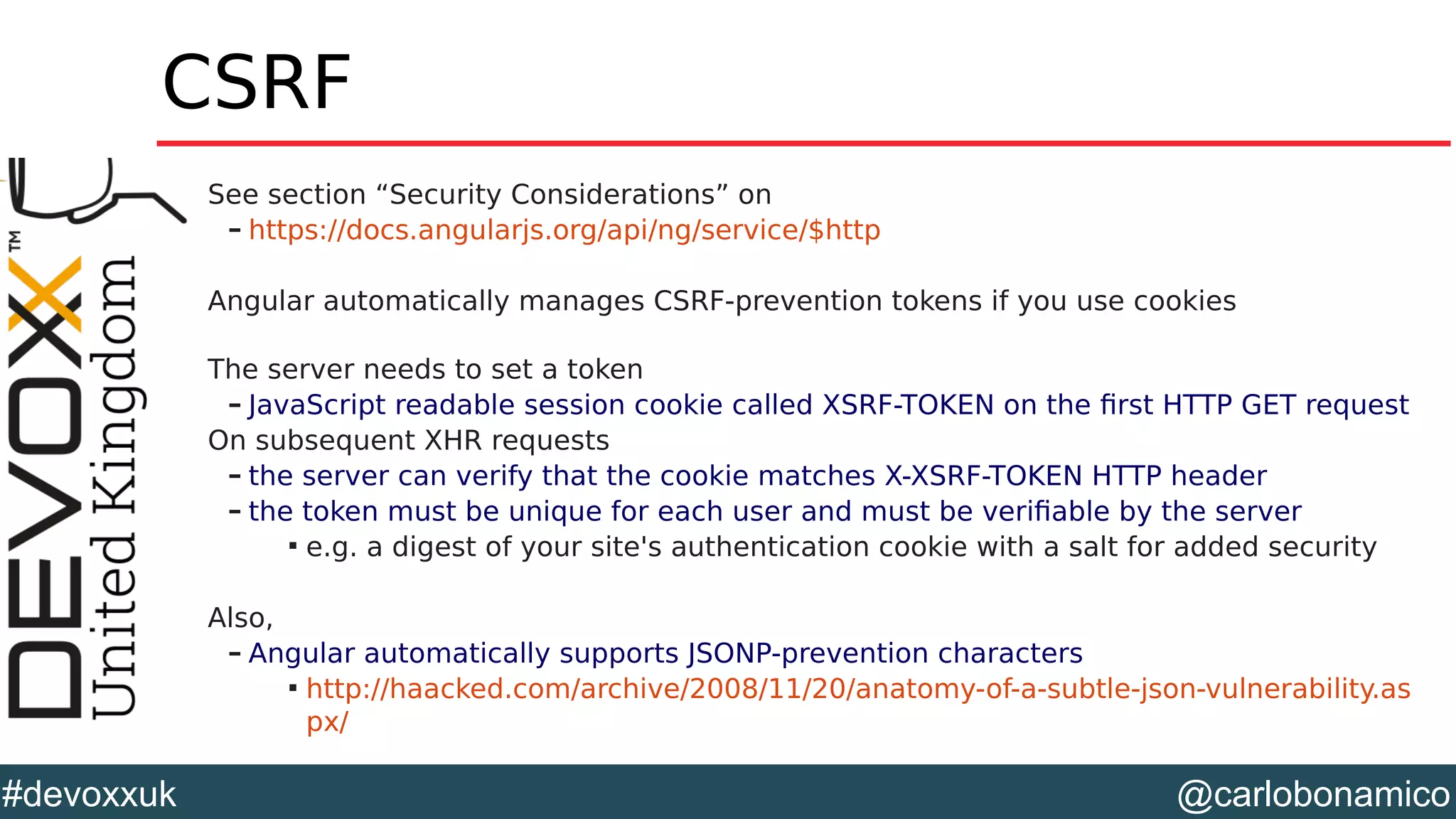
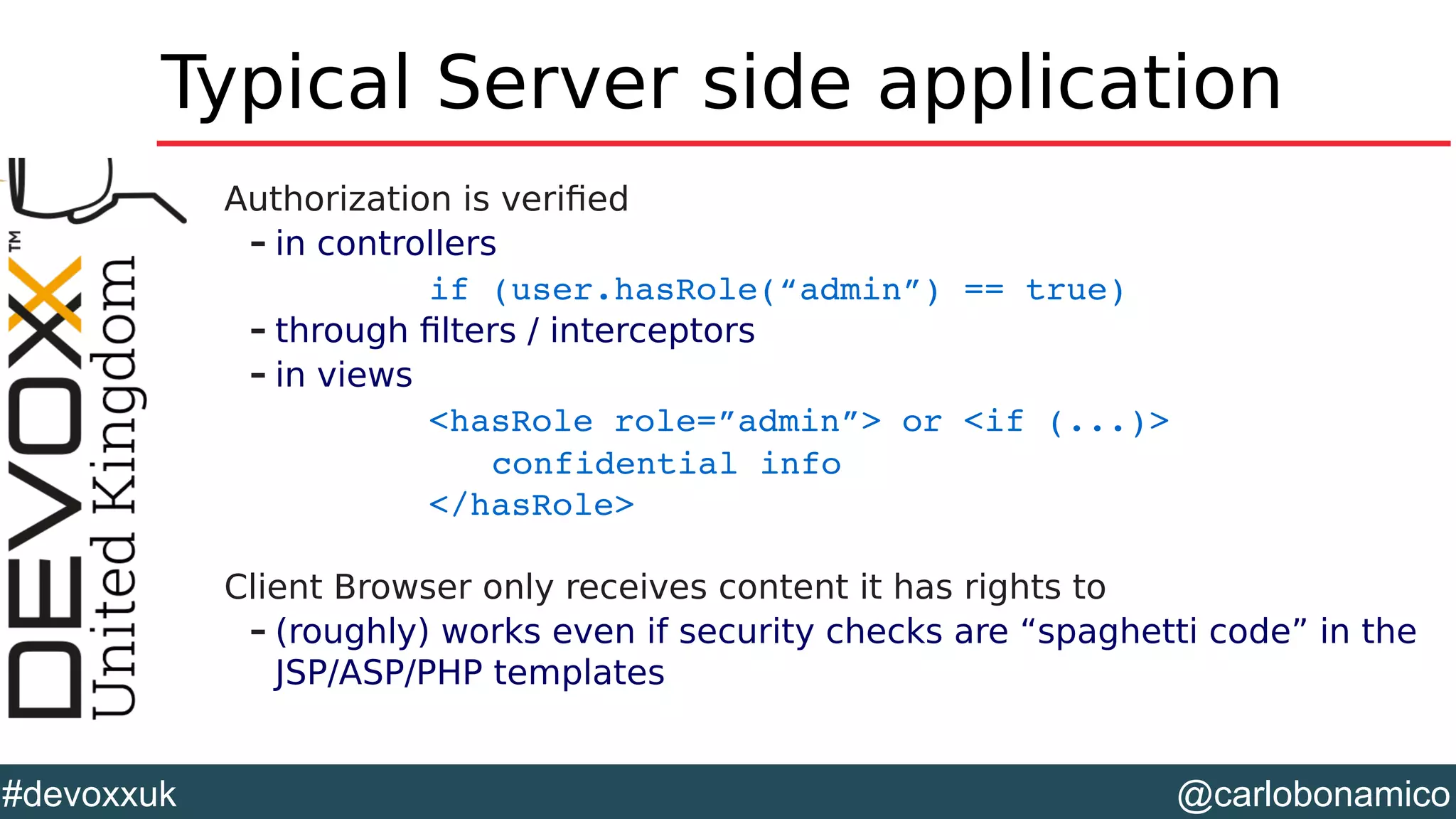
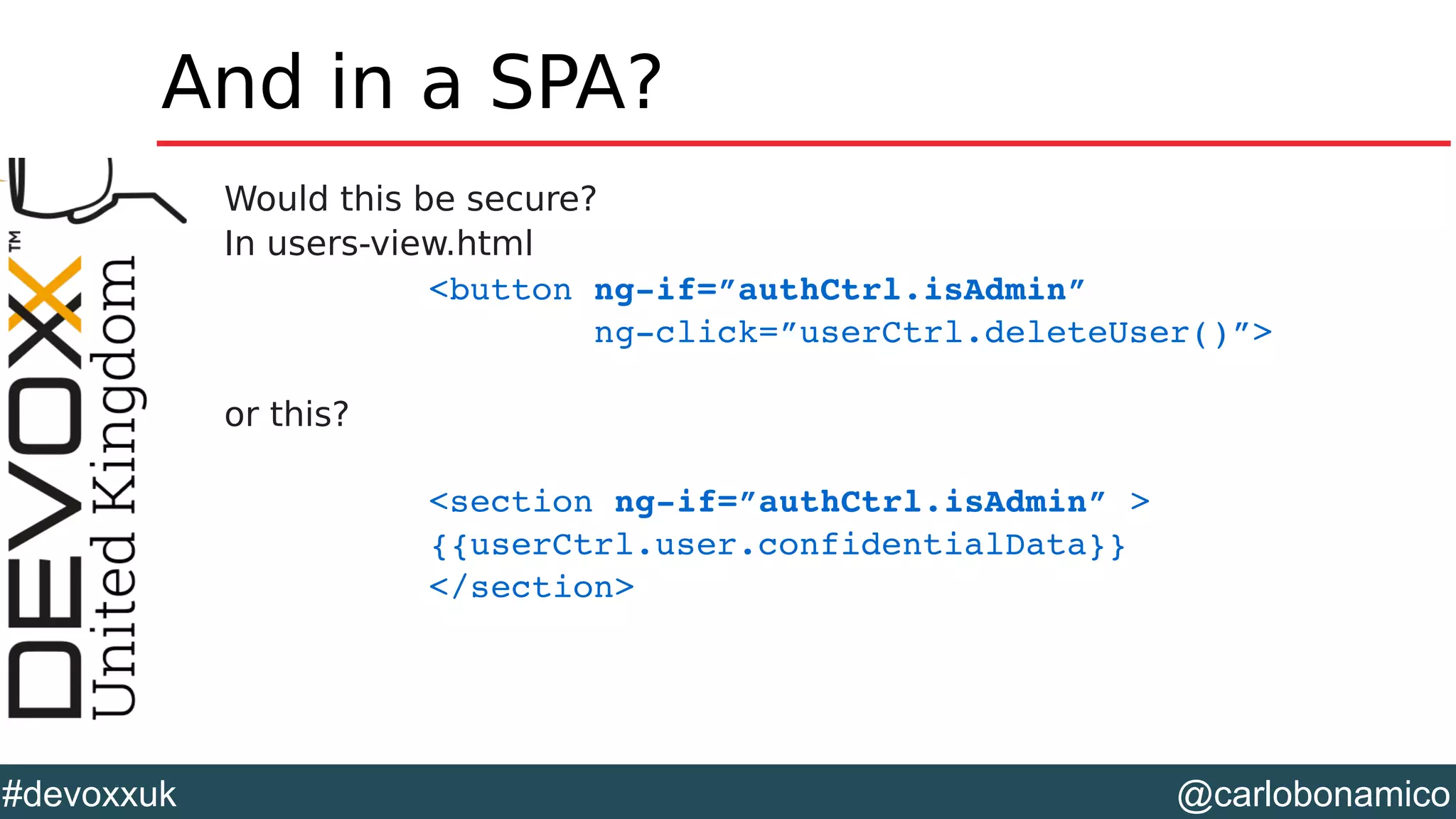
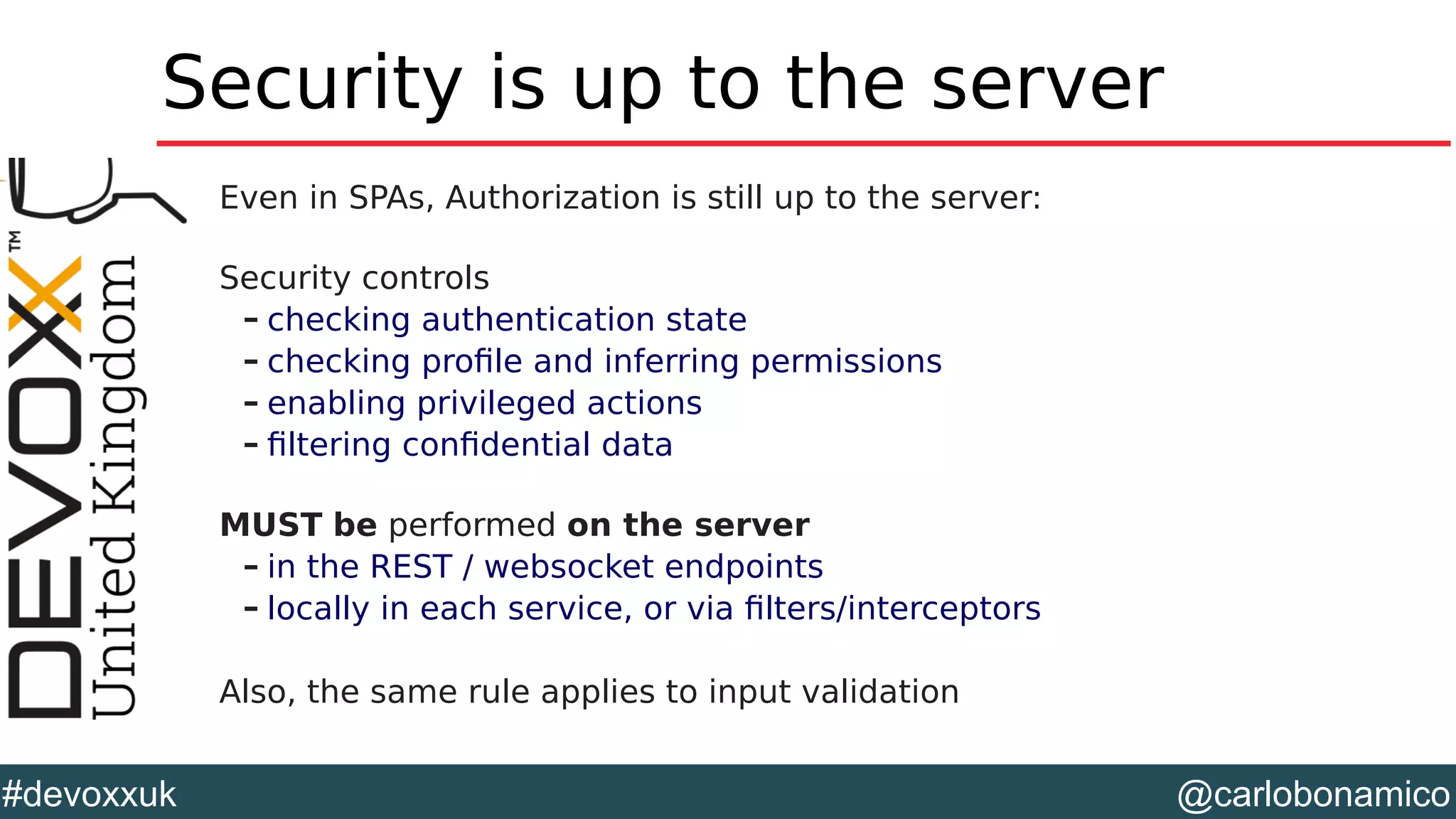
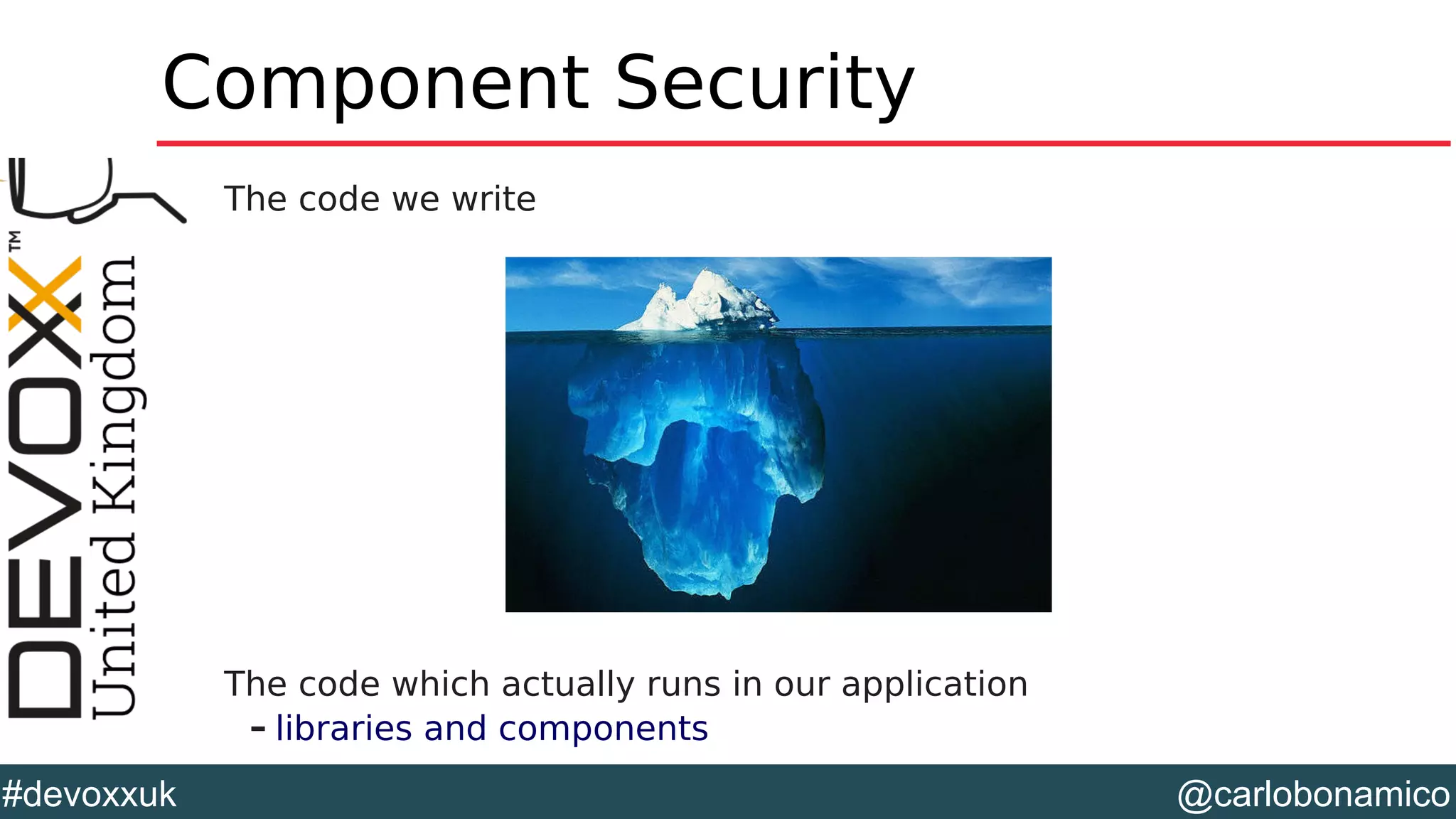
This document discusses the evolving landscape of web application security, particularly in the context of HTML5 and single page applications. It highlights the challenges and risks associated with modern development technologies and emphasizes the importance of secure coding practices to mitigate vulnerabilities, including those listed in the OWASP Top Ten. The talk includes practical examples and tools for implementing security measures in contemporary web applications.


![@carlobonamico#devoxxuk Authentication Client Perform the request – Form based POST $http({ url: '/oauth2/token', method: 'POST', headers: { 'Content-Type': 'application/x-www-form-urlencoded' }, transformRequest: function (obj) { var str = []; for (var p in obj) str.push(encodeURIComponent(p) + "=" + encodeURIComponent(obj[p])); return str.join("&"); }, data: { username: credentials.username, password: credentials.password, } })](https://image.slidesharecdn.com/devoxx-uk-2015-bonamicowebapplicationsecurity-html5-full-150618083904-lva1-app6892/75/Web-Application-Security-Reloaded-for-the-HTML5-era-42-2048.jpg)
![@carlobonamico#devoxxuk Integrating with angular-jwt Specify Token retrieval function angular.module('myApp') .config(function Config($httpProvider, jwtInterceptorProvider) { jwtInterceptorProvider.tokenGetter = ['currentToken', function(currentToken) { return currentToken.jwt; //or return localStorage.getItem('id_token'); }]; Register interceptor $httpProvider.interceptors.push('jwtInterceptor'); });](https://image.slidesharecdn.com/devoxx-uk-2015-bonamicowebapplicationsecurity-html5-full-150618083904-lva1-app6892/75/Web-Application-Security-Reloaded-for-the-HTML5-era-45-2048.jpg)

![@carlobonamico#devoxxuk Checking dependecies for vulns On the client side – http://retirejs.github.io/retire.js/ npm install g retire ; retire –path src – also available as ZAP & mvn plugin mvn com.h3xstream.retirejs:retirejsmaven plugin:scan On the server side – OWASP Dependency Check https://github.com/jeremylong/DependencyCheck dependencycheck.sh app Testing out . scan [path to jar files to be scanned] mvn org.owasp:dependencycheckmaven](https://image.slidesharecdn.com/devoxx-uk-2015-bonamicowebapplicationsecurity-html5-full-150618083904-lva1-app6892/75/Web-Application-Security-Reloaded-for-the-HTML5-era-71-2048.jpg)